Explore our posts
-
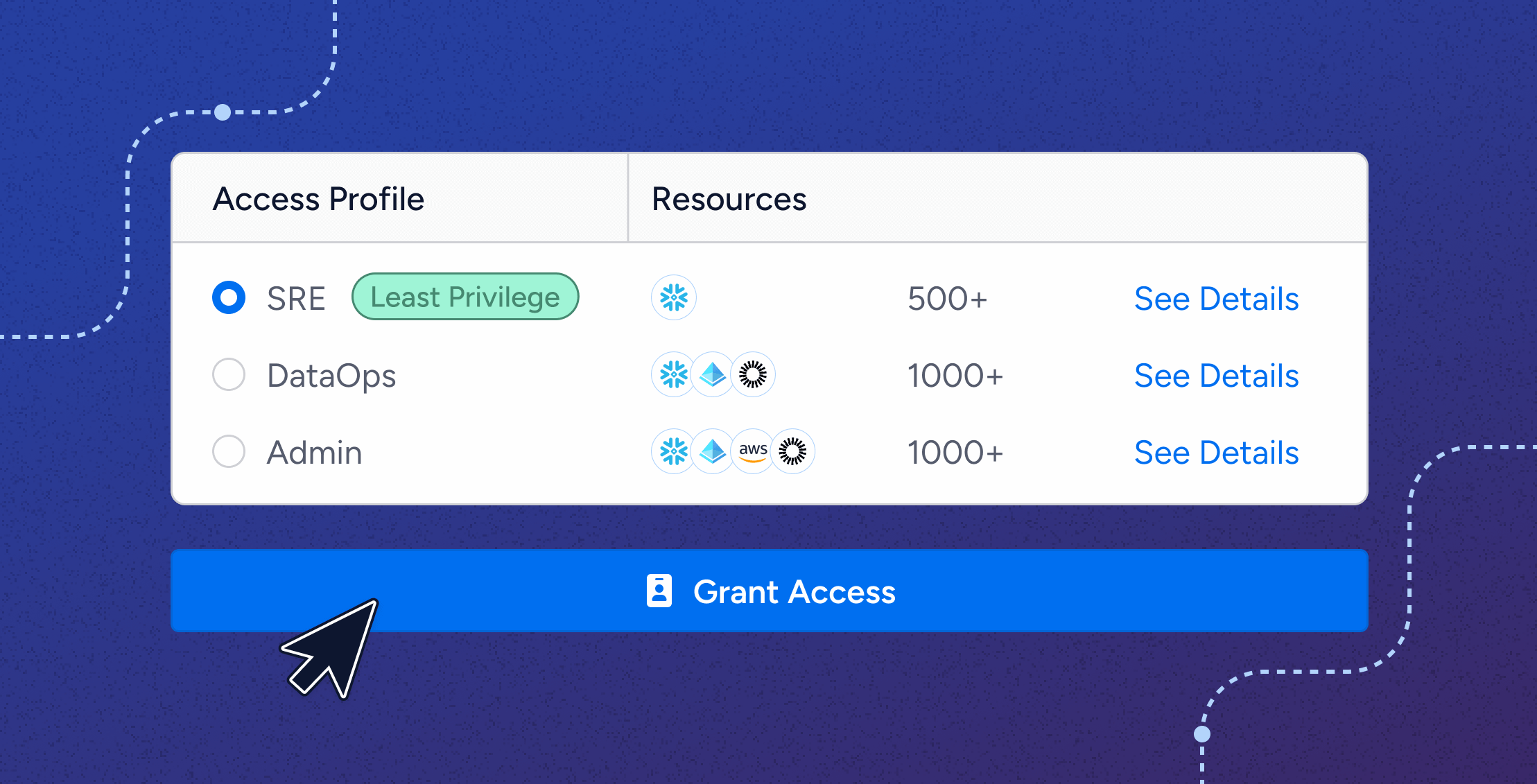
Introducing Veza Access Requests: Automated, Policy-Driven Access at Scale
Learn more -
SOX Compliance Checklist: Your Sarbanes-Oxley Guide for 2025
Learn more -
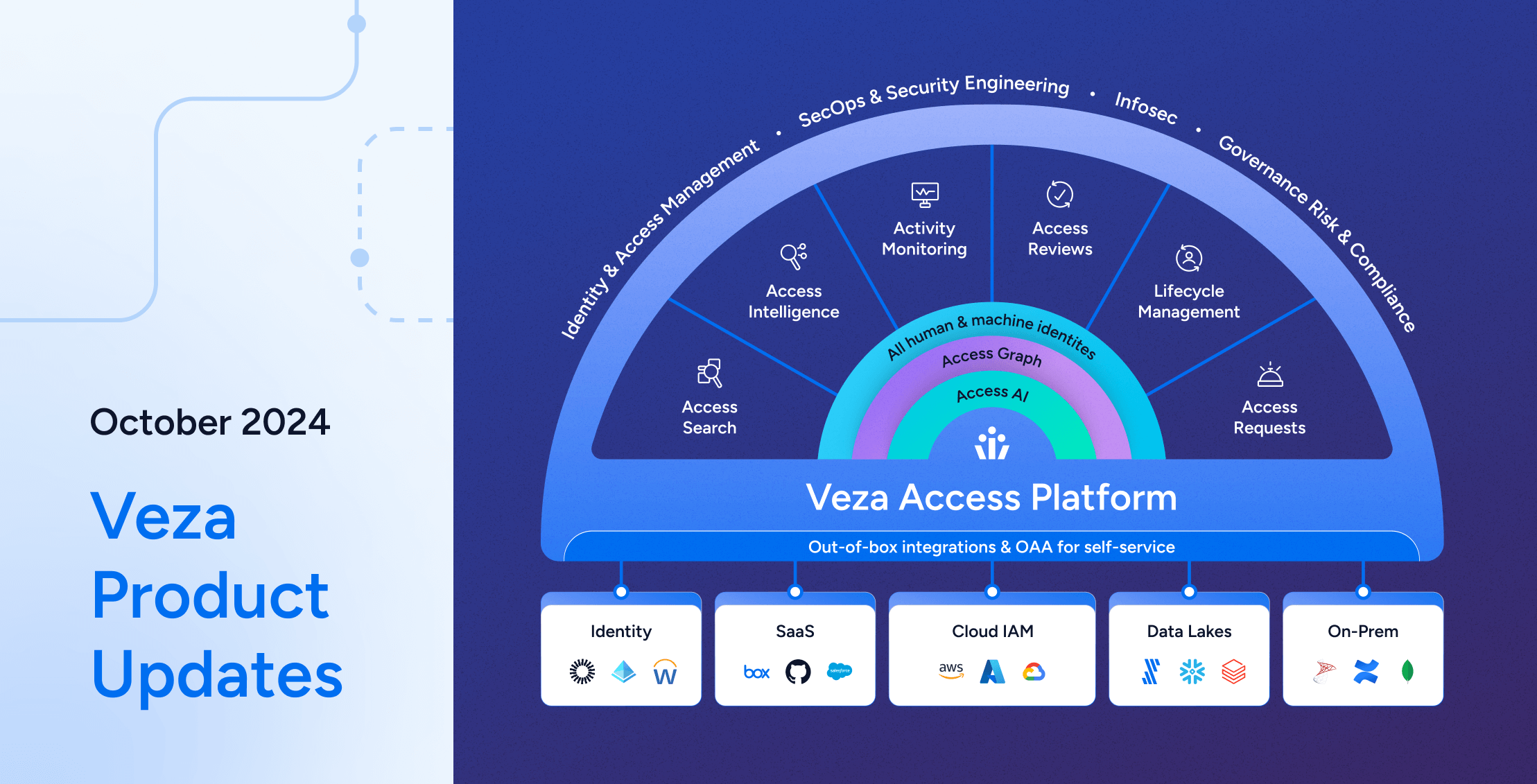
Veza Product Updates – October 2024
Learn more -

Groundhog day in identity security
Learn more -
Operationalizing Modern Identity Security: A CISO’s Perspective on Value Creation and Sustainable Growth
Learn more -

12 Top IGA Software Vendors [2025 Guide]
Learn more
-

Identity Security Posture Management
Learn more -
The MIGHT of Veza
Learn more -

Veza welcomes Mike Towers as Chief Security & Trust Officer
Learn more -

Identity Security Spotlight: Cisco announces “Identity Intelligence”
Learn more -
Veza @ Blackstone: Modernizing IGA with Automation and Intelligence
Learn more -
The year of Intelligent Access
Learn more
-
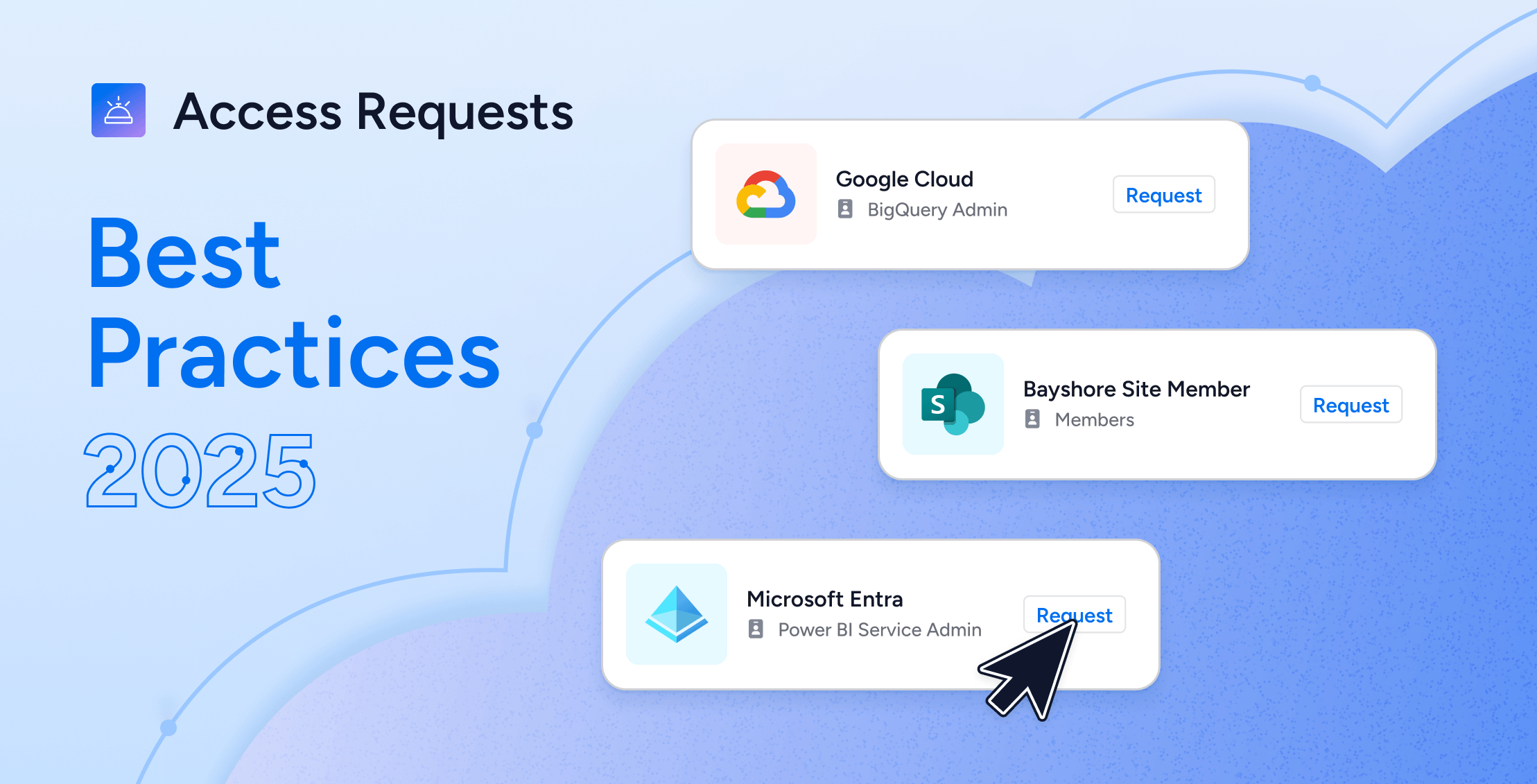
Modern Access Request Processes: Best Practices & What to Avoid in 2025
Learn more -
Simplifying Security: The Power of Effective Access Control in Cybersecurity
Learn more -
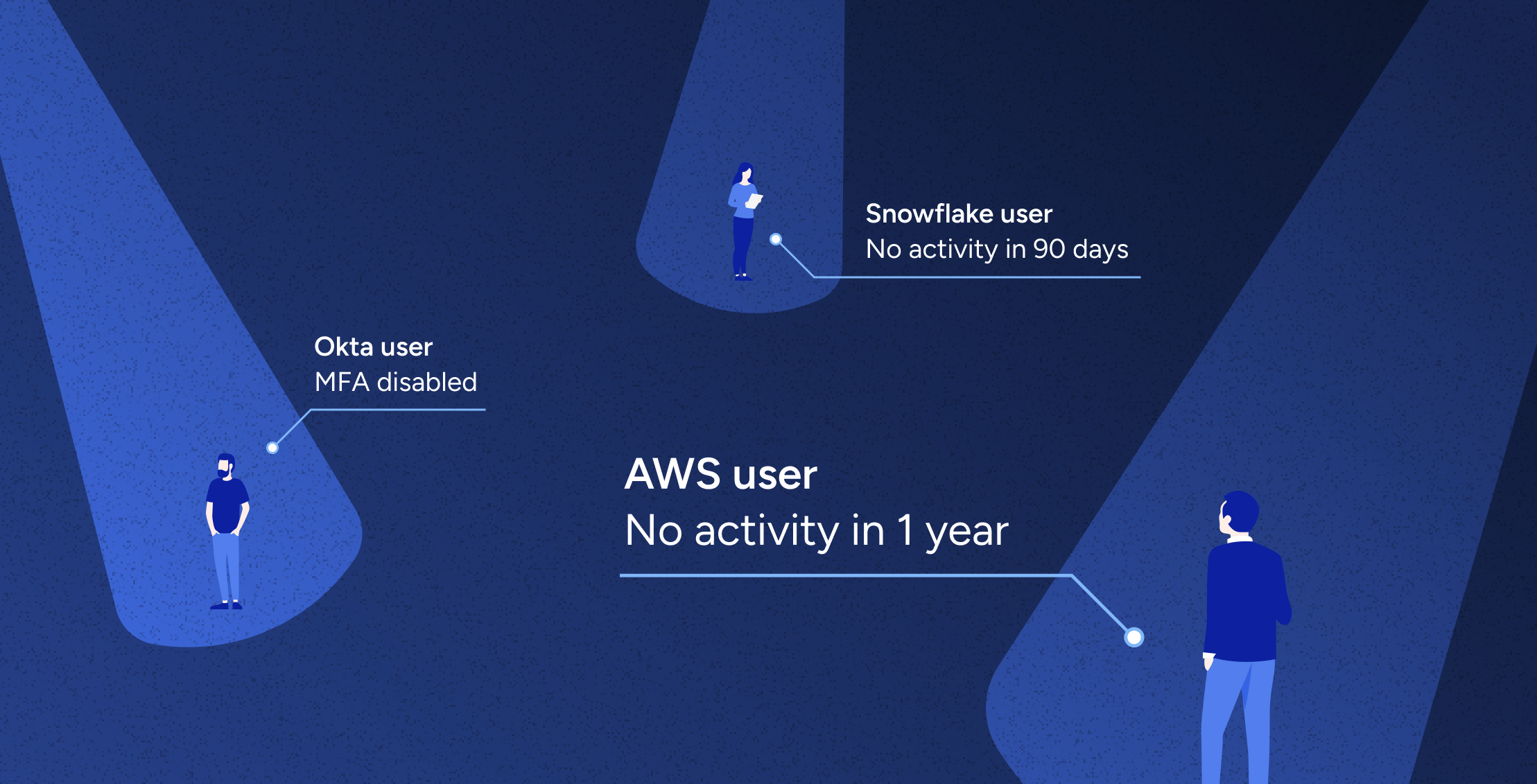
Automated Access Revocation & Remediation at Scale
Learn more -
Securing Snowflake: A CISO’s Guide to Effective Access Control
Learn more -
Acess AI: Introducting the Future of Identity Security
Learn more -
What is SaaS Sprawl?
Learn more
-
Where Non-Human Identities (NHIs) and Human Identities Converge: A Comprehensive Approach to Identity Security
Learn more -

Principle of Least Privilege Explained: Best Practices
Learn more -

Snowflake Roles Best Practices: Steps to Least Privilege
Learn more -
AWS Guide: Access Governance, Security, Compliance & Roles [2024]
Learn more -
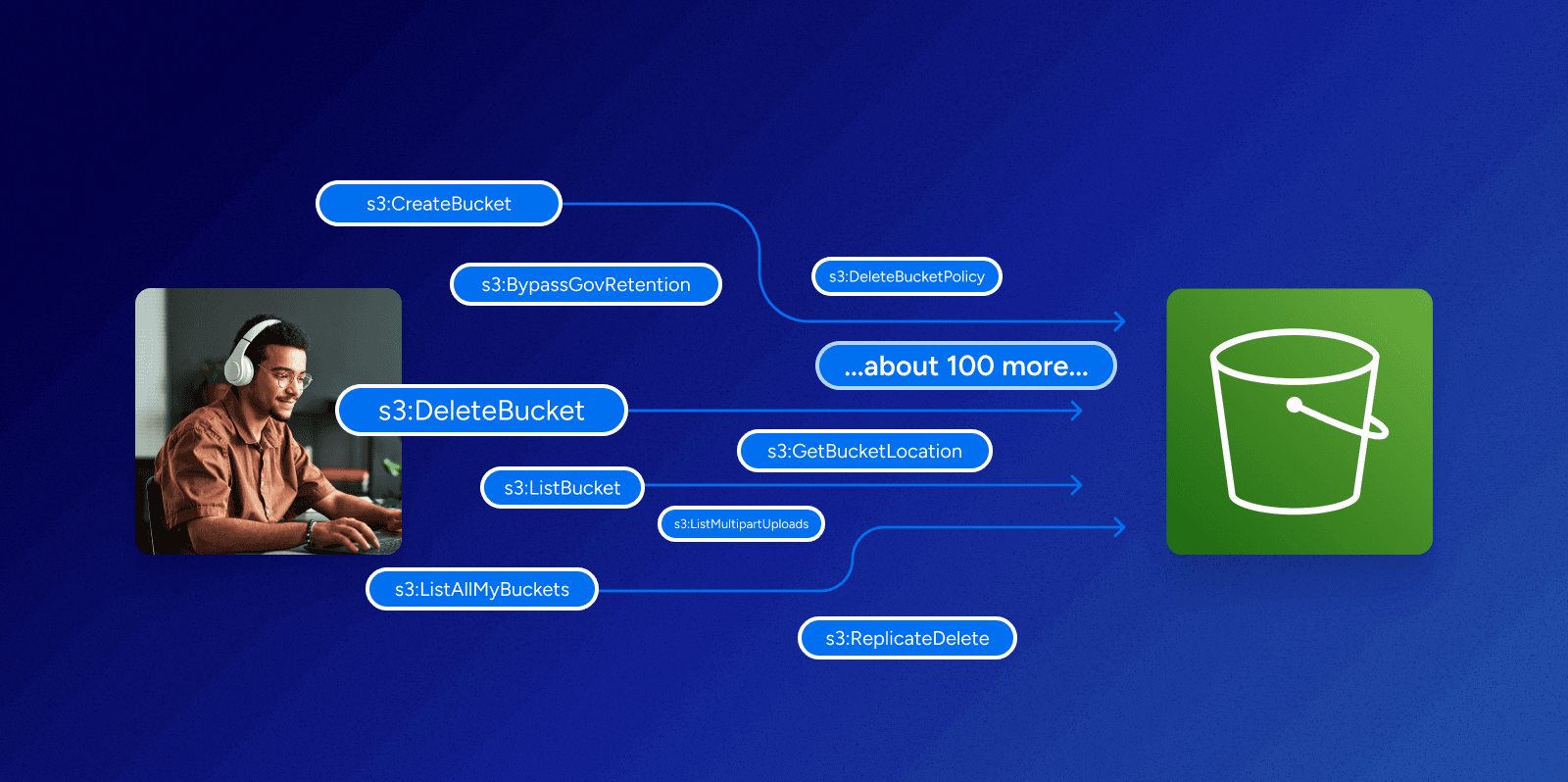
Can you make sense of permissions in AWS?
Learn more
-

Beyond the Buzzwords: Identity, Zero Trust, and Digital Transformation
Learn more -
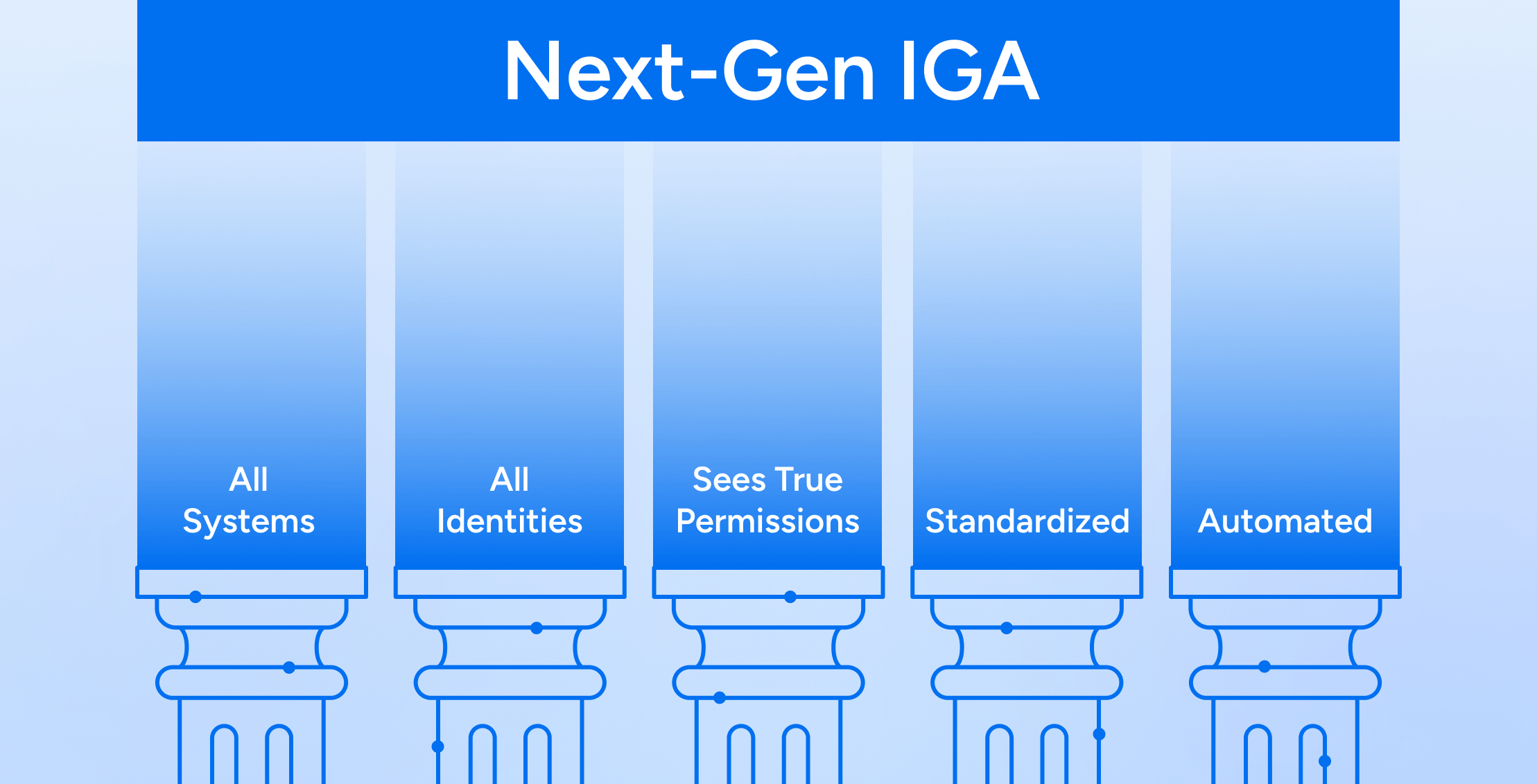
The Five Tenets of Next-Gen IGA
Learn more -

Posture of Access, 3 Pillars of Least Privilege
Learn more -

Groundhog day in identity security
Learn more -
Charting a Path for the Future of Identity Security
Learn more -

Identity governance in the cloud era
Learn more
-
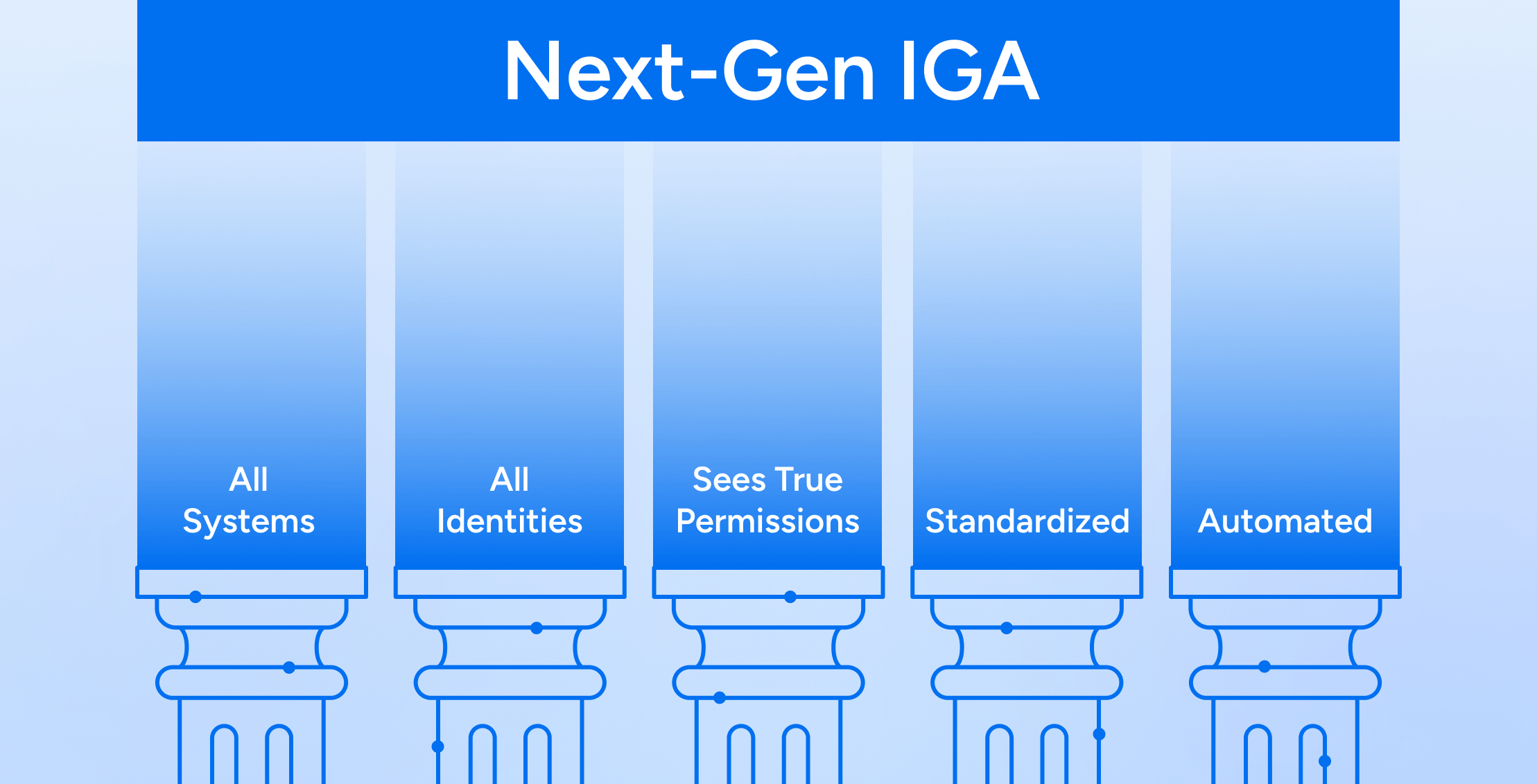
The Five Tenets of Next-Gen IGA
Learn more -
IBM Cost of a Data Breach Report: AI Security Cost Reduction
Learn more -
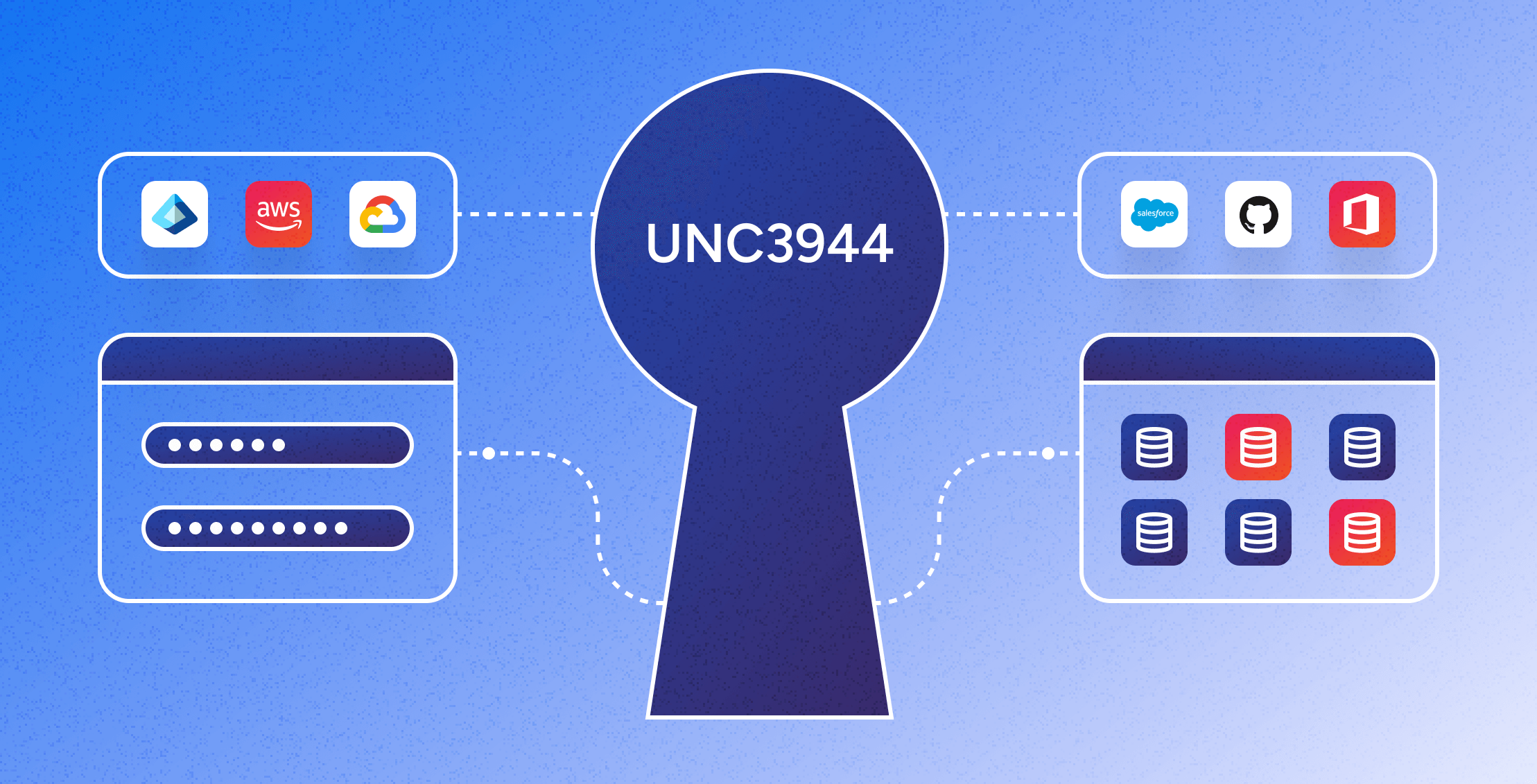
Mitigating the UNC3944 Threat: The Power of Modern Identity Security Platforms
Learn more -

Identity Security Spotlight: Ransomware attack on Ascension
Learn more -

Identity Security Spotlight: Microsoft CISA Investigation
Learn more -

Veza welcomes Mike Towers as Chief Security & Trust Officer
Learn more
No results found.
-

Ransomware supply chain threats: What made a global automotive company shut their plants this past spring?
Learn more -

BlackHat USA 2022 Recap – 25 years of InfoSec
Learn more -
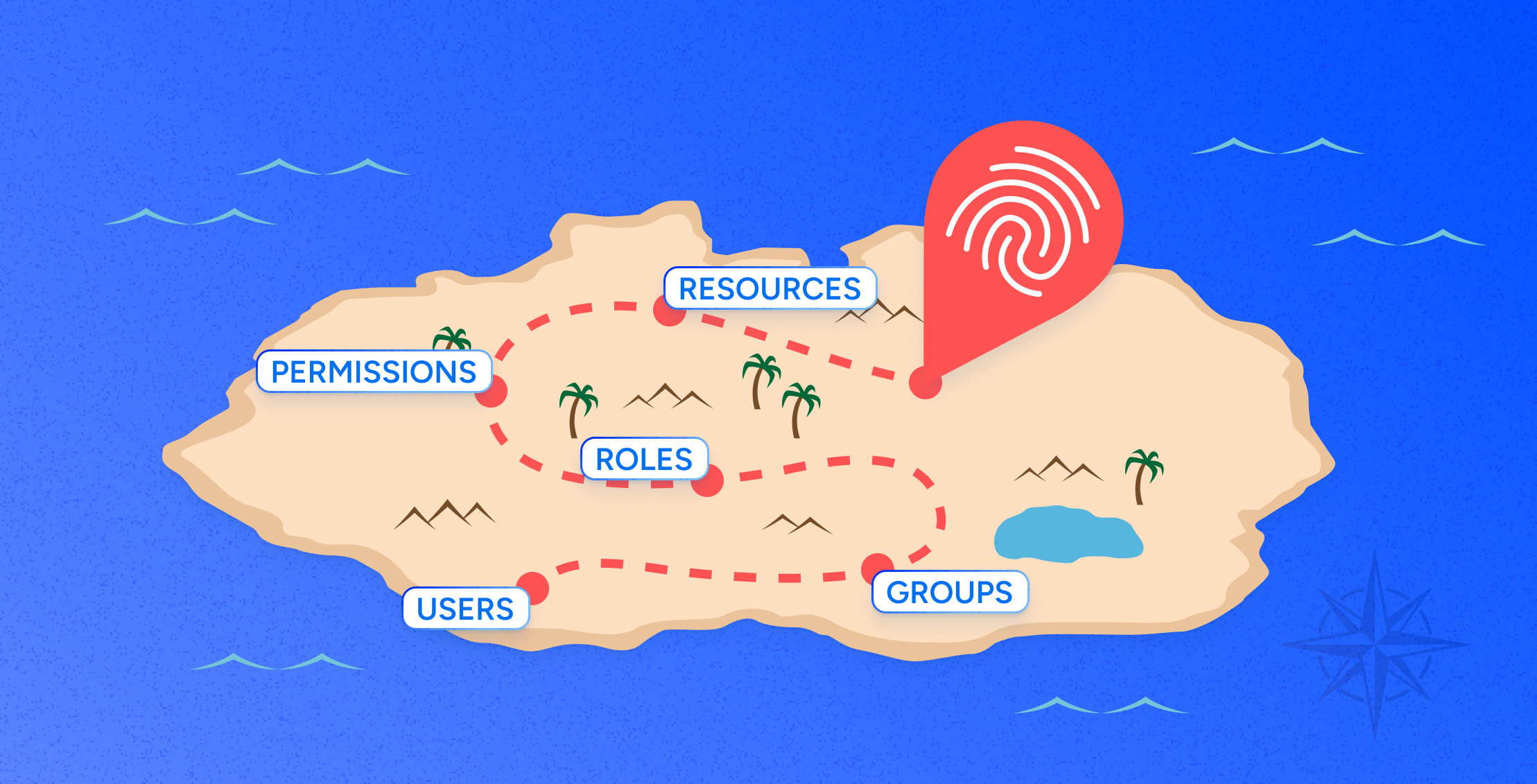
RBAC vs ABAC: Access Control Explained
Learn more -
Identity-Security Trends: Expectations vs Reality in Securing Data
Learn more -
Identiverse 2022 – where are we after a rapid move to cloud data?
Learn more -
5 Keys To Securing Your Data in a Multi-Cloud Environment
Learn more