Data System Access
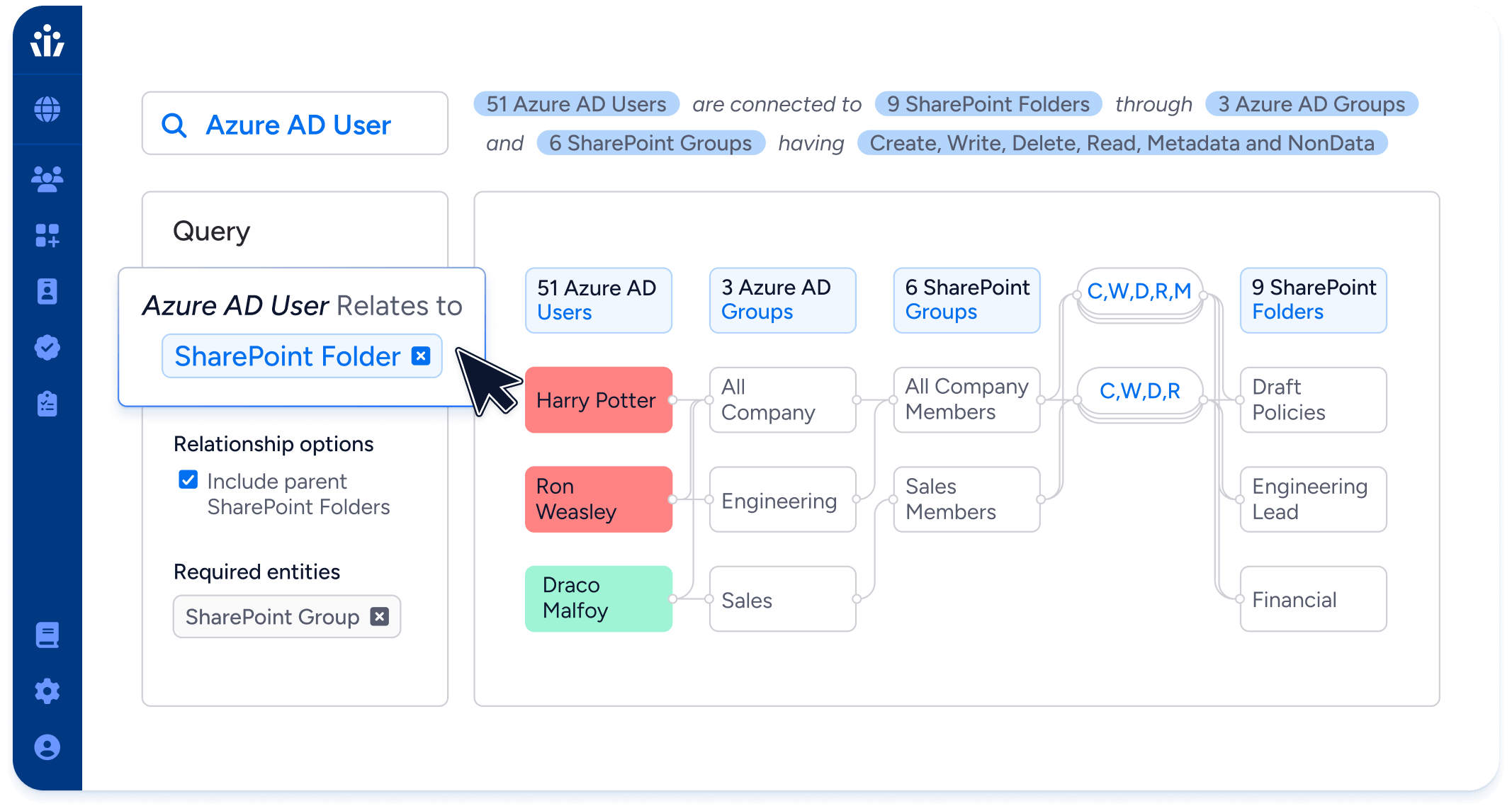
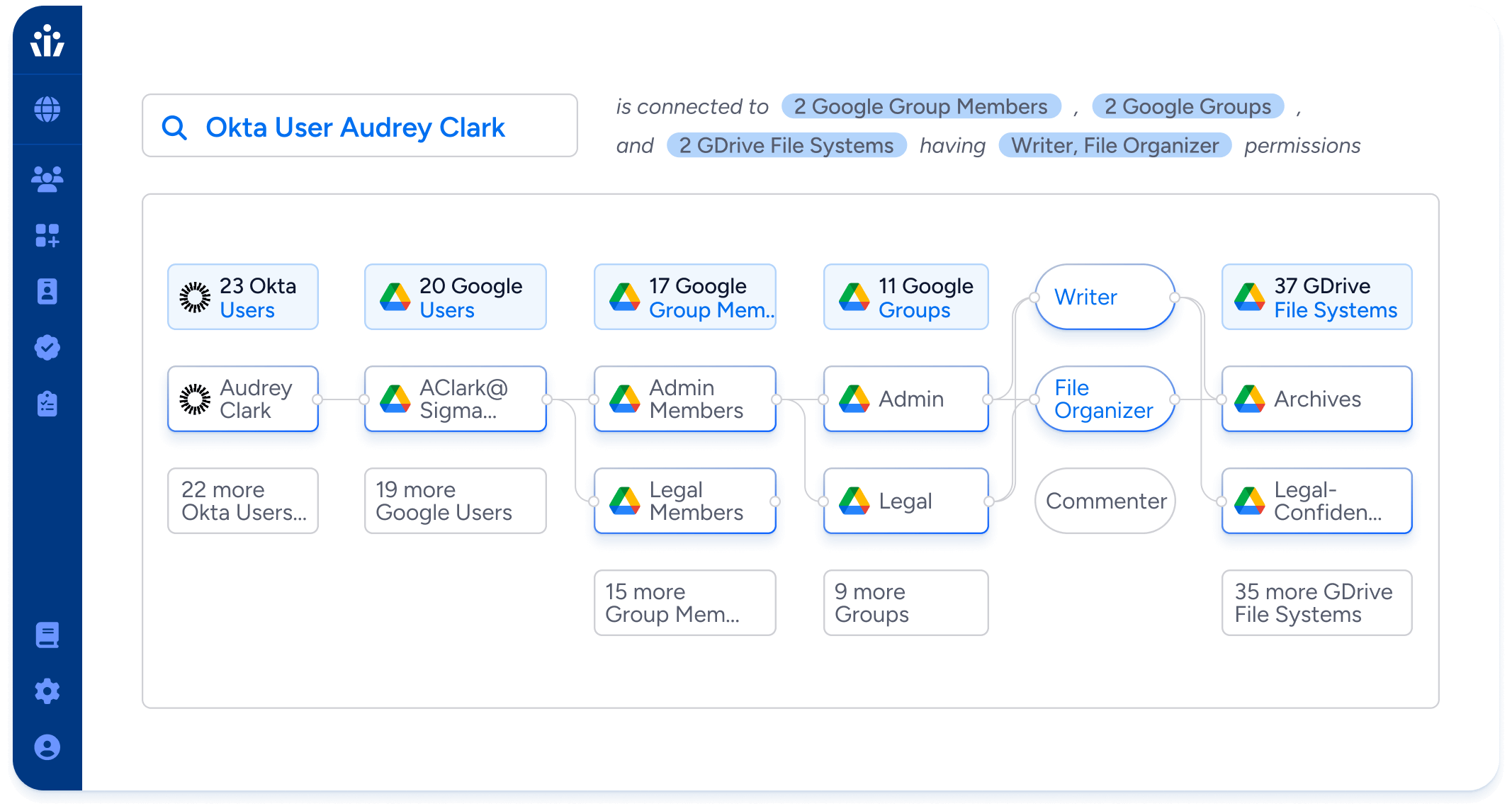
Your most sensitive data may not be neatly stored away in a SQL table, but spread across unstructured data stores beyond the reach of traditional IGA tools. With Veza, you can understand and control access to unstructured data in your data lakes, ML datasets, shared drives, and cloud storage.
Intelligent access for unstructured data
For all your identity security teams
Governance, Risk & Compliance (GRC)
Automatically compile and assign access reviews and certifications for sensitive data in cloud storage buckets or shared drives.
Track sensitive access by guest users, external contractors and third parties
Assign the least permissive role possible for ad hoc access requests to any resources.
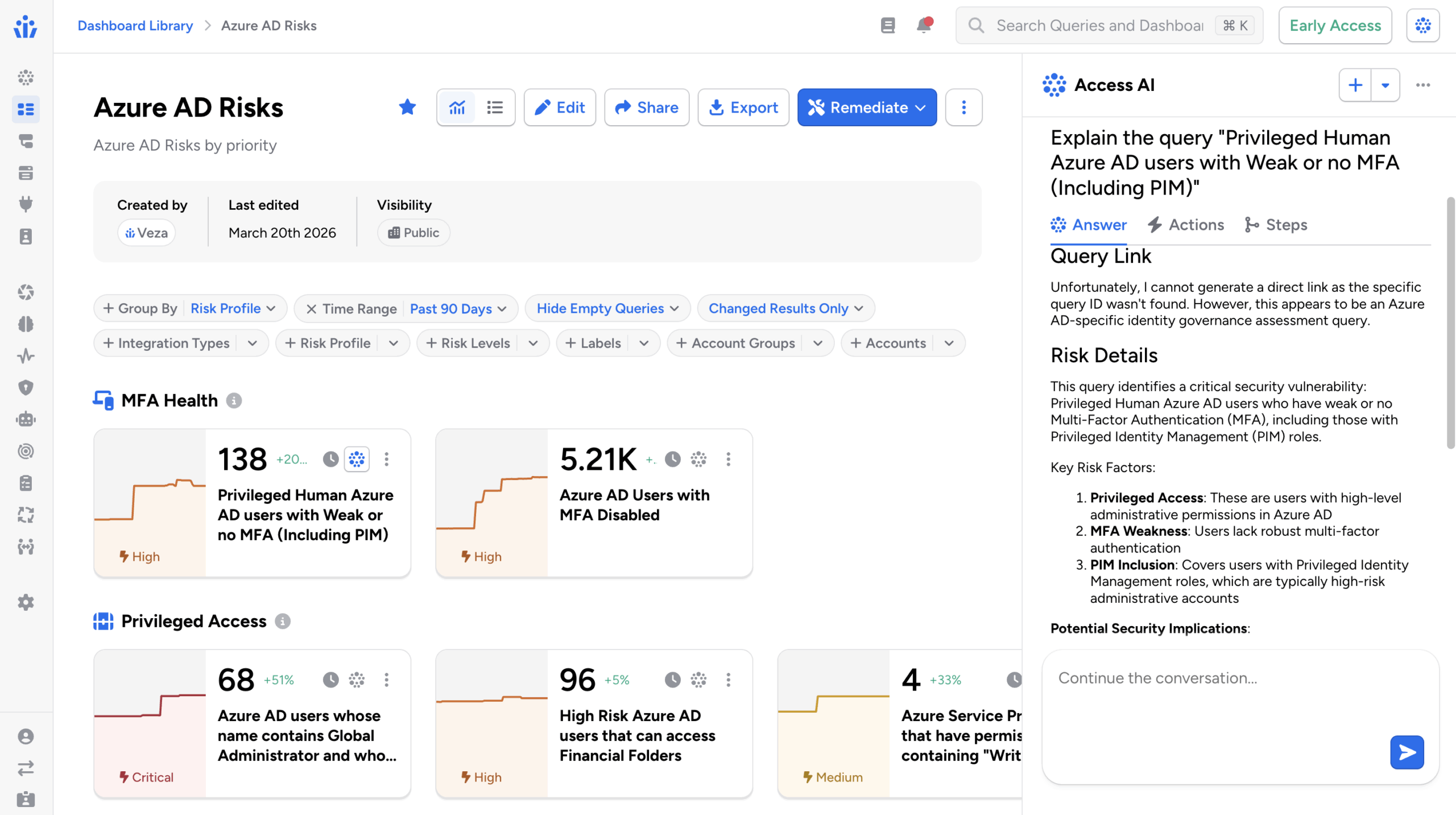
Security and Risk Management (SRM)
Enforce detailed policies for restricting access to different types of unstructured data.
Identify and fix privilege drift and identities with overly broad access to fileshares.
Monitor for shared drive misconfigurations, such as drives that are accessible to the internet.