Blog
-
 AI
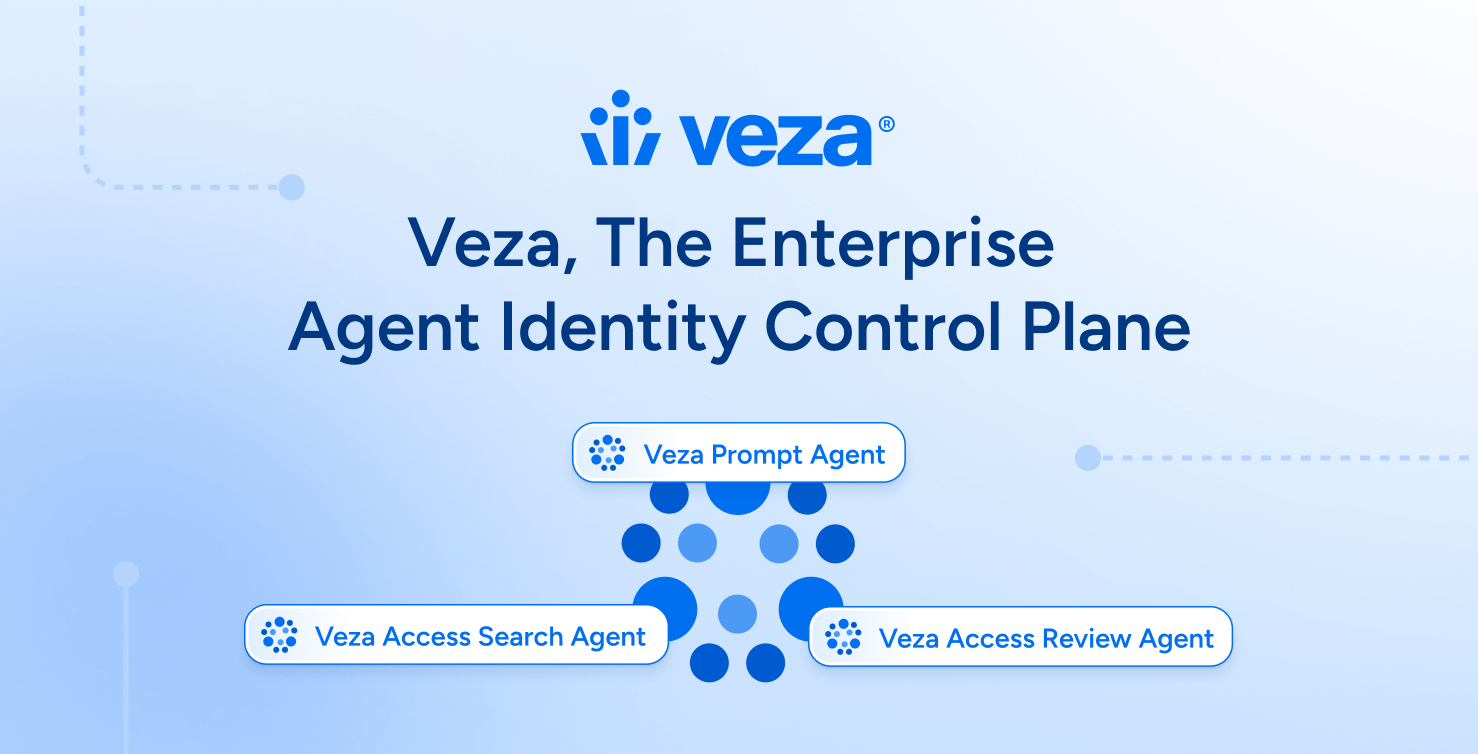
AIVeza – The Enterprise Agent Identity Control Plane
Veza’s 2026 State of Identity and Access Report found that in a typical enterprise, an average worker holds 96,000 entitlements, 38% of IdP accounts are dormant and only 55% of permissions are safe and compliant. The volume and complexity of identity-based attacks is exacerbated by the explosion of AI agents and non-human identities (NHIs). In […] -
 Company
CompanyServiceNow + Veza: A new chapter in identity security
Today marks a pivotal moment—not just for Veza, but for the entire identity security industry. I’m deeply proud to share that ServiceNow has signed a definitive agreement to acquire Veza. Together, we will accelerate the mission to secure identity across the modern enterprise as organizations transition into the era of agentic identities. When Maohua, Rob, […]
Explore our posts
-

Beyond the Buzzwords: Identity, Zero Trust, and Digital Transformation
Learn more -
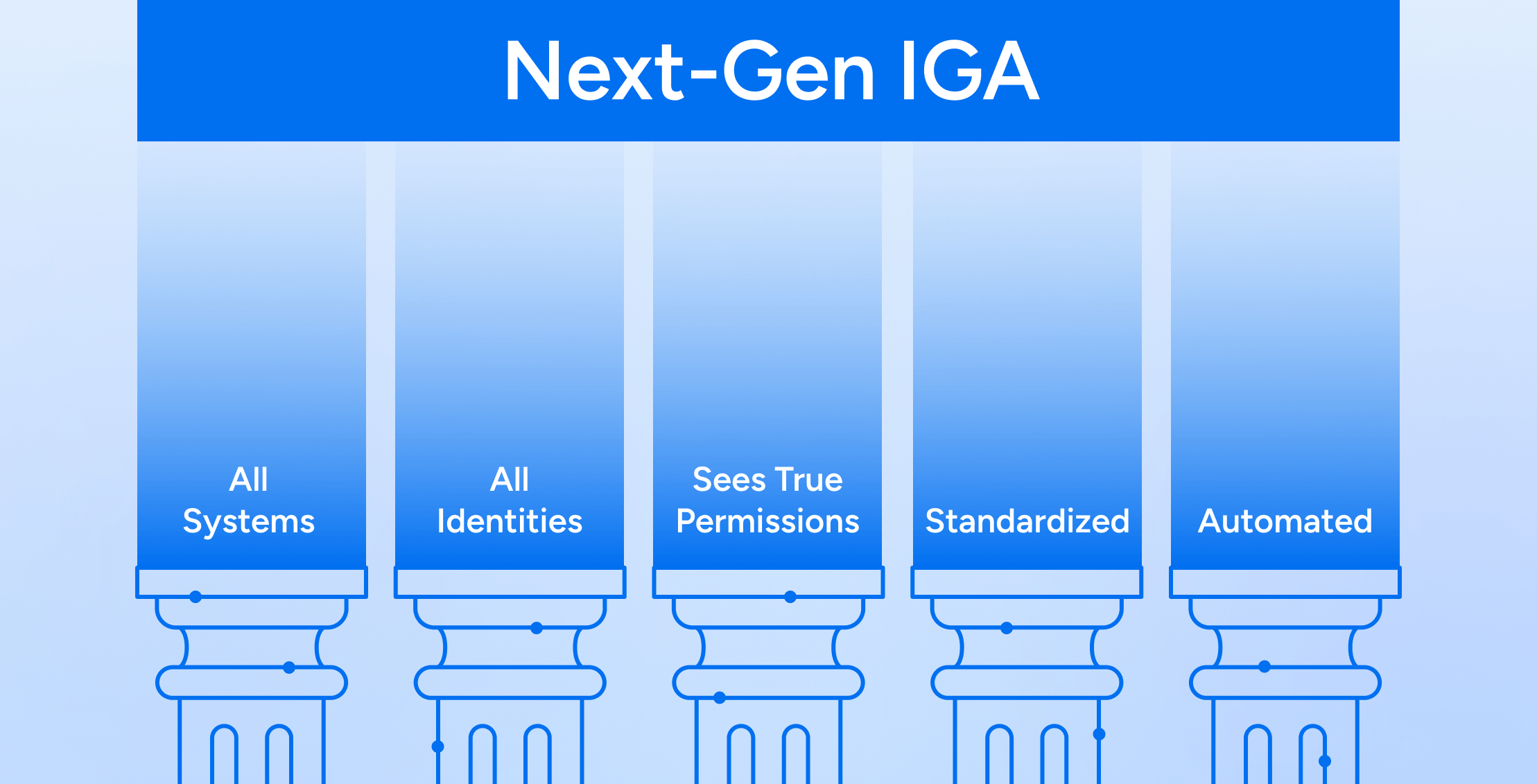
The Five Tenets of Next-Gen IGA
Learn more -

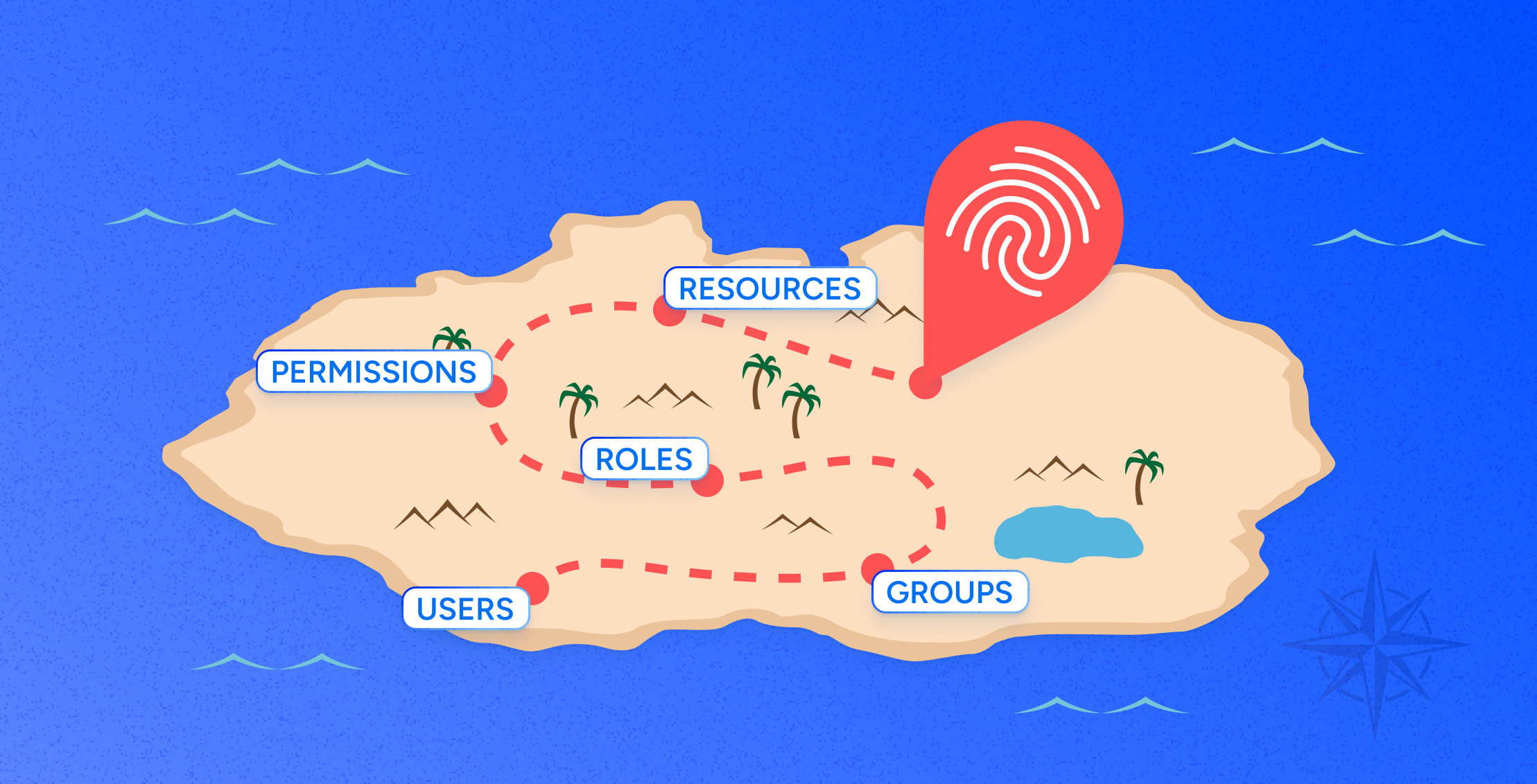
Posture of Access, 3 Pillars of Least Privilege
Learn more -

Groundhog day in identity security
Learn more -
Charting a Path for the Future of Identity Security
Learn more -

Identity governance in the cloud era
Learn more
-

Unveiling Least Privilege Vulnerabilities with Stryker: How Veza Access Platform Empowers Security Teams to Prevent Device Wipe Breaches Related To Microsoft AD and Intune environments
Learn more -
Achieving DORA Compliance: A Practical Guide for Financial Organizations
Learn more -
I Attended the Verizon Data Breach Session at RSA So You Don’t Have To:
Learn more -
Reflections from Gartner IAM London: Visibility Leads to Observability
Learn more -

Join us at Black Hat USA August 3 – 8, 2024
Learn more -

Veza @ AWS re:Invent
Learn more
-

10 top privileged access management (PAM) software solutions for 2025
Learn more -
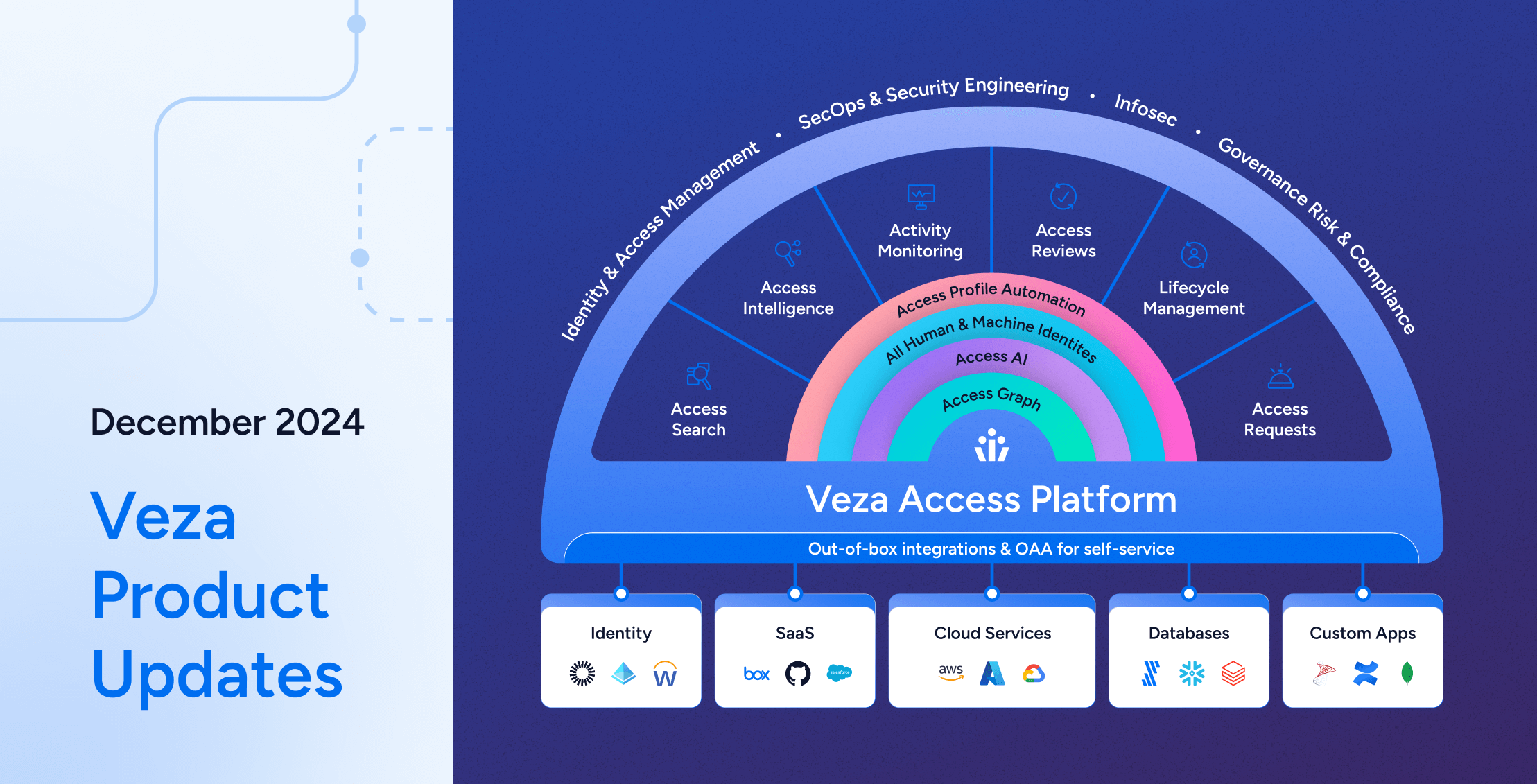
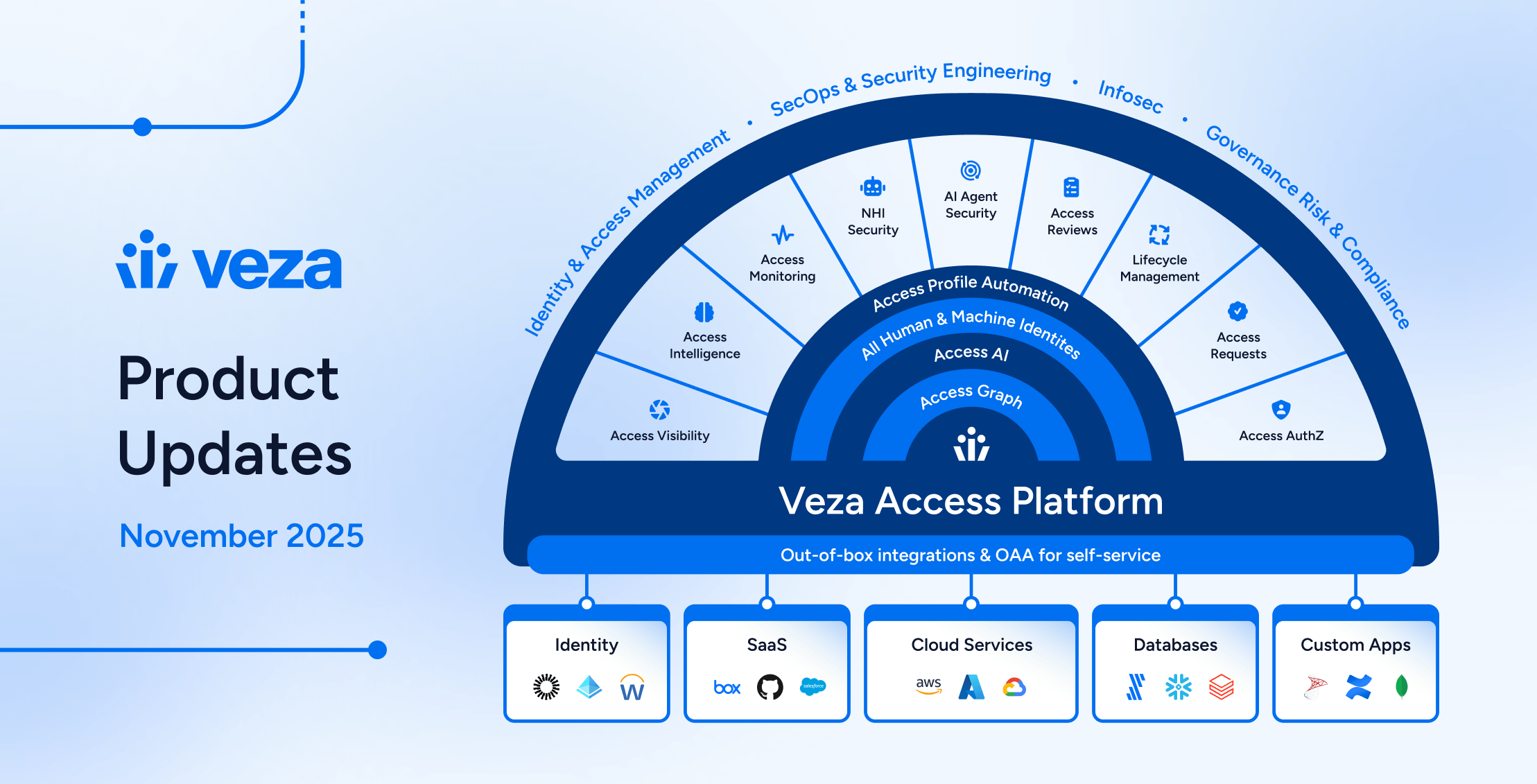
Veza Product Updates – December 2024
Learn more -
Demonstrating PCI DSS 4.0 Compliance with Veza’s Identity Security Platform
Learn more -

Complete SailPoint Review & Top Alternatives [2024]
Learn more -

Posture of Access, 3 Pillars of Least Privilege
Learn more