Tune in to hear Tarun Thakur (Co-Founder & CEO of Veza) and Rich Dandliker (Chief Strategist of Veza) dive into Microsoft’s recent breach. In this chat, they discuss how the breach occurred and what all of us can learn from this incident to strengthen our defenses for a safer future.
The recent attack, perpetrated by Russian Intelligence service-backed hacker group Midnight Blizzard, facilitated a password spray attack to gain access to Microsoft’s test environment. For this test environment, Microsoft did not require users to have MFA enabled, making it easy for the attackers to infiltrate and compromise a legacy Oauth application once inside.
With that Oauth application, the attackers created several additional applications and leveraged them to gain access to the Microsoft corporate environment. Once there, they created a new user and went through a consent flow that granted privileged access to many of the corporate mailboxes within Microsoft.
Our two main takeaways from this breach:
- Highly privileged permissions were at the root of this attack. Once attackers got access to the Oauth application, they were able to grant end permissions that enabled them to move deep within the organization.
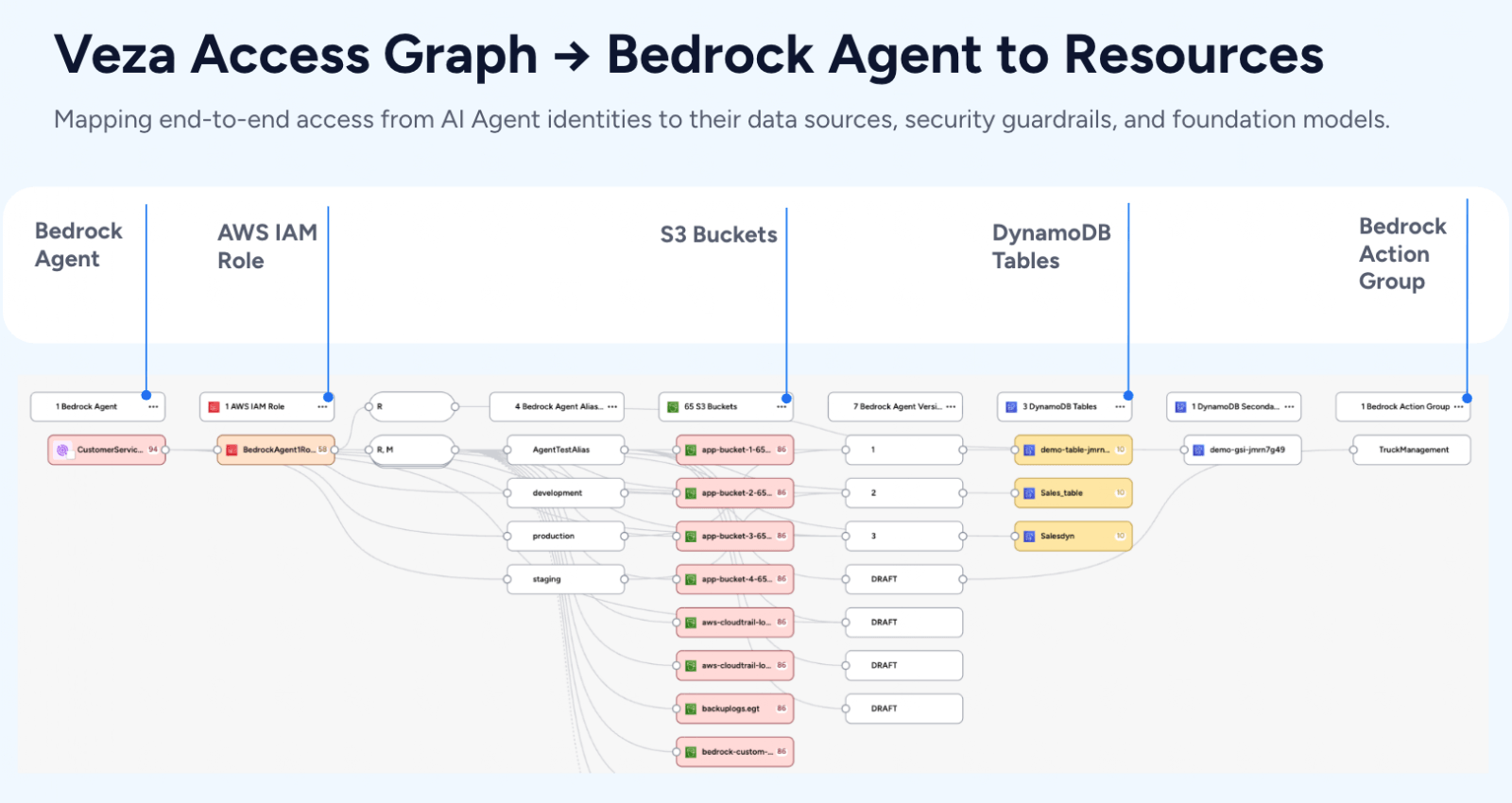
- Lack of visibility around permissions is the greatest vulnerability. Permissions are the truest picture of access; without the ability to visualize who can take what actions across your enterprise, you’re blind to the potential attack vectors a group like Midnight Blizzard might take.
To defend your attack surface against threats like this, consider using tools that allow you to see which identities have access to which resources and alert you when privilege drift occurs. Watch the full video to learn more about how the application impersonation we saw at Microsoft contributed to not only this breach but several other recent security incidents including those at Okta, MGM Hotels and more.
At Veza, we recognize that identity is the new perimeter. We’ve built the Veza Access Control Platform to help organizations answer the critical question, “who can take what action on what data?,” limiting the damage of identity-based threats.