Explore our posts
-
Veza Product Update – April 2023
Learn more -
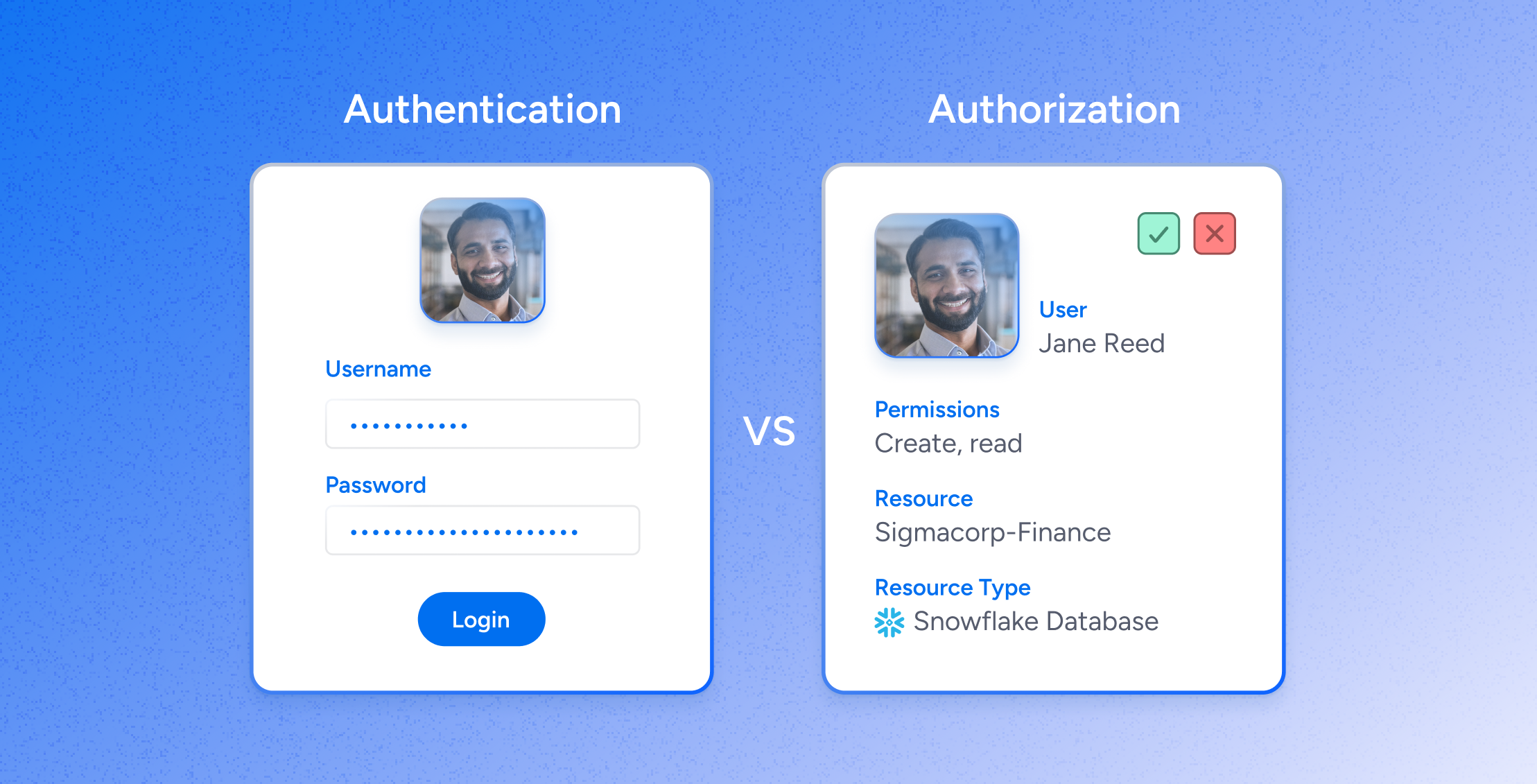
The Identity Authorization Approach to SaaS Access Governance
Learn more -
How strong is your SaaS Security Posture Management (SSPM)?
Learn more -

The Veza Voice – March Issue
Learn more -
Veza at RSA
Learn more -
Veza Welcomes Gertie the Goat to Board of Advisors
Learn more
-
Simplifying Security: The Power of Effective Access Control in Cybersecurity
Learn more -
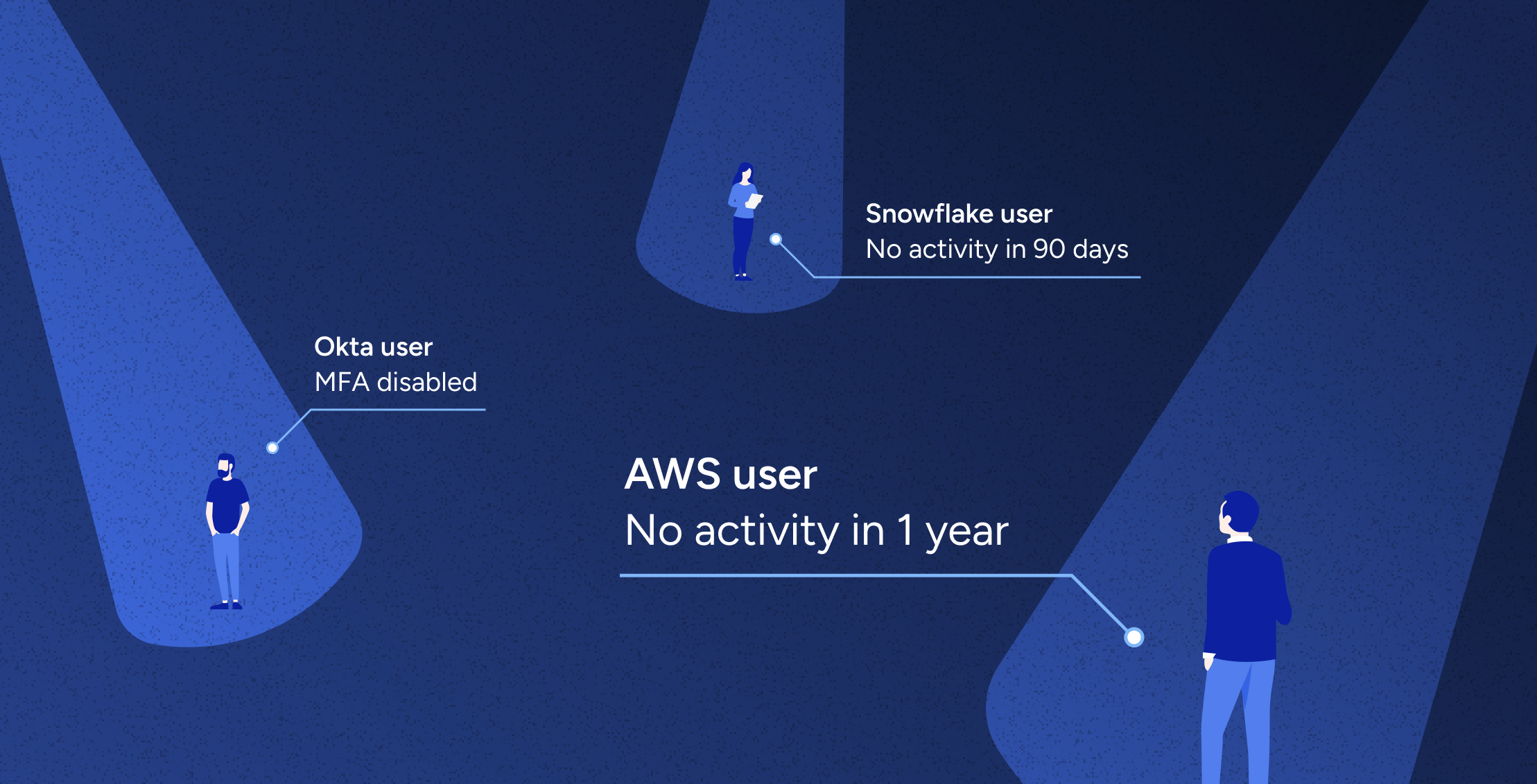
Veza’s Automated Access Revocation and Access Remediation
Learn more -
Securing Snowflake: A CISO’s Guide to Effective Access Control
Learn more -
Introducing Access AI: The Future of Identity Security
Learn more -
What is SaaS Sprawl?
Learn more
-
Where Non-Human Identities (NHIs) and Human Identities Converge: A Comprehensive Approach to Identity Security
Learn more -

Cybersecurity’s biggest challenge: The Principle of Least Privilege
Learn more -

Role mining for Snowflake: four steps toward least privilege
Learn more -
AWS Guide: Access Governance, Security, Compliance & Roles [2024]
Learn more -
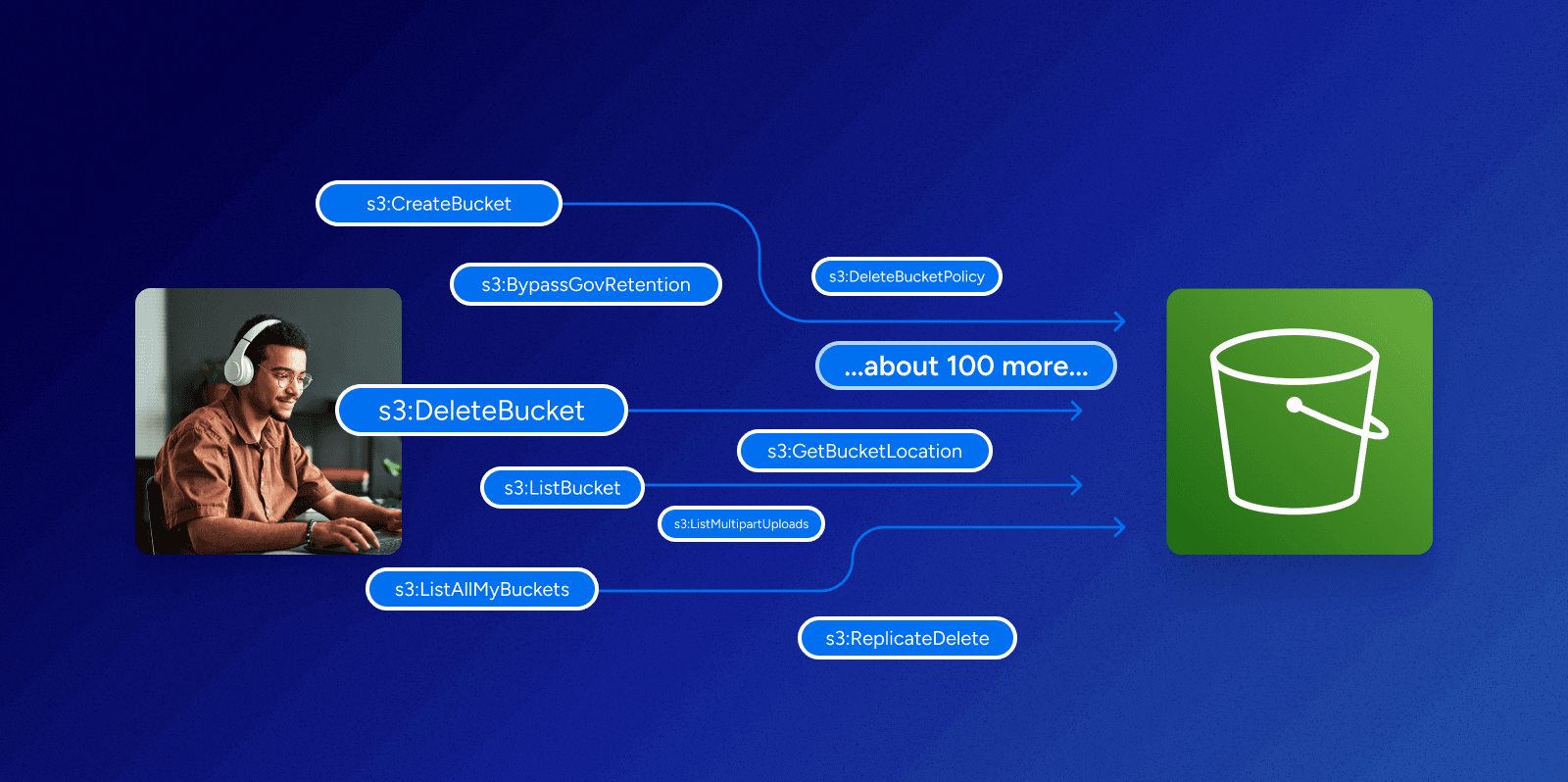
Can you make sense of permissions in AWS?
Learn more
-
Charting a Path for the Future of Identity Security
Learn more -
Identity Radicals: Identity governance in the cloud era
Learn more -

Identity Security Posture Management
Learn more -
Decoding Data Sovereignty with Jenner Holden | Ep 3
Learn more -
Disrupting Breaches and Advancing InfoSec with David Tyburski | Ep 2
Learn more -
Identity Targeting: A Growing Threat with Rachel Wilson | Ep 1
Learn more
-
IBM’s 2024 Cost of a Data Breach Report: AI-Powered Security Lowers Costs
Learn more -
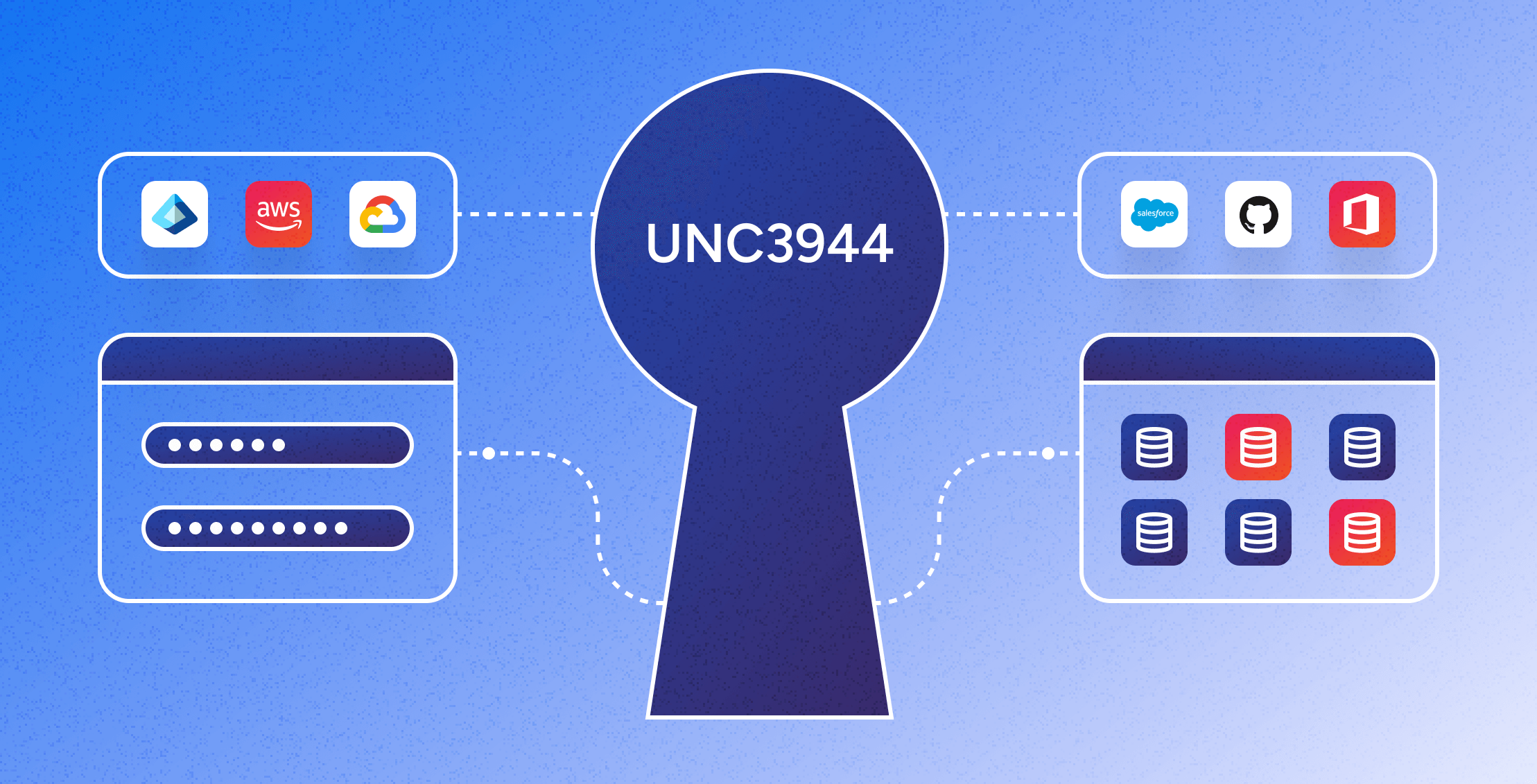
Mitigating the UNC3944 Threat: The Power of Modern Identity Security Platforms
Learn more -

Identity Security Spotlight: Ransomware attack on Ascension
Learn more -

Identity Security Spotlight: Microsoft CISA Investigation
Learn more -

Veza welcomes Mike Towers as Chief Security & Trust Officer
Learn more -
Identity Security Spotlight: Delinea acquires Fastpath
Learn more
-
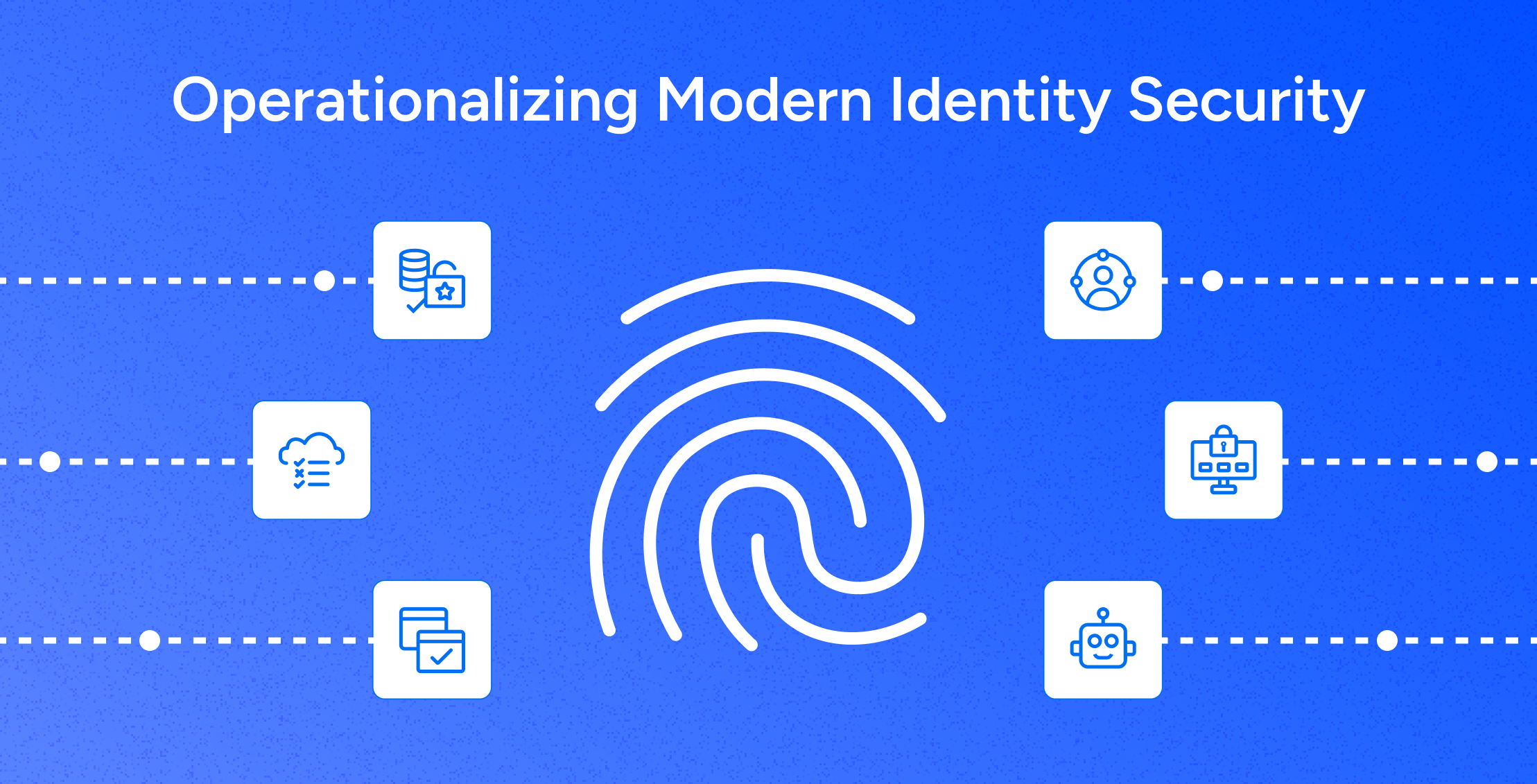
Operationalizing Modern Identity Security: A CISO’s Perspective on Value Creation and Sustainable Growth
Learn more -

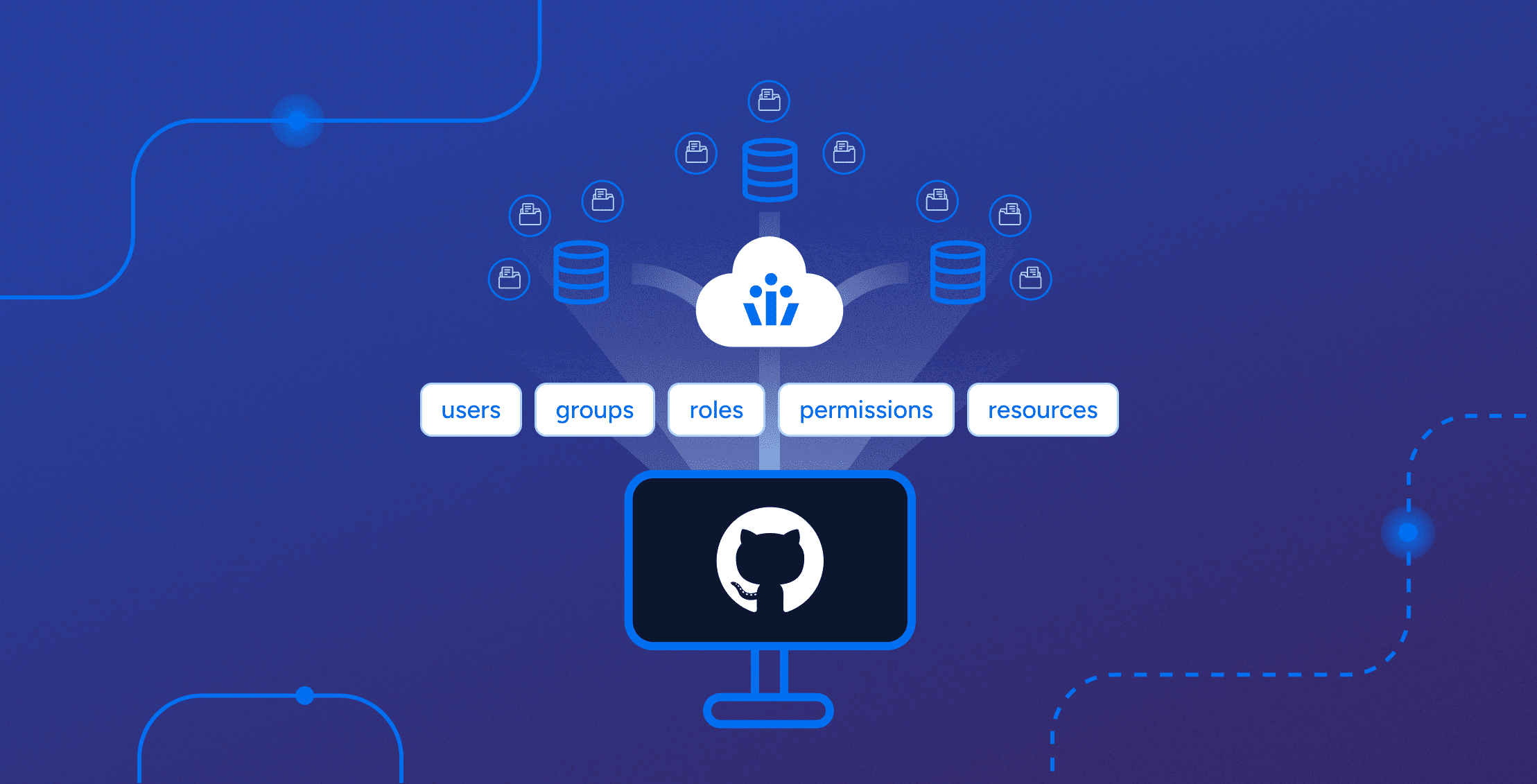
What is lifecycle management in identity security?
Learn more -

SOC 2 Compliance Requirements [2025]
Learn more -
Non-Human Identity Security: A Practical Guide to Mitigating Risk
Learn more -

Going Beyond Provisioning and Deprovisioning with Veza Lifecycle Management
Learn more -
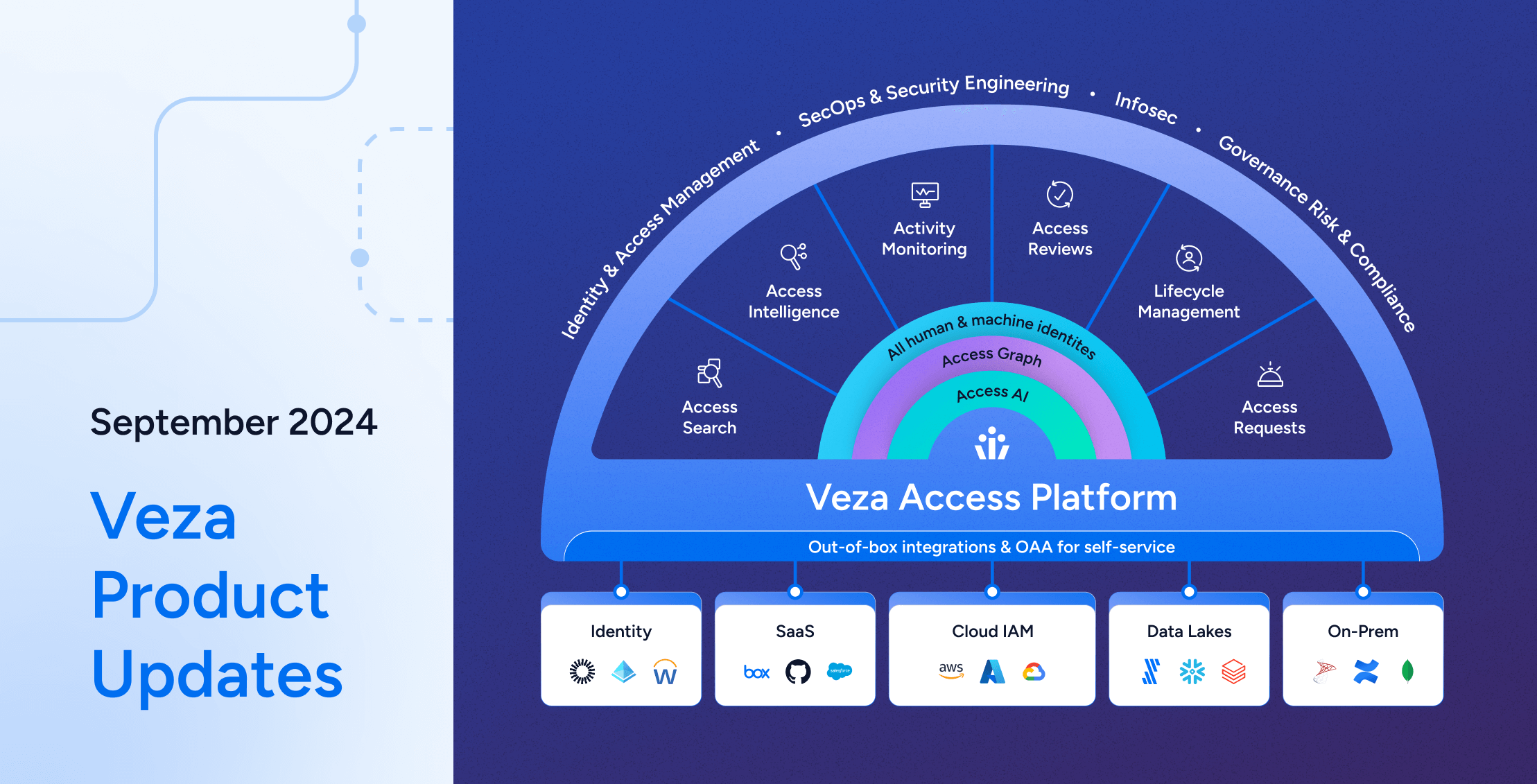
Veza Product Updates – September 2024
Learn more