On 12 January 2024, a state-sponsored hacking collective known as Midnight Blizzard—the same group responsible for the Solar Winds attack—breached key infrastructure at Microsoft, gaining access to key data, including the email accounts of senior leadership team members. Join Veza’s Chief Strategy Officer Rich Dandliker, and Principal Solutions Architect Tarek Khaled to discuss the implications of the breach, the threat posed by privileged OAuth apps and how Intelligent Access and Veza can protect your organization.
What happened?
Midnight Blizzard’s successful breach of Microsoft was primarily caused by the excessive permissions granted to a legacy OAuth application, revealing machine identities as the key vulnerability. But what allowed the over-privileged OAuth application to be created, and to remain undetected and unremediated for so long?
- Limited Visibility: You can’t address an issue that you can’t identify. A fundamental lack of visibility into the true permissions of identities, including machine identities, allows excess privilege to go unremediated.
- Limitations of role/group-based management: Solely relying on roles or groups for access management proved ineffective. Understanding the specific permissions associated with each role is crucial for achieving true visibility and control. For example, permissions like
Full_access_as_appandEWS.AccessAsUser.Allcould grant complete email access, a detail not obvious to those without specialized knowledge in Exchange Online.
How Veza can help
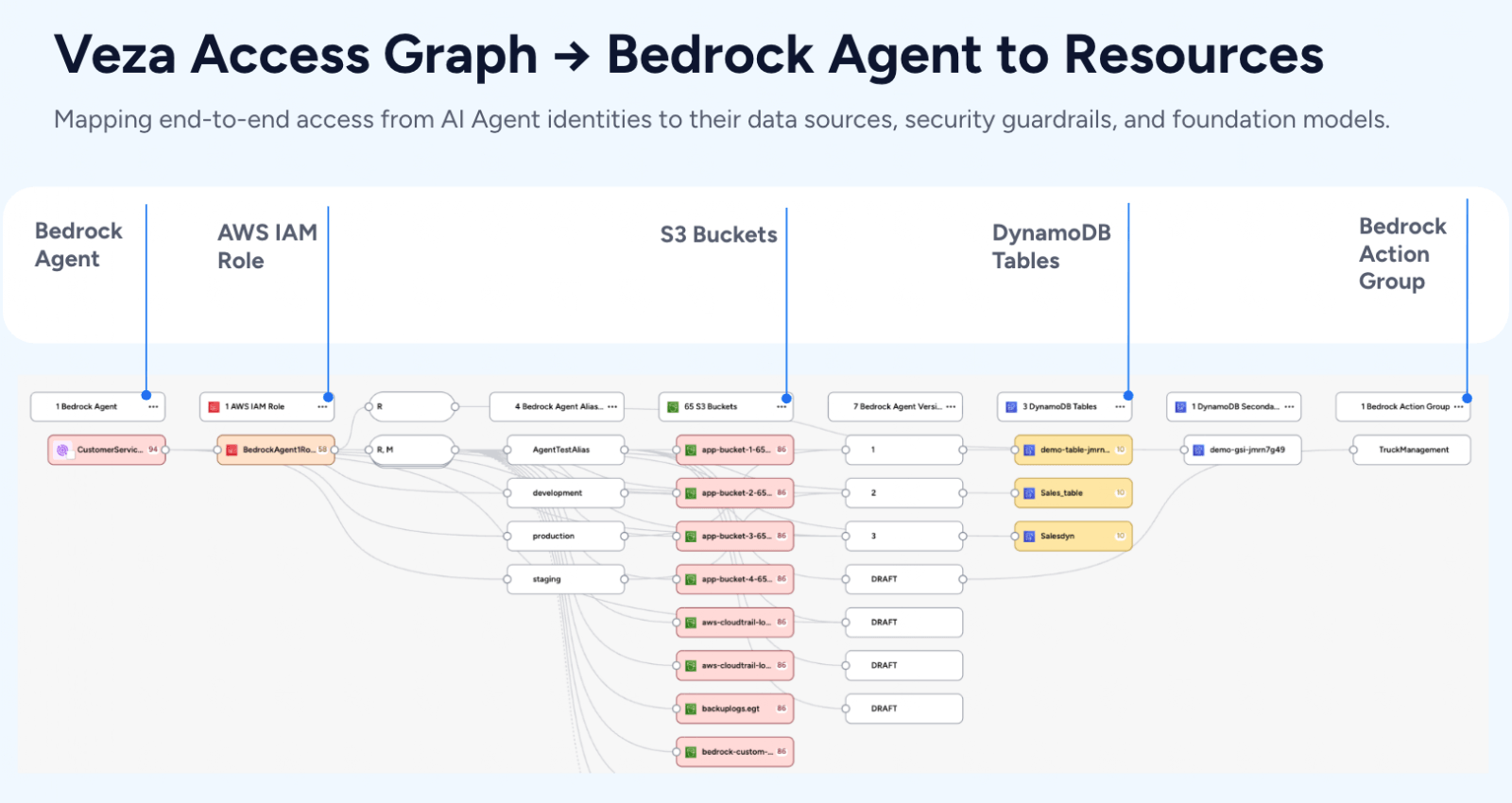
- Comprehensive Visibility: Veza delivers unparalleled visibility into access rights for all identities, both human and machine, ensuring a holistic overview of access points within the system.
- Beyond Basic Role / Group Management: Veza offers detailed insights into the exact permissions each identity holds, utilizing the intuitive language of CRUD (Create, Read, Update, Delete). This approach transcends traditional role and group-based frameworks, providing a deeper understanding of access nuances.
- Risk Prioritization: With Veza, prioritizing security risks becomes more nuanced than the binary classification of privileged vs. non-privileged identities. By evaluating the granular permissions of all identities, Veza effectively identifies potential vulnerabilities, guiding focused remediation efforts based on risk scores. This method ensures that attention is directed towards the permissions most likely to contribute to a data breach.