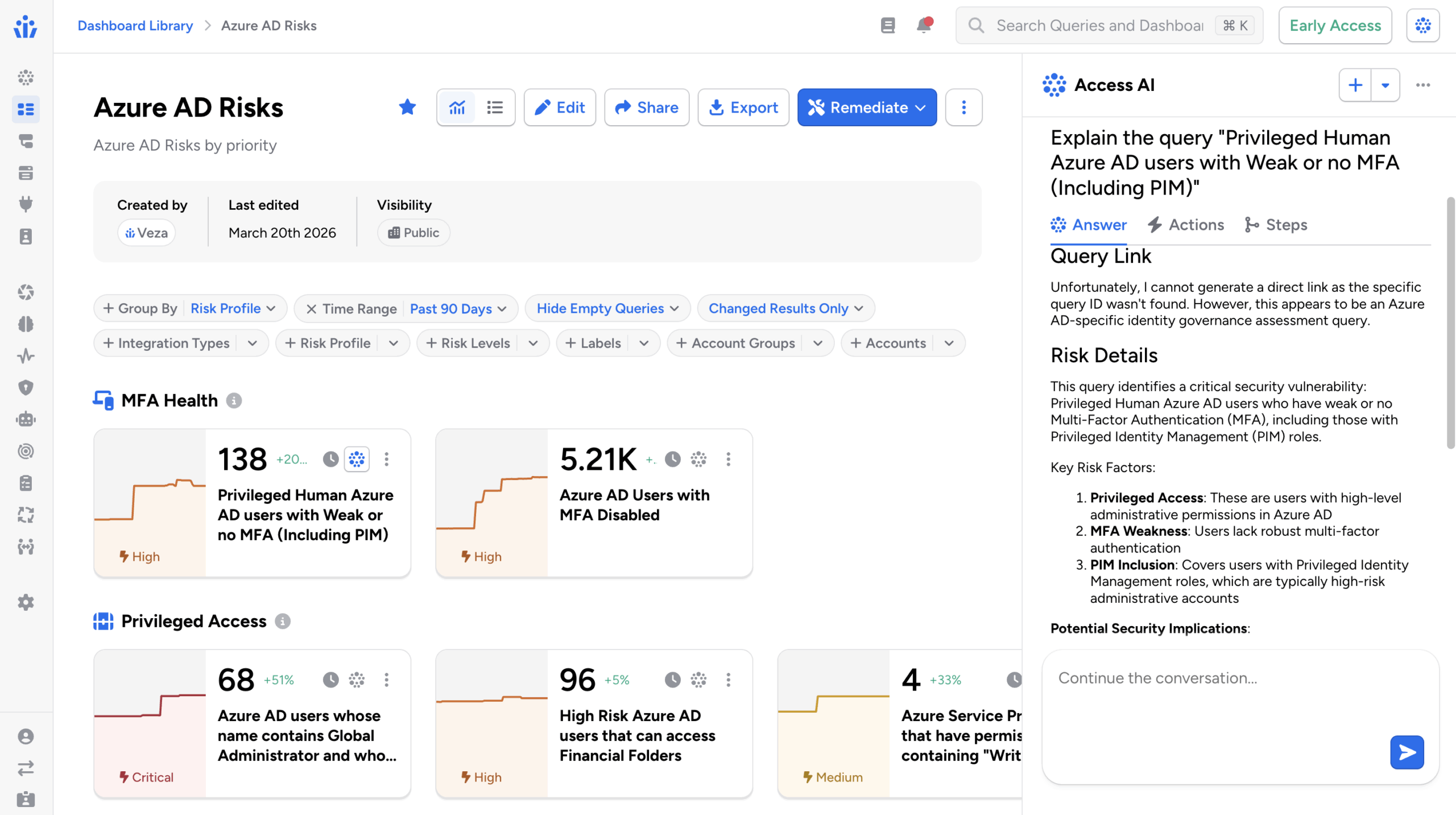
Your Agents Have Access. Now You Do Too.
AI agents are already running in your AWS environment. Security teams often face a significant visibility gap: they may not know which agents exist, what models they run, or what data they can reach. This creates a critical “blast radius” issue when security incidents occur.
In many enterprises, the deployment of agents on Amazon Bedrock AgentCore involves multiple teams—developers building the agents, platform teams provisioning IAM roles, and data engineers configuring memory stores. Without a unified view, governing these complex interactions is nearly impossible. Today, Veza is closing that gap.
From Bedrock Agents to AgentCore — One Authoritative View
Veza initially launched AI Agent Security to provide visibility for classic Amazon Bedrock Agents. With the addition of support for Amazon Bedrock AgentCore, Veza now covers the production runtime platform where agents built with any framework (such as LangGraph, CrewAI, or OpenAI Agents SDK) reside.
| Feature | Amazon Bedrock Agents | Amazon Bedrock AgentCore |
|---|---|---|
| Primary Role | Orchestration layer for managed invocations. | Production runtime platform for any framework. |
| Lifecycle | Short-lived, managed sessions. | Long-running serverless compute (up to 8 hours). |
| Framework Support | Managed Bedrock orchestration. | Strands, LangGraph, CrewAI, Google ADK, etc. |
| Capabilities | Knowledge bases and action groups. | Persistent memory and unified tool gateways. |
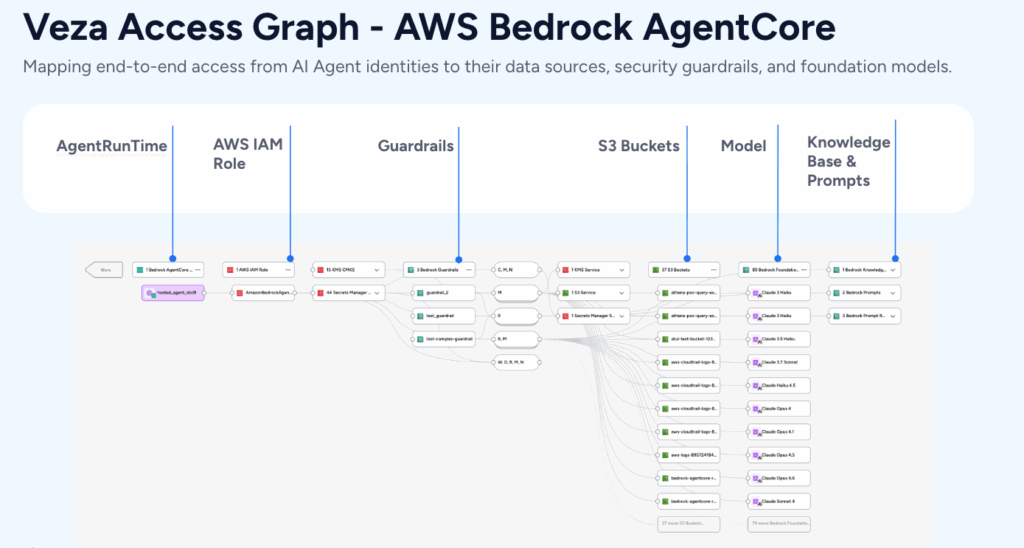
What Veza Discovers and Governs in AgentCore
AgentCore spans several functional subsystems and resource types. Veza models the critical components that impact access control:
- Agent Runtimes: The compute units and invocation surface (Runtime Endpoints).
- Gateways: Unified tool routing layers and downstream targets.
- Memory: Persistent context stores for reading and writing.
- Execution Tools: Code Interpreters and Browser tools with specific VPC and IAM roles.
- Models: Bedrock Foundation, and Imported models.
- Governance: Online Evaluation Configs.
Answering Critical Security Questions
1. Outbound: What can this agent actually reach?
Veza models the complex web of IAM trust policies and permissions as a clear graph path. This allows security teams to move away from manual policy reviews and use precise queries.
AgentCore Resource → CAN_ASSUME_ROLE → IAM Role → HAS_PRIVILEGE → AWS Resource (S3/Lambda/etc.)- Which agents can read from specific PII buckets?
- Which agents can invoke sensitive payment processing functions?
- Is the execution role granting unintended privileges?
2. Inbound: Who can manage and invoke these agents?
Veza maps access to the AgentCore resources themselves, ensuring that only authorized personnel can manage the AI lifecycle.
IAM User/Role/Group → HAS_EFFECTIVE_PERMISSION → AgentCore Runtime/Gateway/Memory- Who has permission to invoke production agents?
- Can a developer escalate privileges through agent runtime access?
- Who can modify the gateway routing to internal APIs?
The Strategic Importance of Agent Governance
Every AI agent is a non-human identity with a real-world blast radius. Overly permissive IAM roles can lead to data exfiltration or unauthorized actions. As the number of agents grows, the Veza Access Graph provides a single source of truth that unifies human identity, service accounts, and agent identity.
Getting Started
Veza AI Agent Security with Amazon Bedrock AgentCore support is available now for Veza customers. Existing users can enable the AgentCore data source within their current AWS integration without a separate deployment.