Blog
-
 Identity Security
Identity SecurityUnderstanding ISPM: Closing the Identity Gap with Identity Security Posture Management
ISPM is a new category of identity security designed to help organizations continuously monitor and manage identity risk across cloud, SaaS, and hybrid environments. Learn how Identity Security Posture Management works, why it matters, and how Veza enables it. -
 Identity Security
Identity SecurityVeza Access AI – Applications of Gen AI for Identity Security Use Cases
Veza Access AI transforms identity security by enabling natural language queries to navigate complex access landscapes, empowering organizations to achieve least privilege effectively.
Explore our posts
-
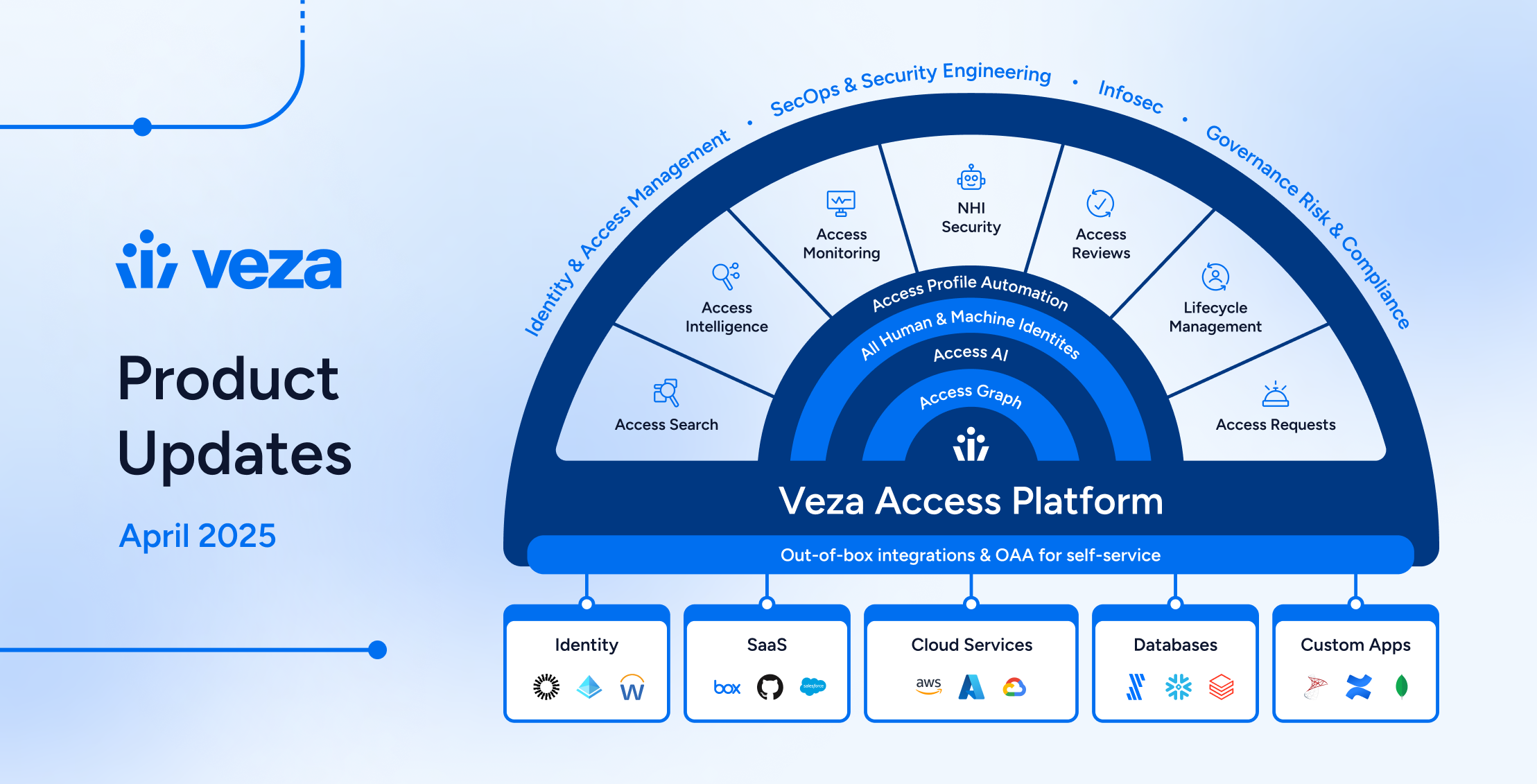
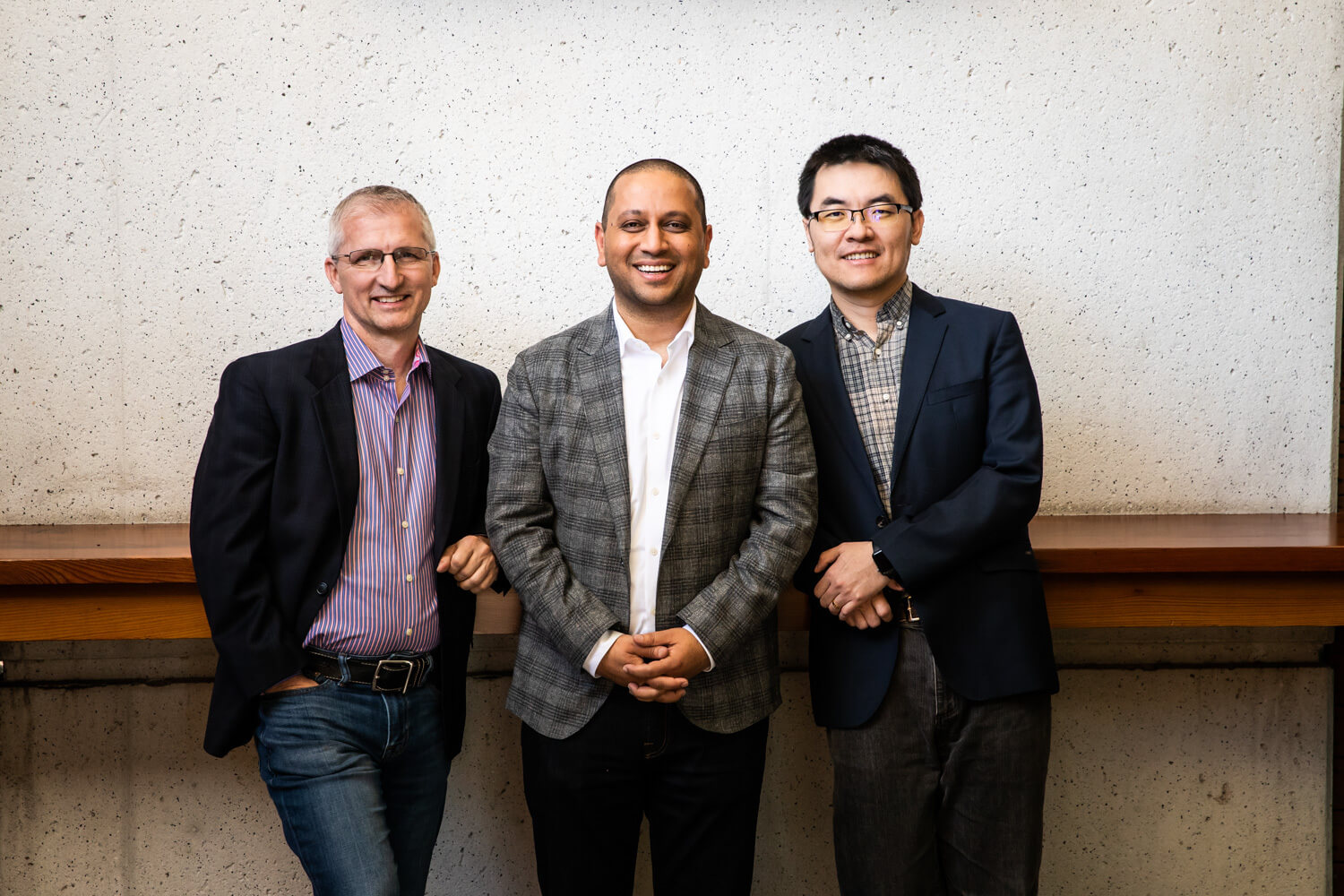
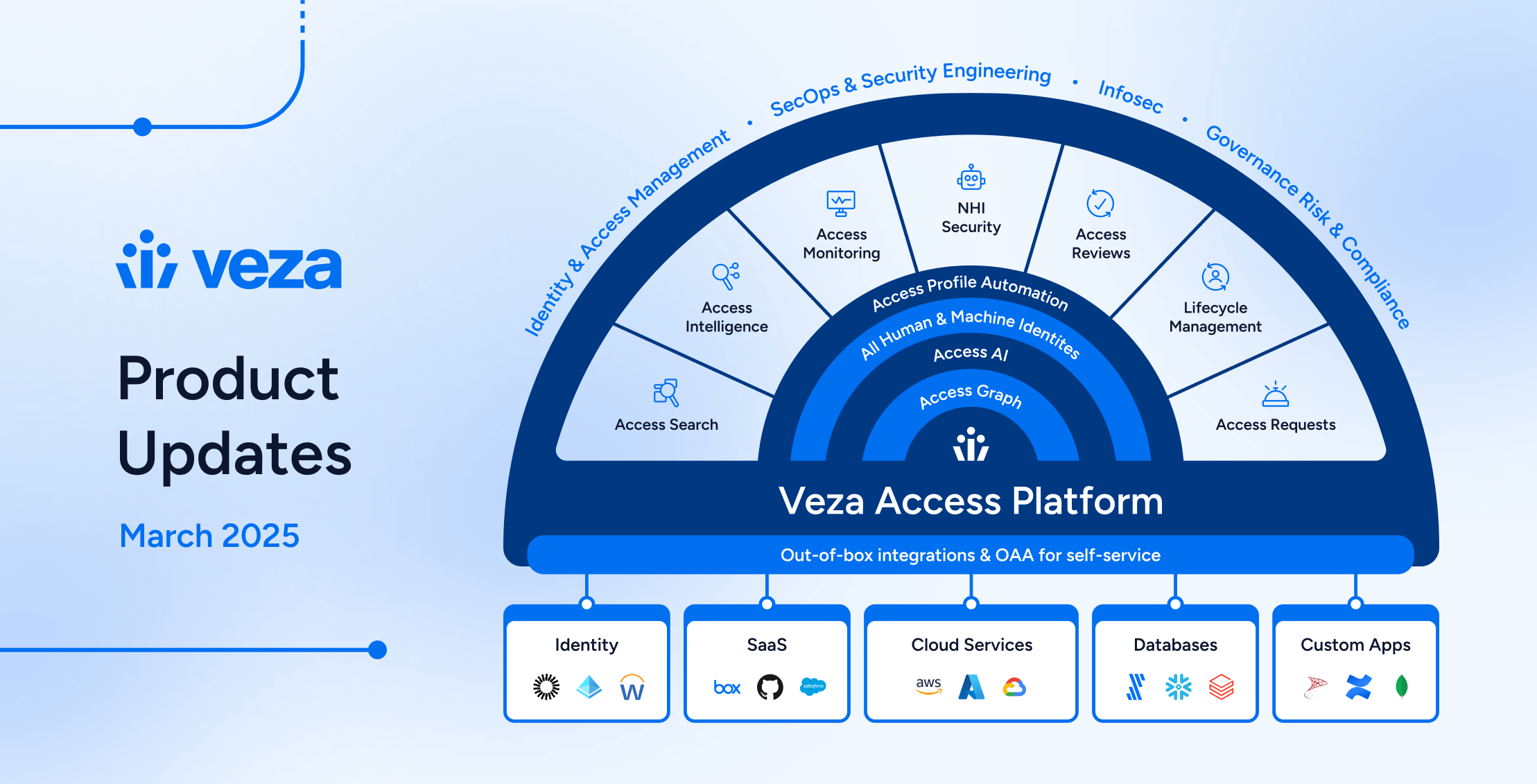
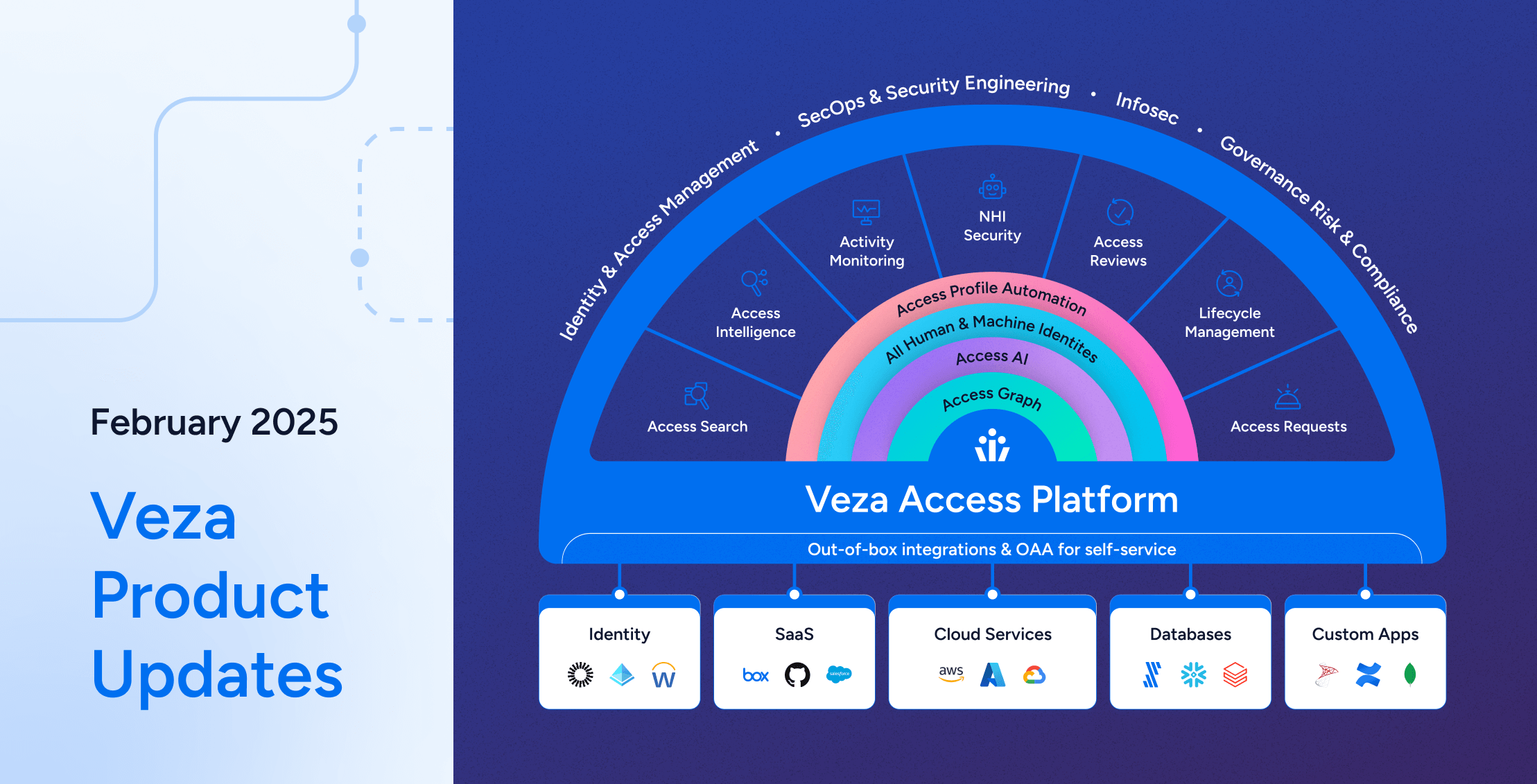
Building Veza’s Platform and Products
Learn more -
Veza Secures Strategic Investment from Capital One Ventures and ServiceNow Ventures to Accelerate Identity Security
Learn more -

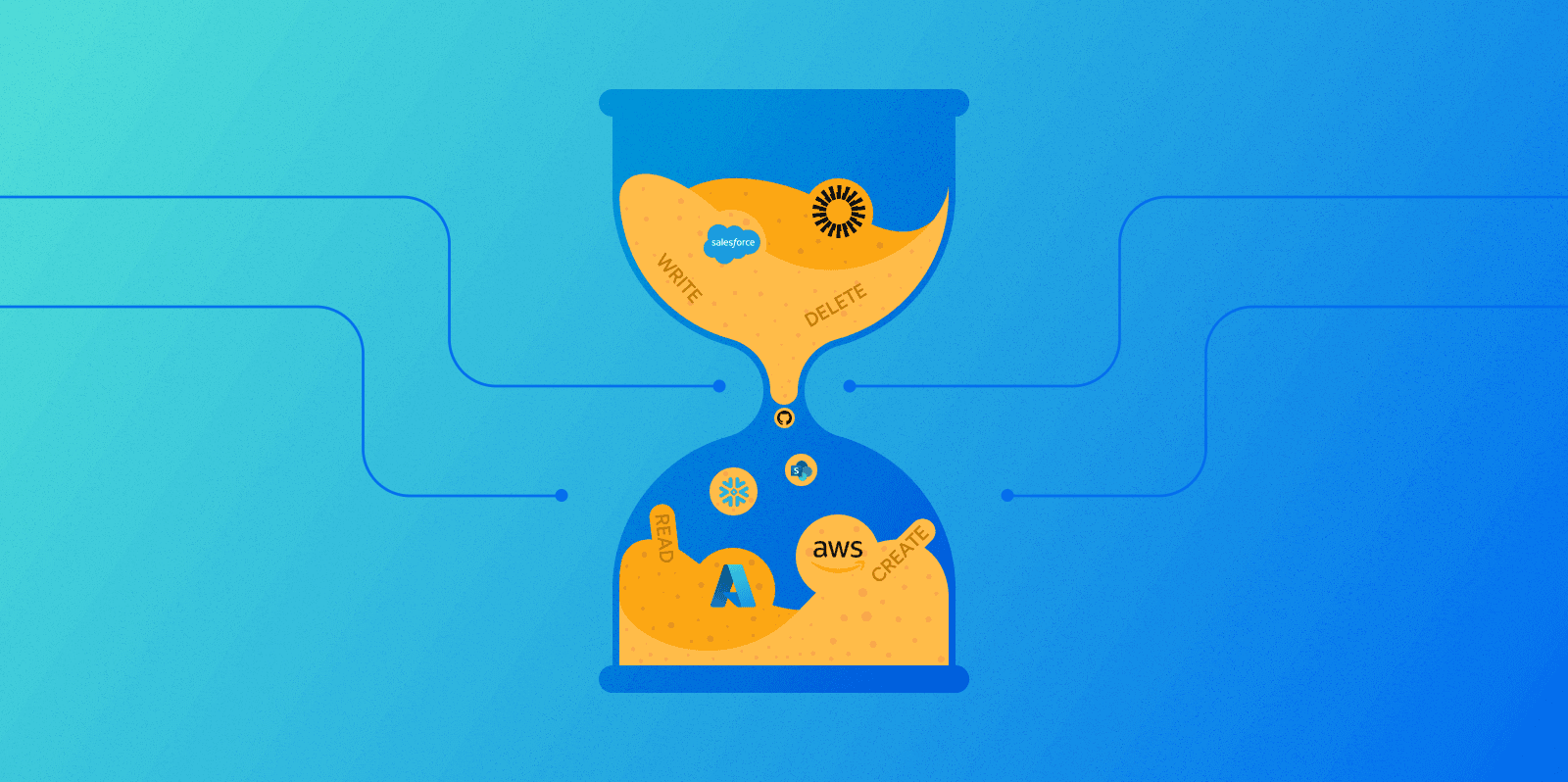
The Principle of Least Privilege Explained
Learn more -
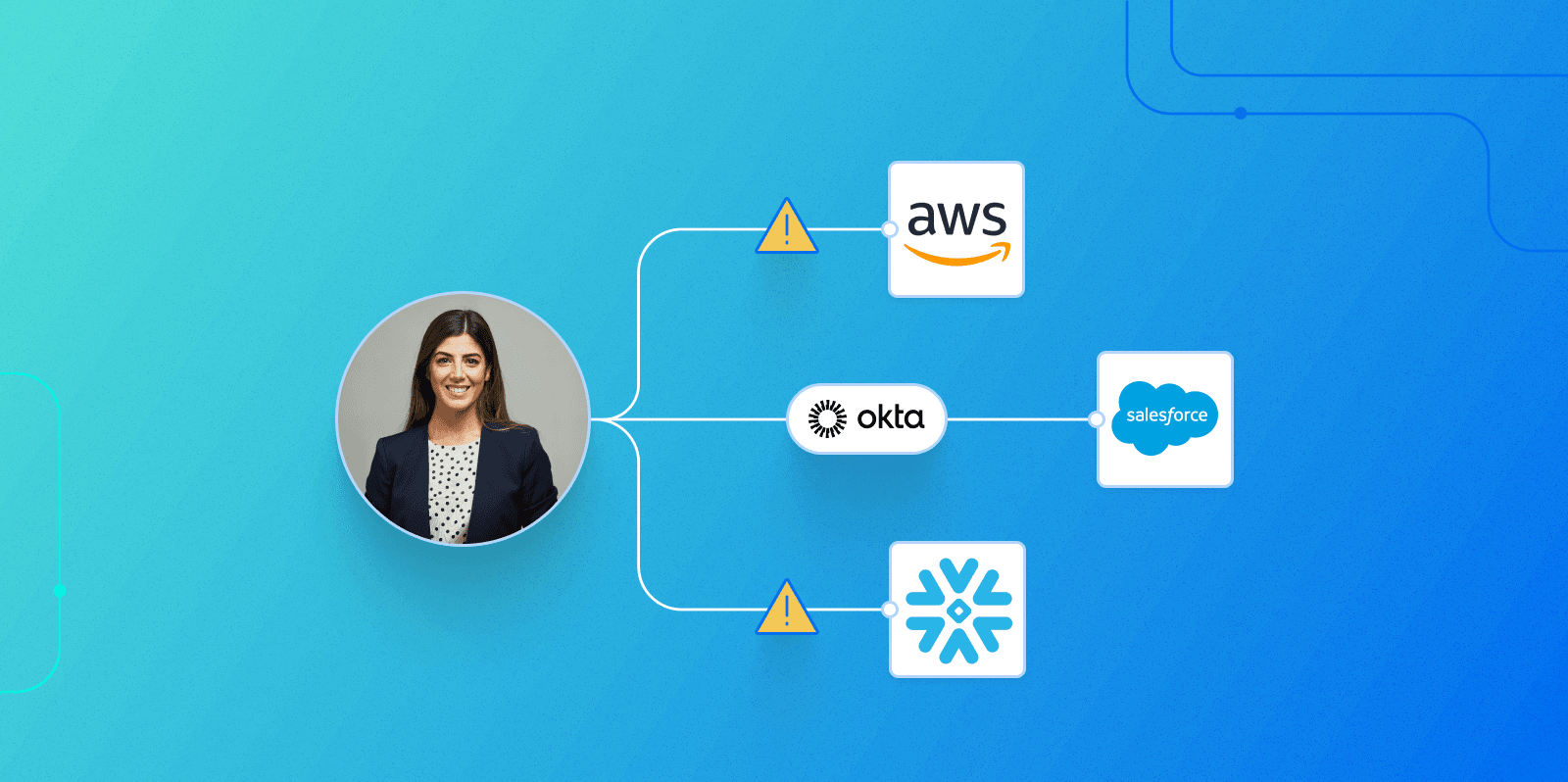
History of Hacks: Orphaned Accounts
Learn more -
The Age of Identity Security is here: Microsoft goes all-in on identity with Microsoft Entra
Learn more -
Veza Product Update – June 2023
Learn more
-
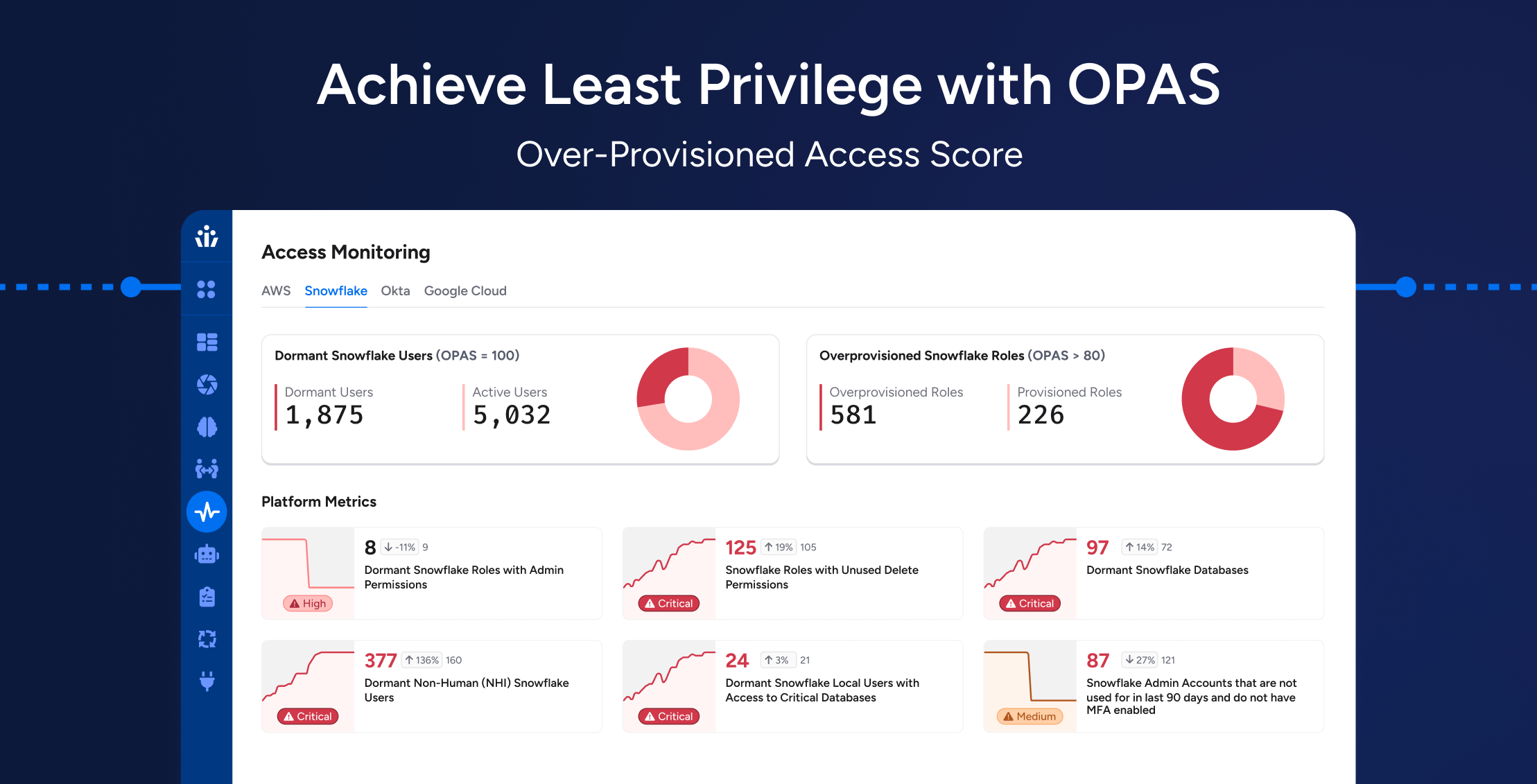
Achieving Least Privilege at Scale: How OPAS Helps Enterprises Reduce Hidden Access Risks
Learn more -
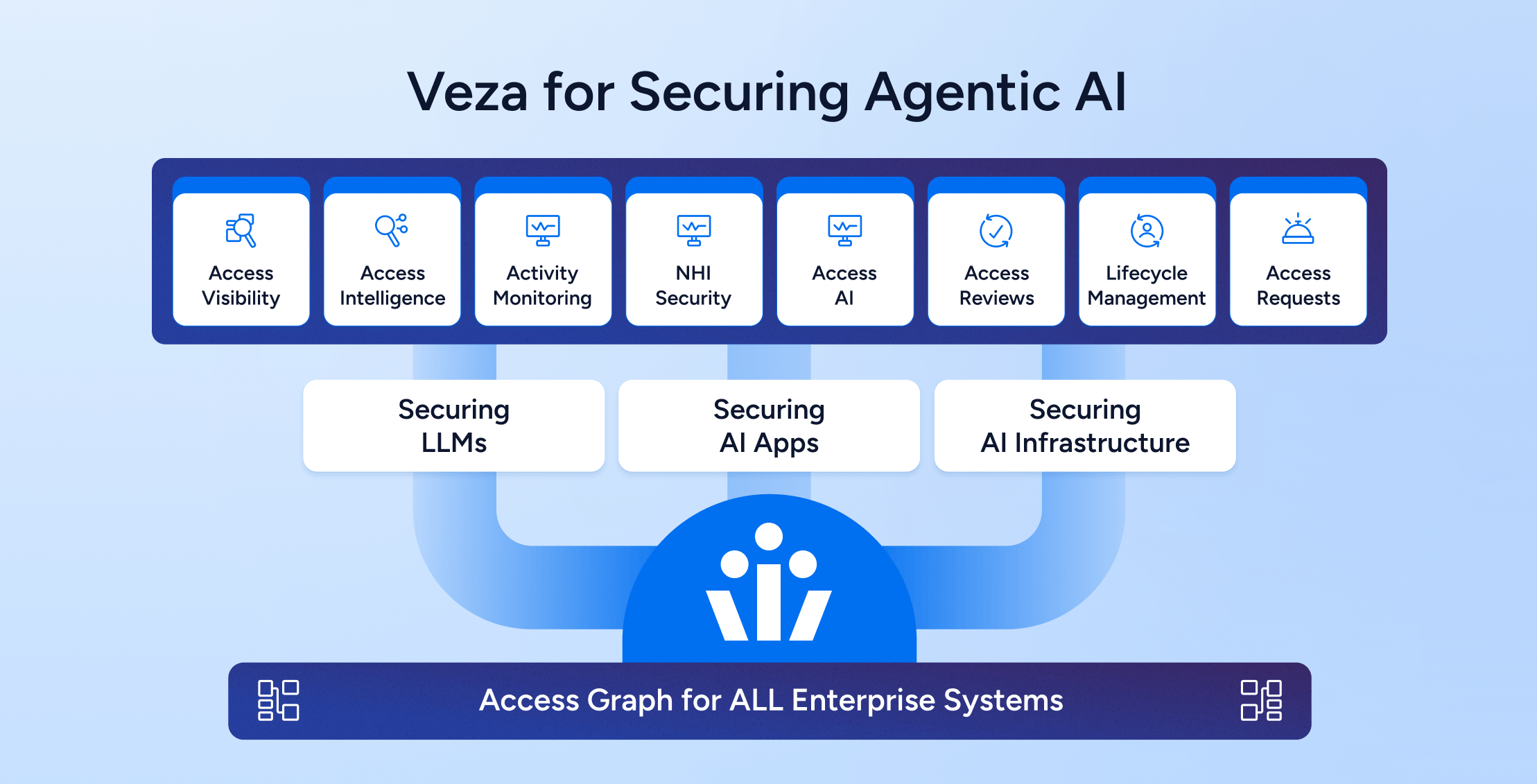
Trust as the Foundation for Agentic AI Architecture: Securing Access to all the AI layers – Models, Infra, AI Applications
Learn more -
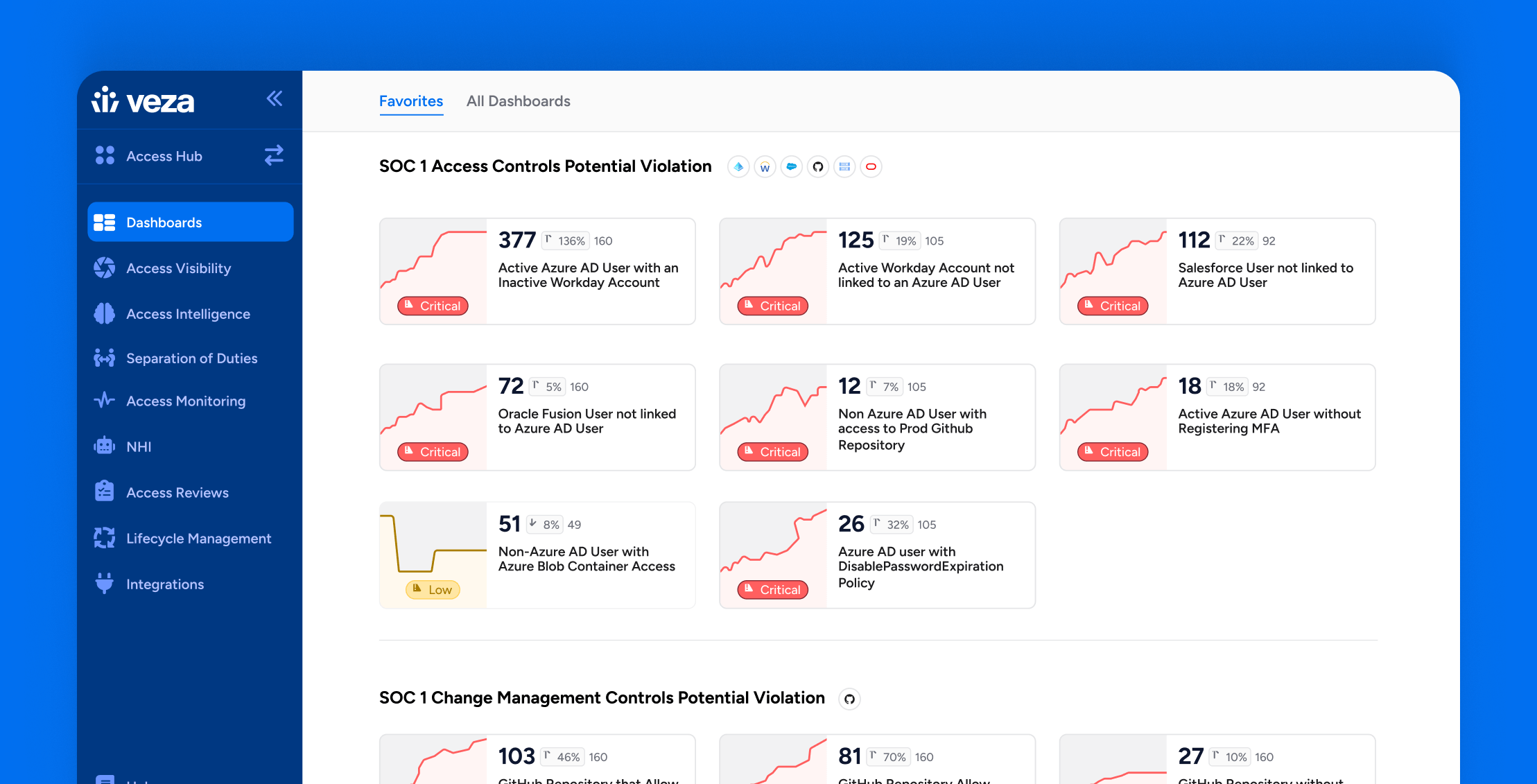
How Veza Strengthens SOC 1 Compliance: Common Control Failures & How to Fix Them
Learn more -
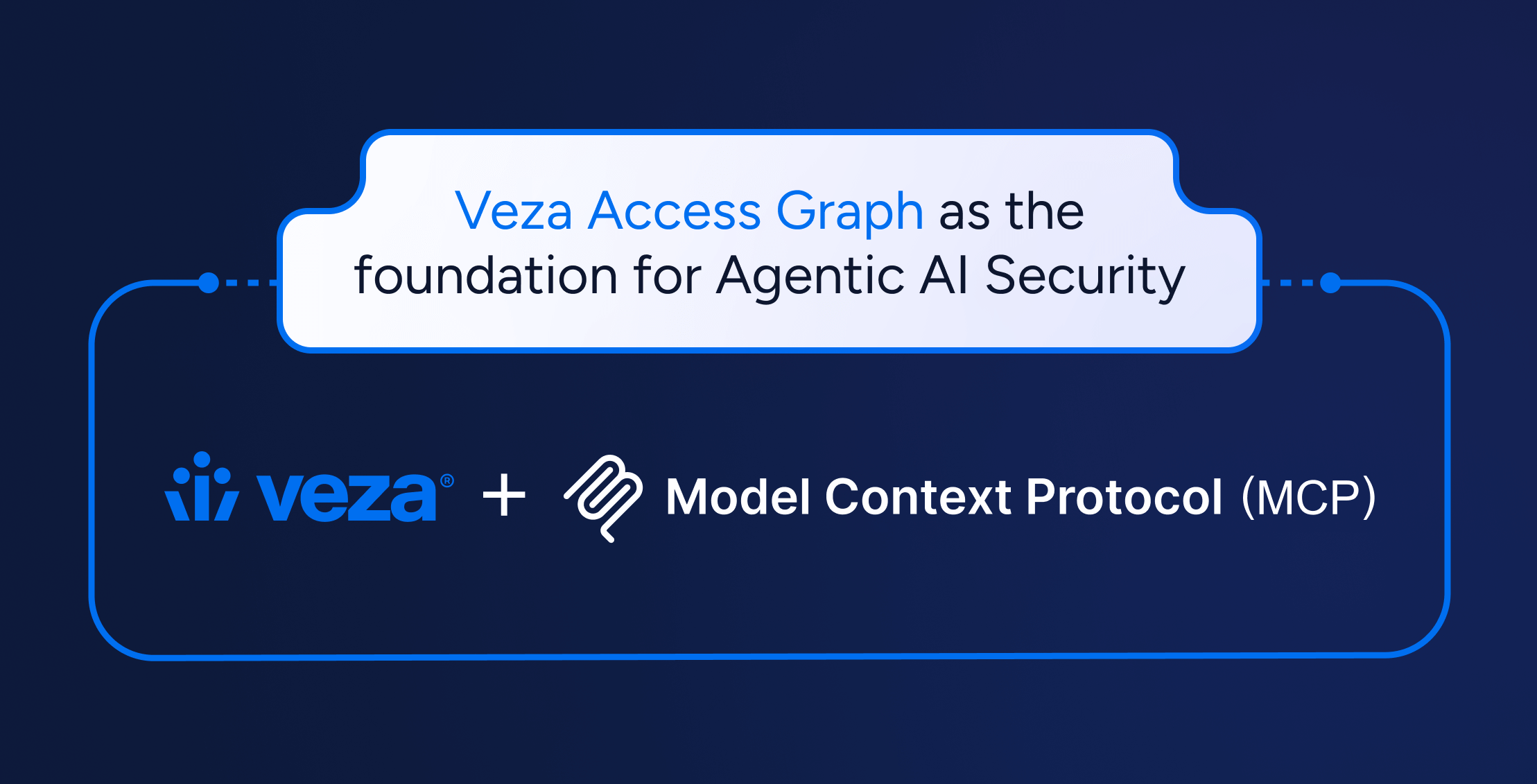
Model Context Protocol (MCP): Implications on identity security and access risks for modern AI-powered apps
Learn more
-
I Attended the Verizon Data Breach Session at RSA So You Don’t Have To:
Learn more -
Reflections from Gartner IAM London: Visibility Leads to Observability
Learn more -

Achieving DORA Compliance: A Practical Guide for Financial Organizations
Learn more -

Join us at Black Hat USA August 3 – 8, 2024
Learn more -

Join us at RSAC May 6-9, 2024
Learn more -

Veza @ AWS re:Invent
Learn more
-
A field guide to bad permissions part 4: policy-violating permissions
Learn more -
A field guide to bad permissions, part 3: excessive permissions
Learn more -
A field guide to bad permissions part 2: expired permissions
Learn more -
A field guide to bad permissions, part 1: ungoverned permissions
Learn more -
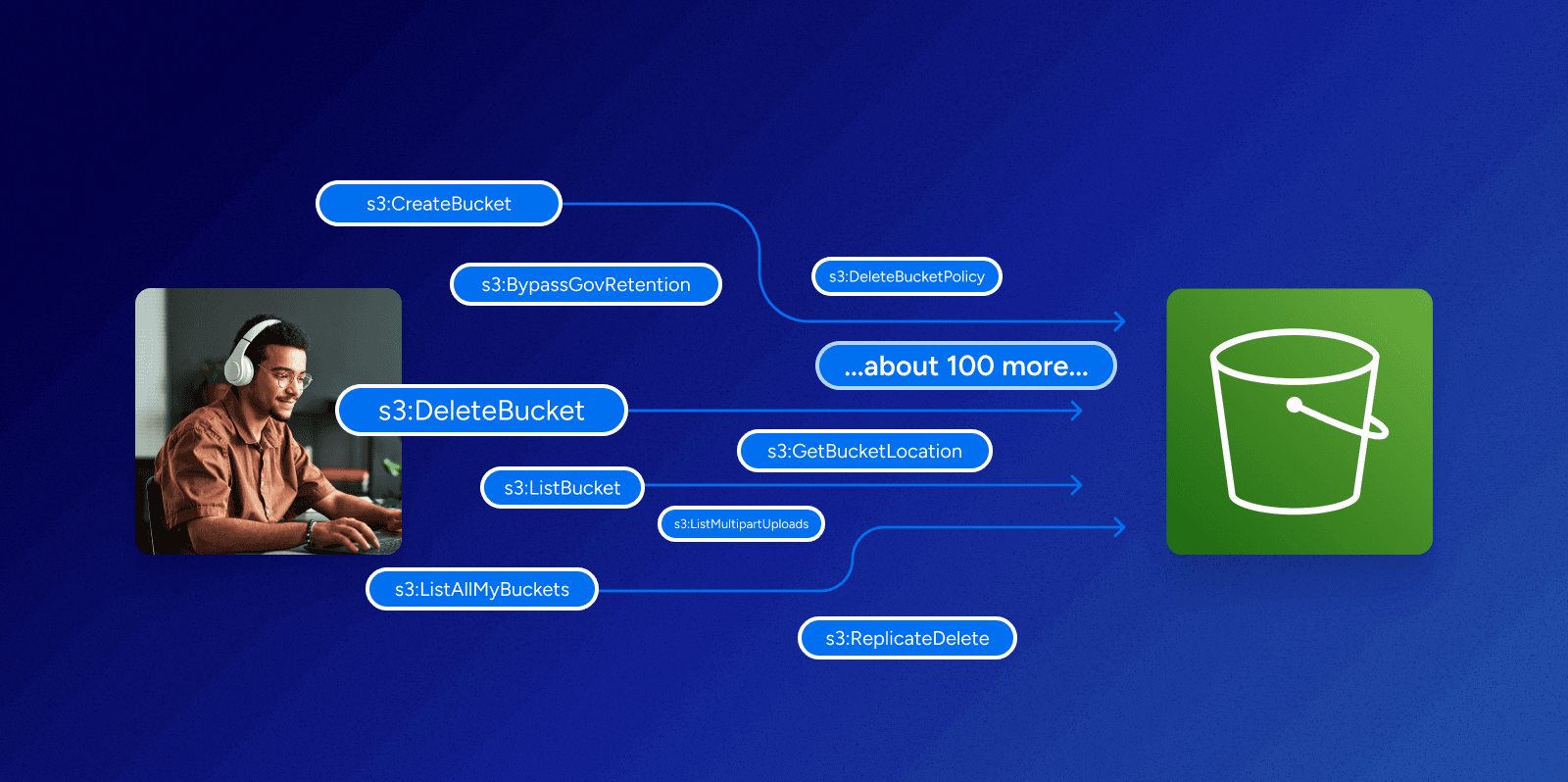
Can you make sense of permissions in AWS?
Learn more -

Veza @ AWS re:Invent
Learn more