Explore our posts
All Types
All Types
Authorization
Company
Data Security
History of Hacks
IAM
Identity Radicals
Industry Events
Industry News
Multi-Cloud
Privileged Access
-

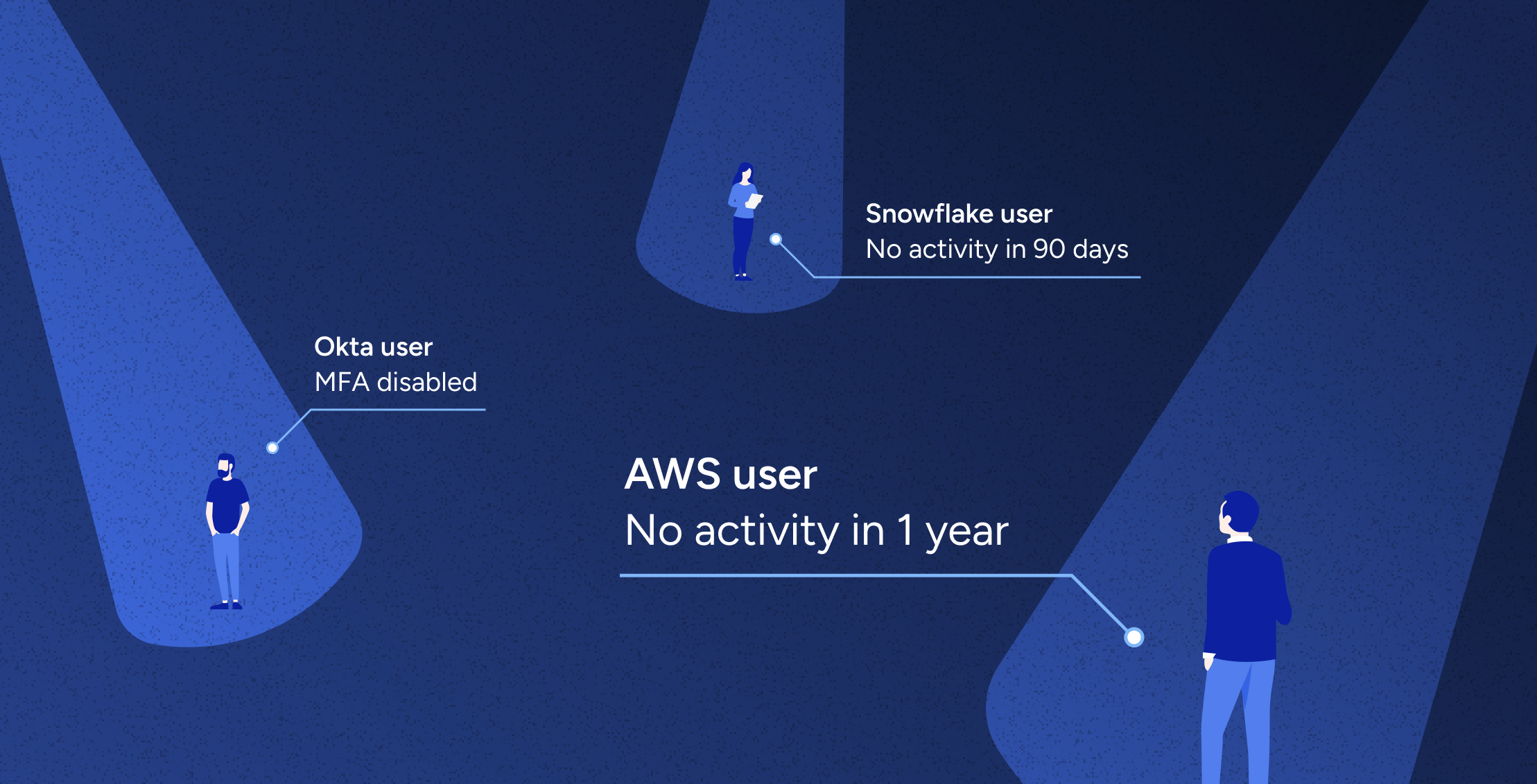
Identity Security Posture Management
Learn more -
The MIGHT of Veza
Learn more -

Veza welcomes Mike Towers as Chief Security & Trust Officer
Learn more -

Identity Security Spotlight: Cisco announces “Identity Intelligence”
Learn more -
Veza @ Blackstone: Modernizing IGA with Automation and Intelligence
Learn more -
The year of Intelligent Access
Learn more
-
Simplifying Security: The Power of Effective Access Control in Cybersecurity
Learn more -
Veza’s Automated Access Revocation and Access Remediation
Learn more -
Securing Snowflake: A CISO’s Guide to Effective Access Control
Learn more -
Acess AI: Introducting the Future of Identity Security | Veza
Learn more -
What is SaaS Sprawl?
Learn more
-
Where Non-Human Identities (NHIs) and Human Identities Converge: A Comprehensive Approach to Identity Security
Learn more -

Cybersecurity’s biggest challenge: The Principle of Least Privilege
Learn more -

Role mining for Snowflake: four steps toward least privilege
Learn more -
AWS Guide: Access Governance, Security, Compliance & Roles [2024]
Learn more -
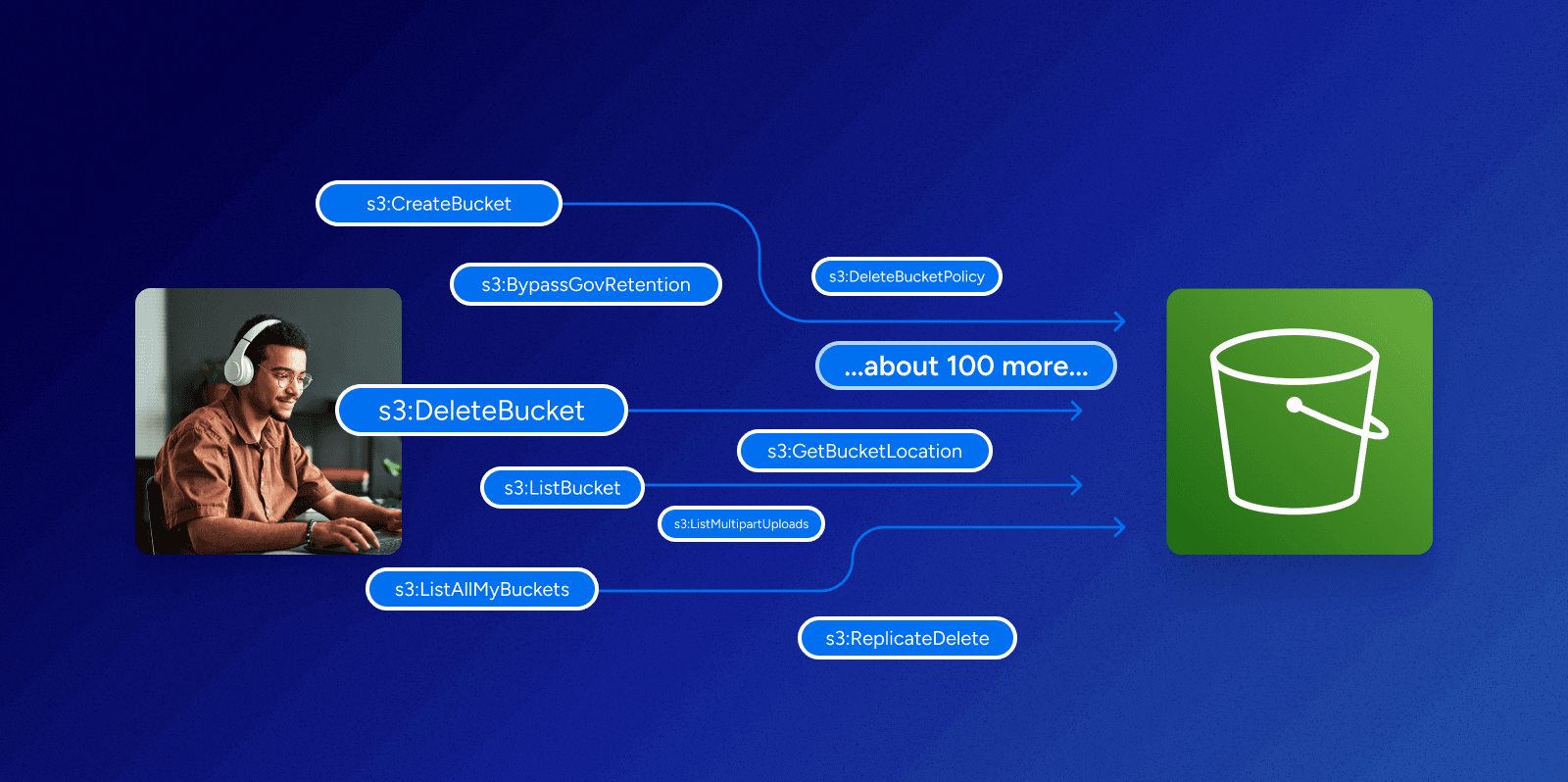
Can you make sense of permissions in AWS?
Learn more
-
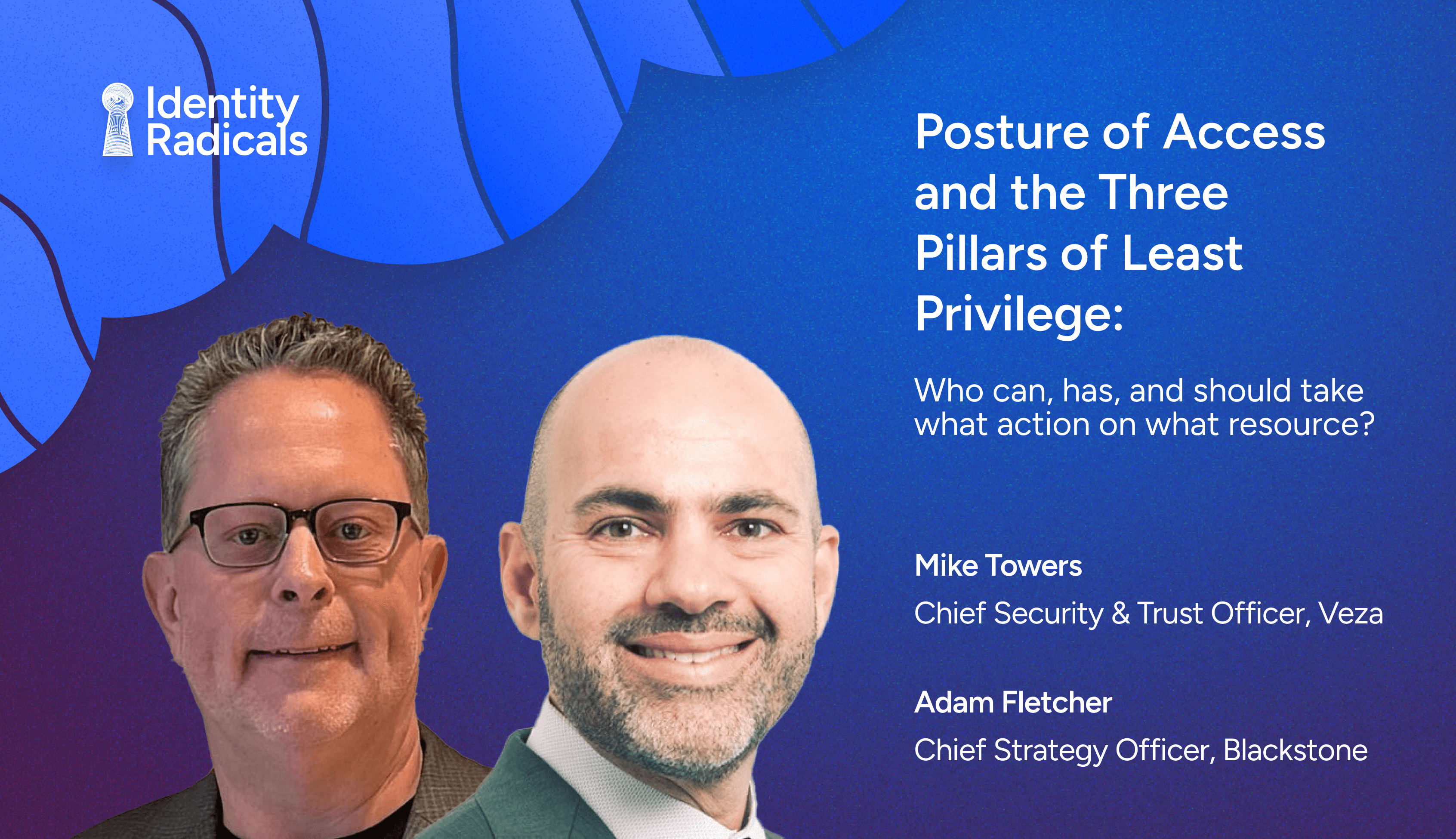
Posture of Access, 3 Pillars of Least Privilege | Ep 6, Identity Radicals Podcast with Adam Fletcher
Learn more -

Identity Radicals: Groundhog day in identity security
Learn more -
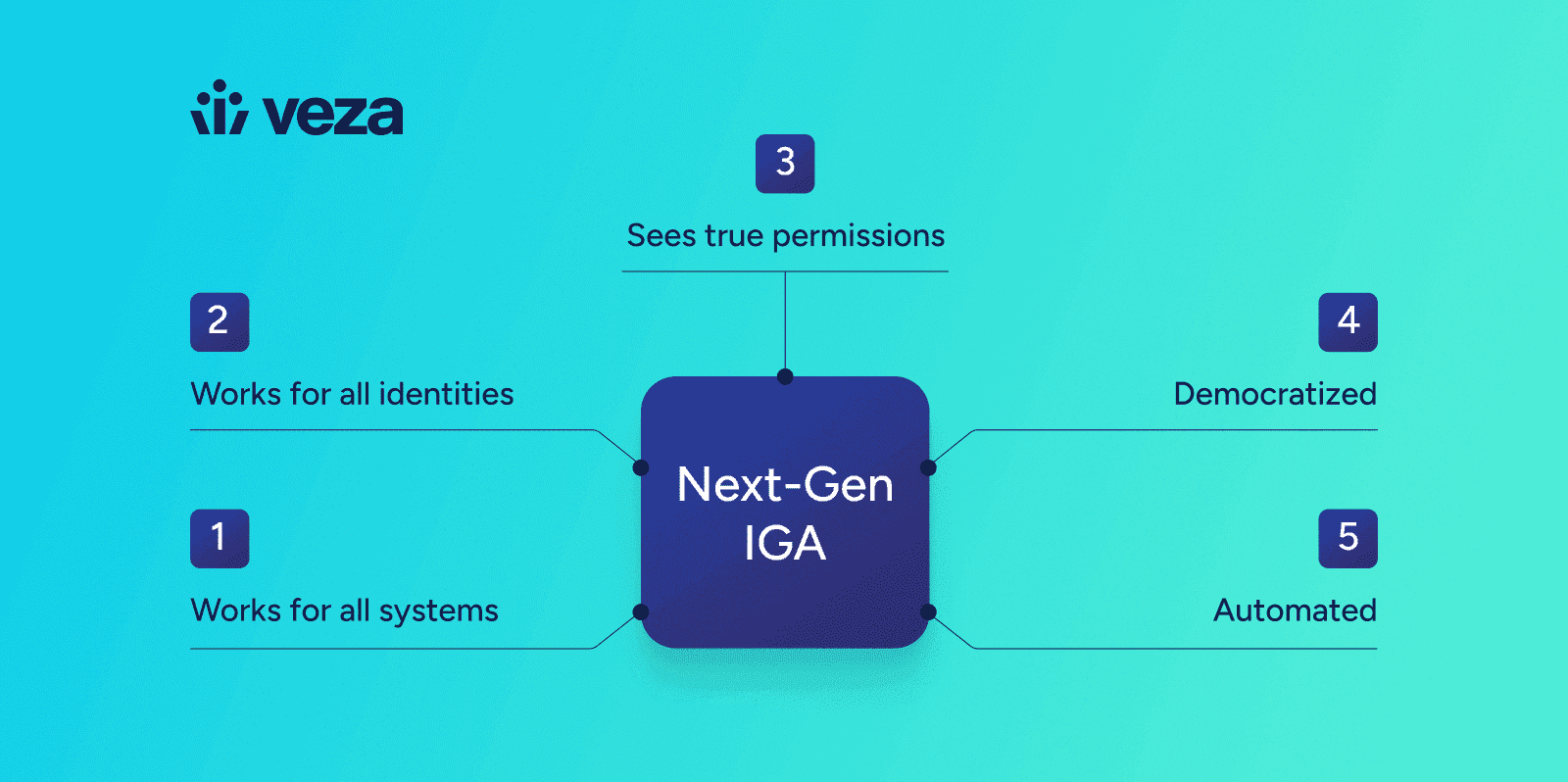
Charting a Path for the Future of Identity Security
Learn more -
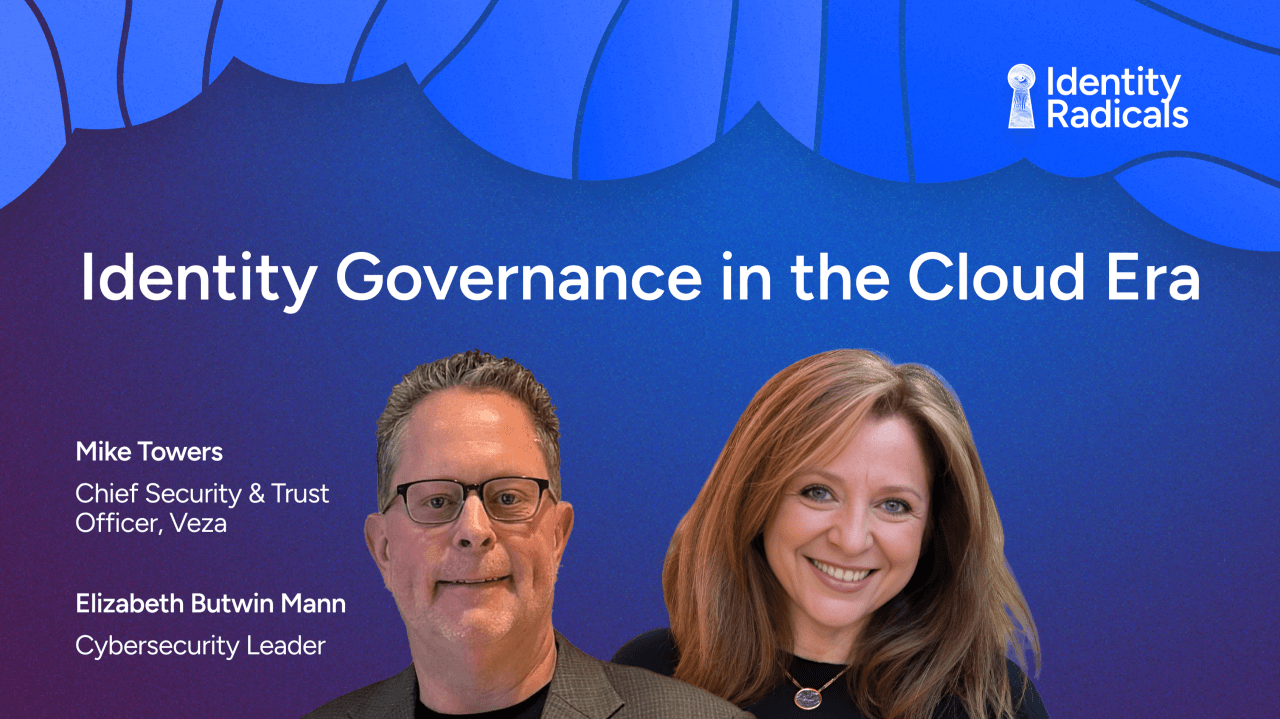
Identity Radicals: Identity governance in the cloud era
Learn more -

Identity Security Posture Management
Learn more -
Decoding Data Sovereignty with Jenner Holden | Ep 3
Learn more
-

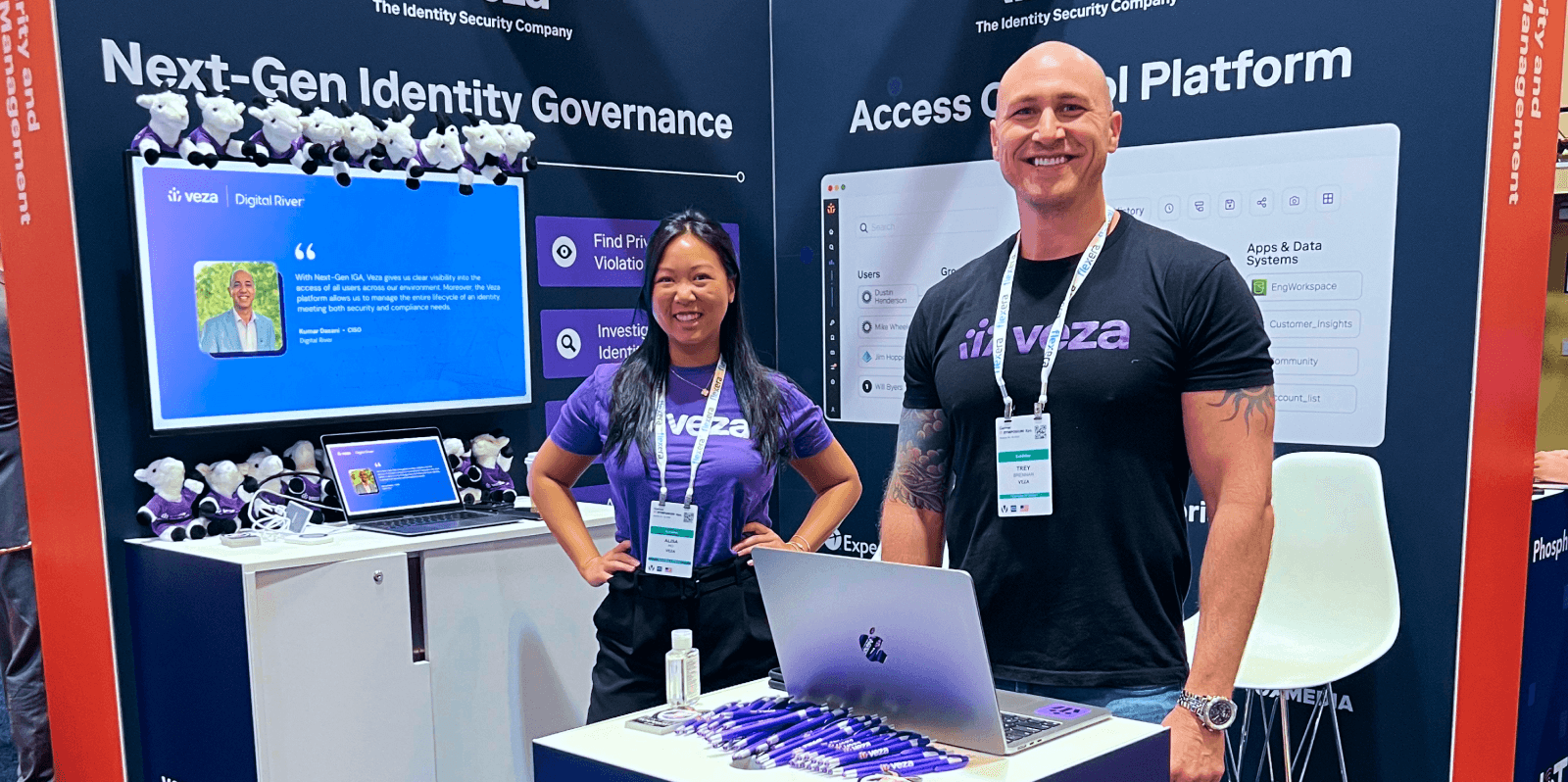
Join us at Black Hat USA August 3 – 8, 2024
Learn more -

Join us at RSAC May 6-9, 2024
Learn more -

Veza @ AWS re:Invent
Learn more -
Six takeaways from the Gartner IT Symposium 2023
Learn more -

Veza @ Gartner Symposium — October 15-19
Learn more -

Join Us at Oktane: Explore “Bad Permissions” and Veza’s Access Solutions
Learn more
No results found.
-
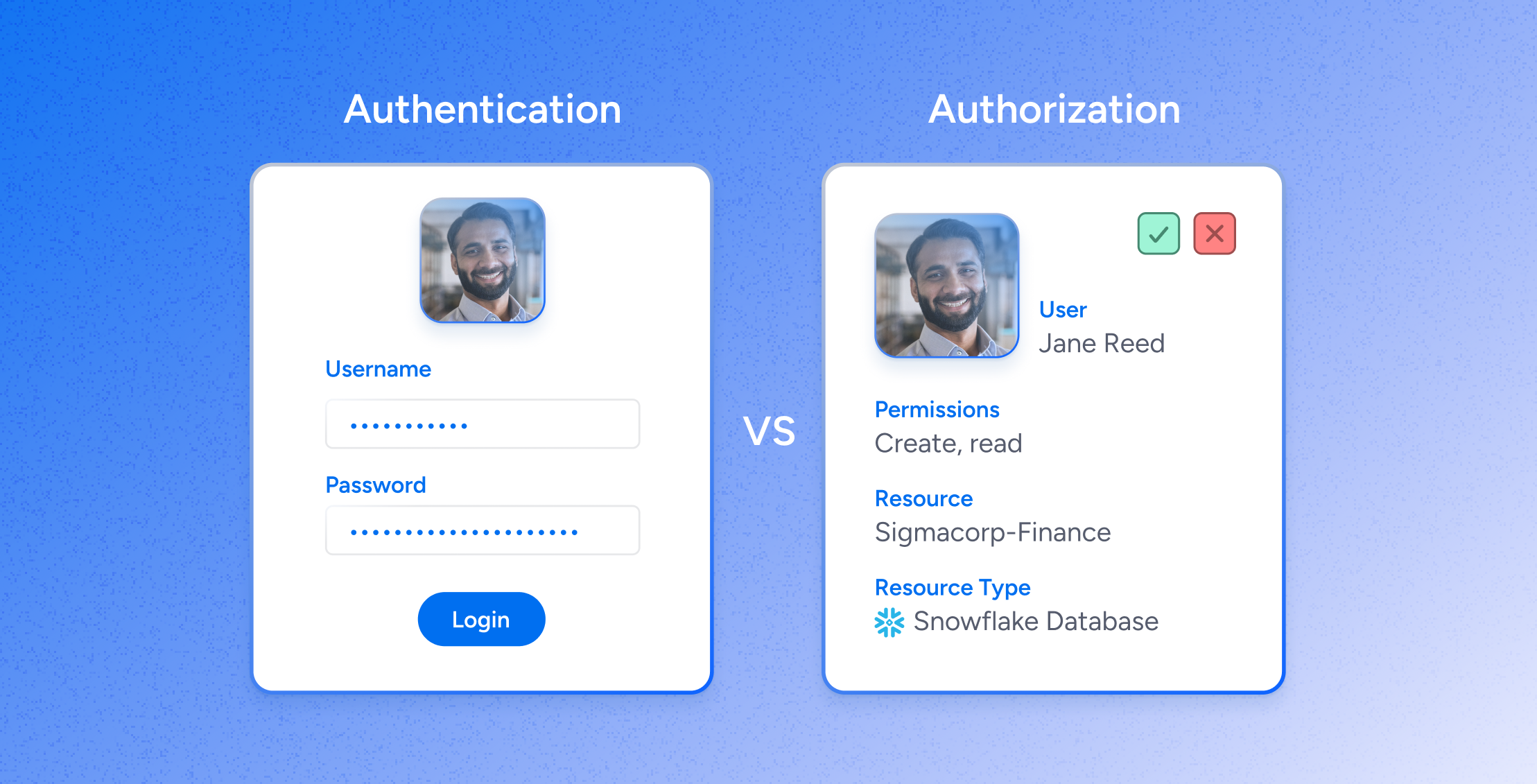
Authorization, NOT Authentication: the critical backbone for zero-trust security
Learn more -
Digital Transformation and the Data Authorization Imperative
Learn more -
Data Security: The Challenge of Securing Service Accounts
Learn more -
Why I’m excited about the future of Veza
Learn more -
Introducing Veza — Our Quest to Advance the Data Security Industry for Decades to Come
Learn more