Explore our posts
-

Three key lessons from unauthorized access to Okta’s support system
Learn more -

Veza @ Gartner Symposium — October 15-19
Learn more -
Disrupting Breaches and Advancing InfoSec with David Tyburski | Ep 2
Learn more -
Why Veza, Why Now?
Learn more -
Identity Targeting: A Growing Threat with Rachel Wilson | Ep 1
Learn more -
Welcome to the Identity Radicals Podcast
Learn more
-
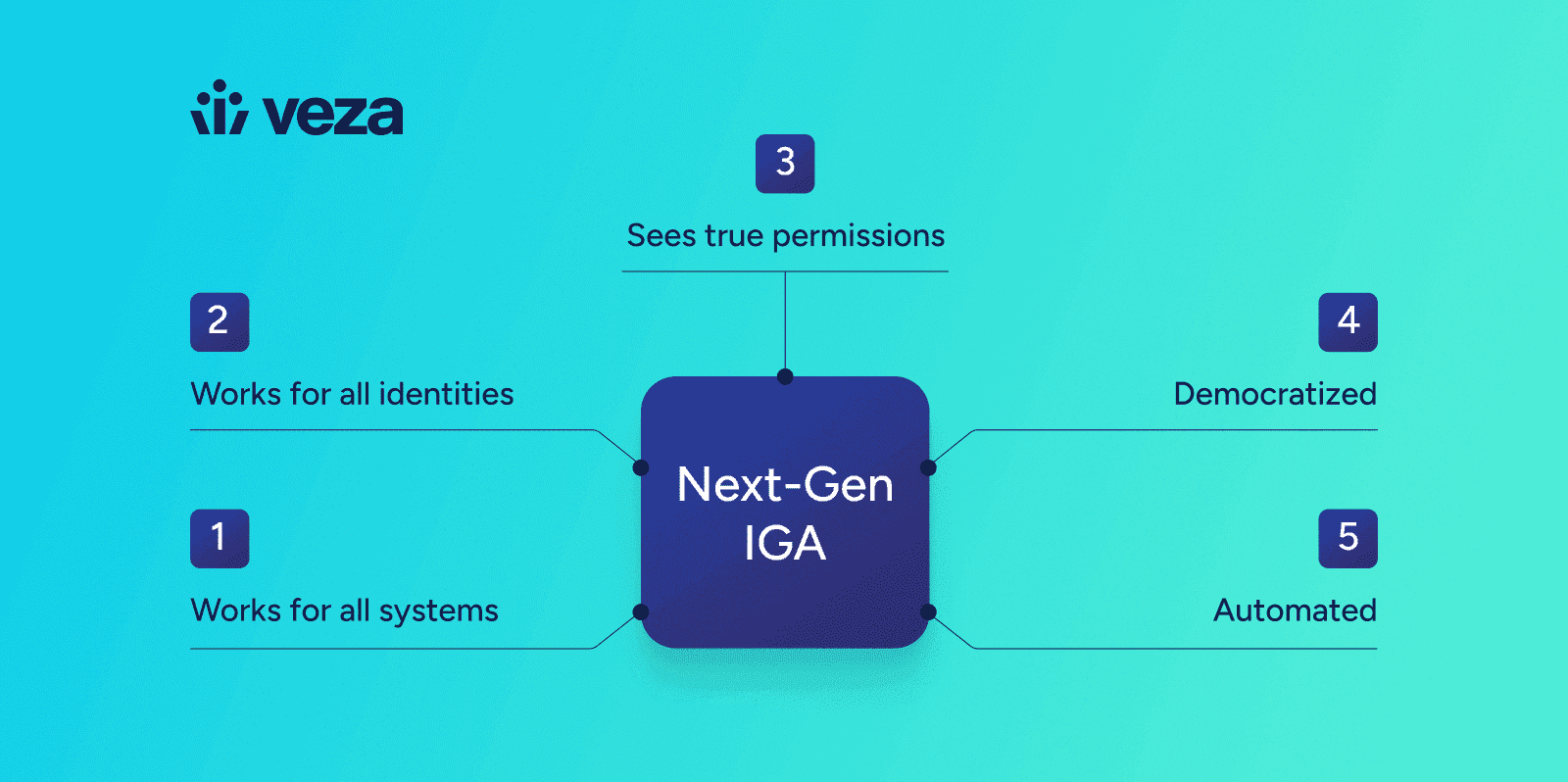
The Five Tenets of Next-Gen IGA
Learn more -
Why Veza, Why Now?
Learn more -

Veza @ Fal.Con 2023
Learn more -
Veza Secures Strategic Investment from Capital One Ventures and ServiceNow Ventures to Accelerate Identity Security
Learn more -
Veza @ Blackstone: Modernizing IGA with Automation and Intelligence
Learn more -
Welcome, Phil Venables, to the Veza Board of Directors!
Learn more
-
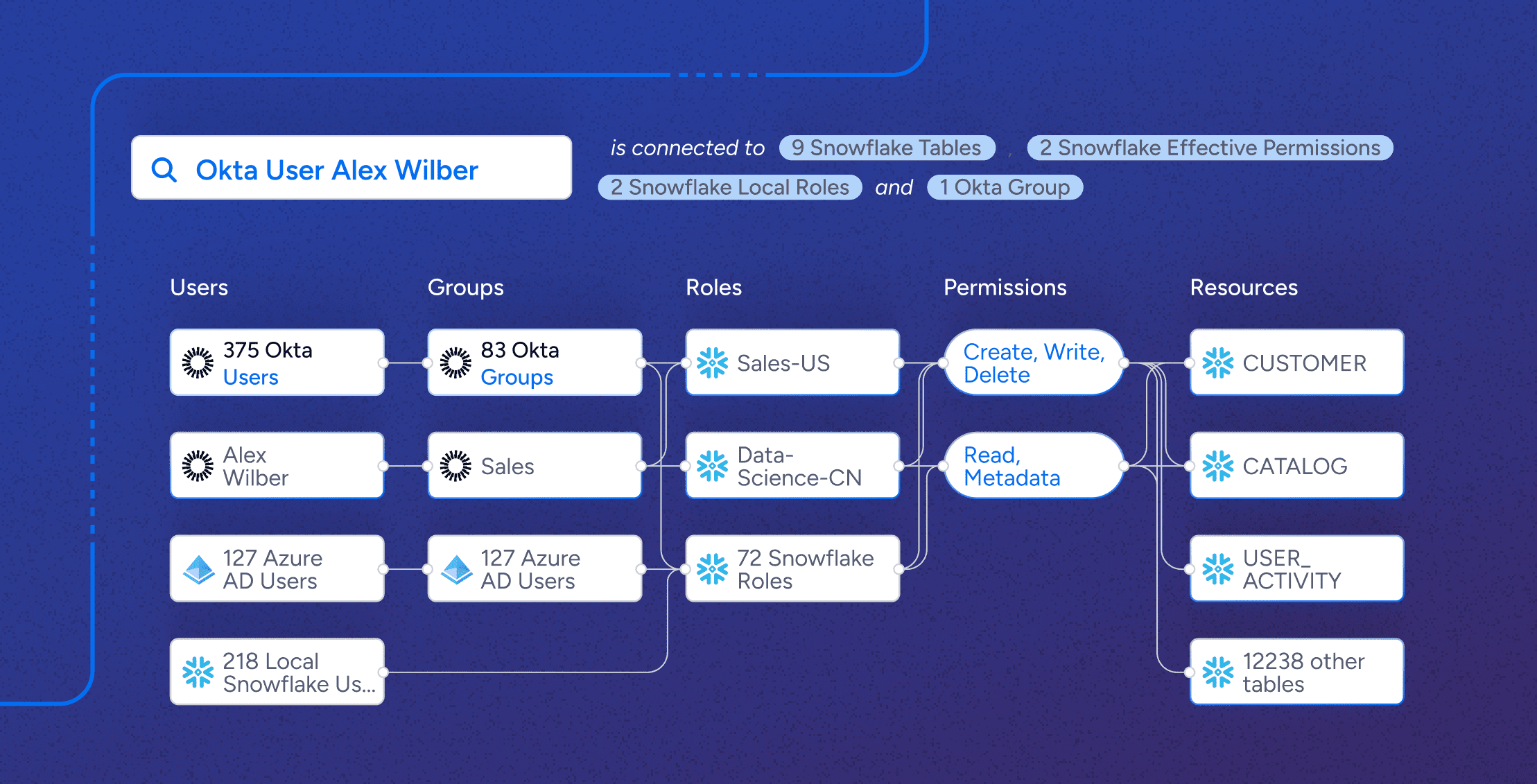
Can you tell who has access to what in Snowflake?
Learn more -
What is Machine Identity Management? [2024 Guide]
Learn more -
The Imperative for Identity Security: A Call to Action for the Industry
Learn more -
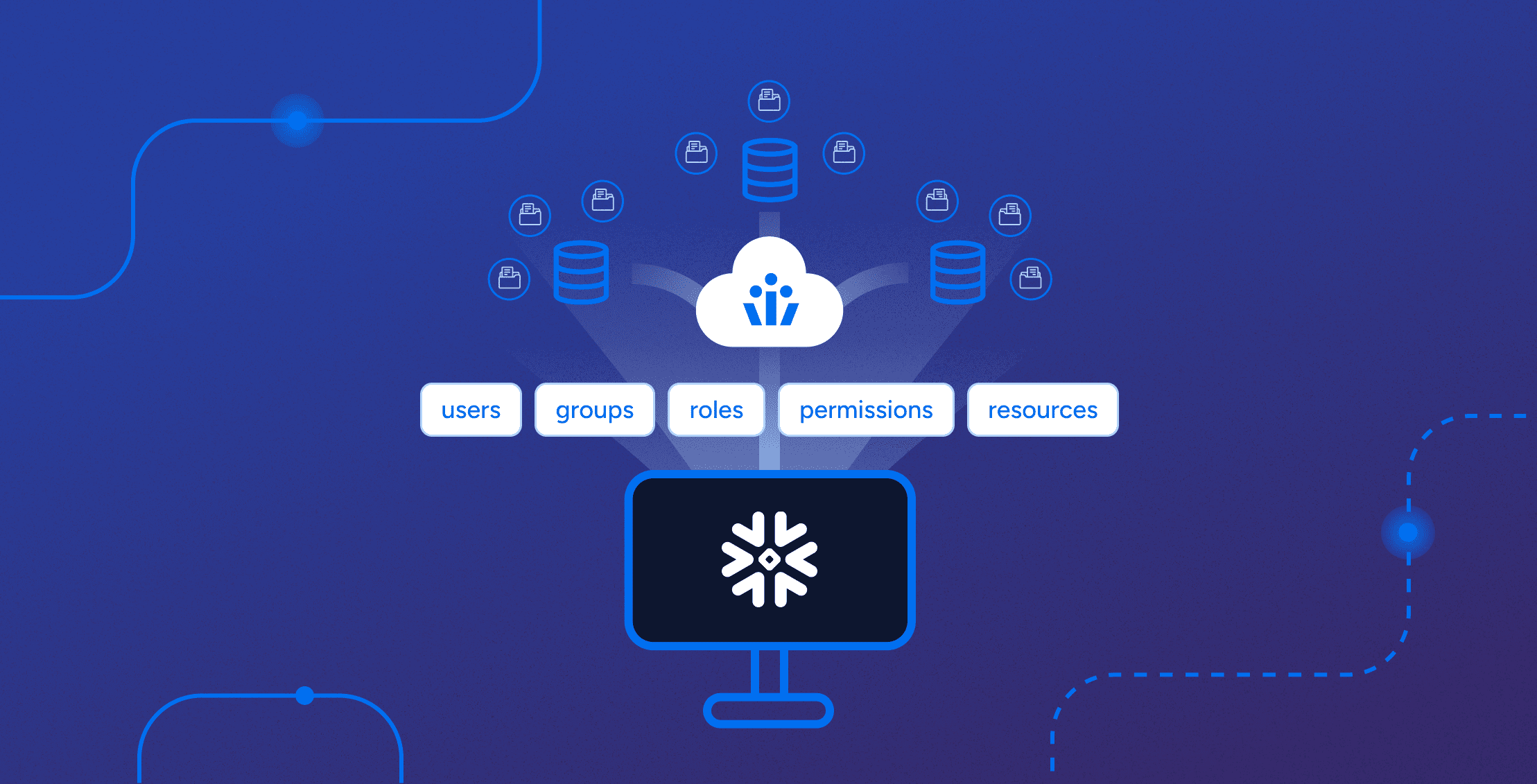
Complete Snowflake Review: Roles, Security & Access Control
Learn more -
Key Takeaways: FBI Breach Prevention Tips
Learn more
-
Where Non-Human Identities (NHIs) and Human Identities Converge: A Comprehensive Approach to Identity Security
Learn more -

Cybersecurity’s biggest challenge: The Principle of Least Privilege
Learn more -

Role mining for Snowflake: four steps toward least privilege
Learn more -
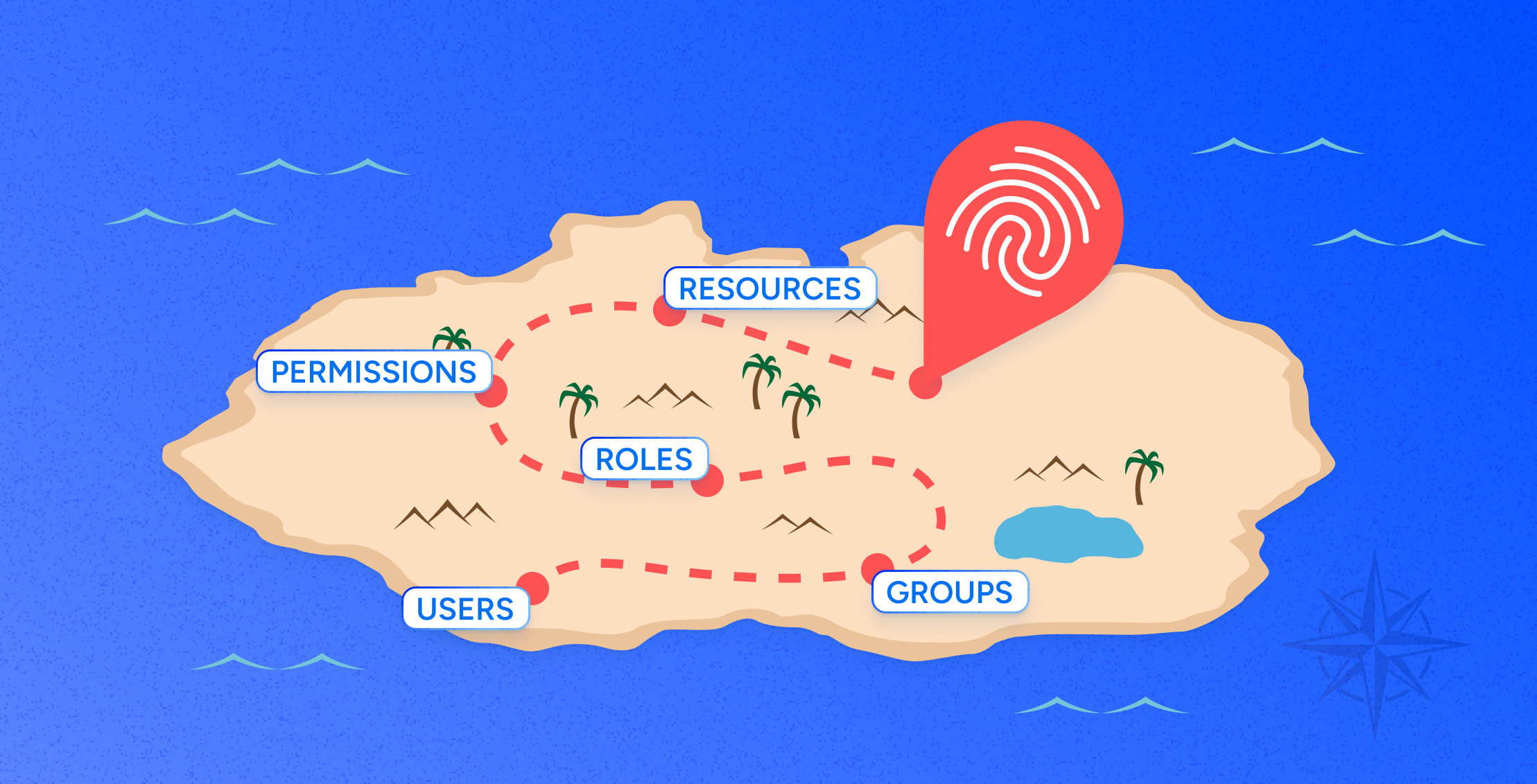
AWS Guide: Access Governance, Security, Compliance & Roles [2024]
Learn more -
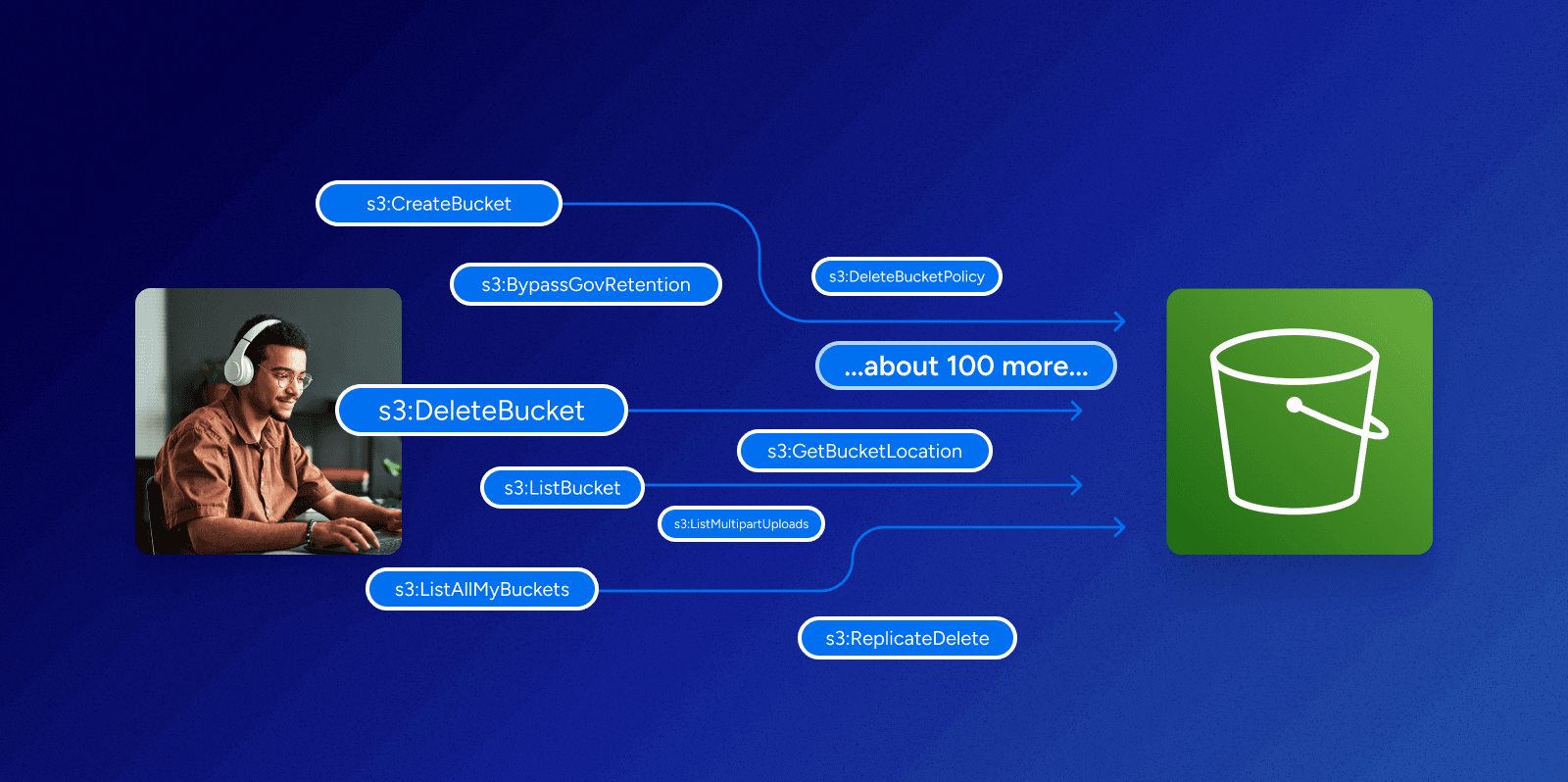
Can you make sense of permissions in AWS?
Learn more
-

Identity Radicals: Groundhog day in identity security
Learn more -
Charting a Path for the Future of Identity Security
Learn more -
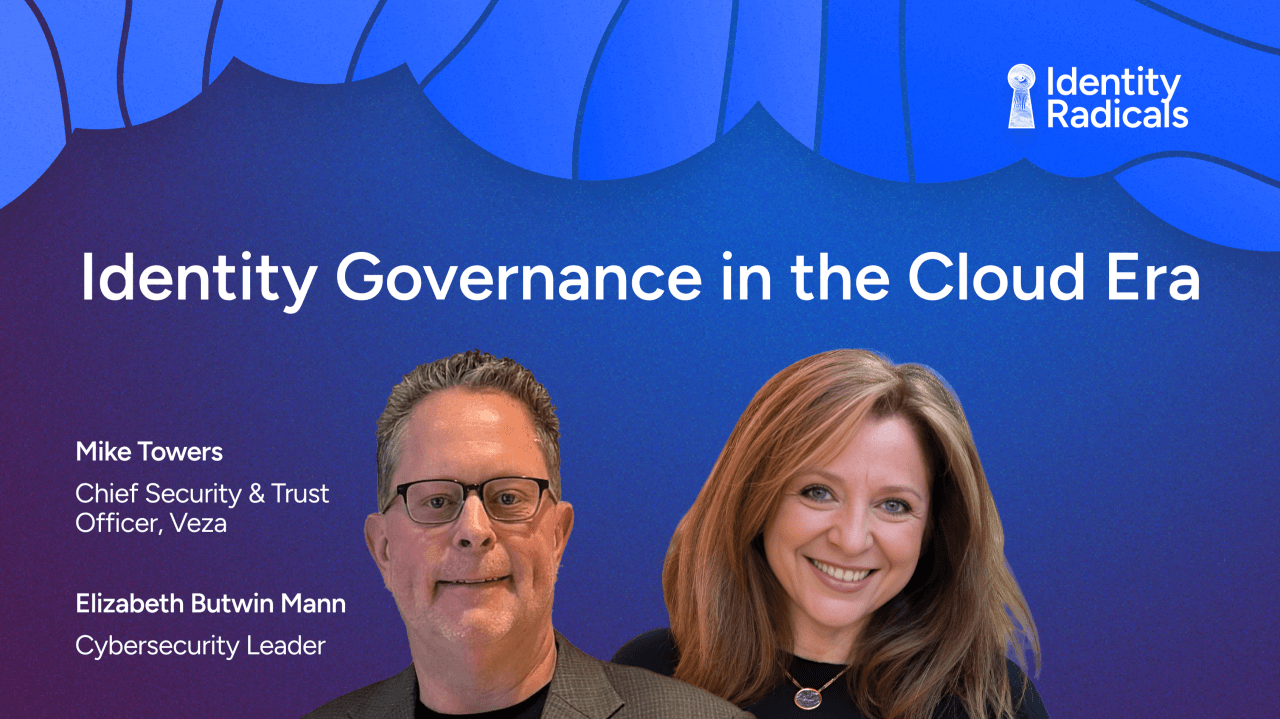
Identity Radicals: Identity governance in the cloud era
Learn more -

Identity Security Posture Management
Learn more -
Decoding Data Sovereignty with Jenner Holden | Ep 3
Learn more -
Disrupting Breaches and Advancing InfoSec with David Tyburski | Ep 2
Learn more
-

Join us at Black Hat USA August 3 – 8, 2024
Learn more -

Join us at RSAC May 6-9, 2024
Learn more -

Veza @ AWS re:Invent
Learn more -
Six takeaways from the Gartner IT Symposium 2023
Learn more -

Veza @ Gartner Symposium — October 15-19
Learn more -

Join Us at Oktane: Explore “Bad Permissions” and Veza’s Access Solutions
Learn more
-
IBM Cost of a Data Breach Report: AI Security Cost Reduction | Veza
Learn more -
Mitigating the UNC3944 Threat: The Power of Modern Identity Security Platforms
Learn more -

Identity Security Spotlight: Ransomware attack on Ascension
Learn more -

Identity Security Spotlight: Microsoft CISA Investigation
Learn more -

Veza welcomes Mike Towers as Chief Security & Trust Officer
Learn more -
Identity Security Spotlight: Delinea acquires Fastpath
Learn more
-

Identity Radicals: Groundhog day in identity security
Learn more -
Operationalizing Modern Identity Security: A CISO’s Perspective on Value Creation and Sustainable Growth
Learn more -

What is lifecycle management in identity security?
Learn more -

SOC 2 Compliance Requirements [2025]
Learn more -
Non-Human Identity Security Risks: Practical Guide to Mitigation | Veza
Learn more -

Going Beyond Provisioning and Deprovisioning with Veza Lifecycle Management
Learn more