Next-Gen IGA
Stop governing in the dark. Veza’s Next-Gen IGA automates provisioning, deprovisioning, and access reviews based on effective permissions, with deep visibility into your entire identity lifecycle.
Why use Veza
Key Benefits
Unify Governance Across All Identities – Replace manual processes and fragmented governance tools with a single platform that governs human, non-human, and AI agent access across every system.
Operationalize in Minutes – Get started immediately with hundreds of out-of-the-box integrations; instantly launch 1-step access review campaigns to improve visibility, reduce risk and enforce the principles of least privilege.
Simplify Lifecycle Management – Automate joiner, mover, and leaver workflows and empower teams with self-service, just-in-time access requests.
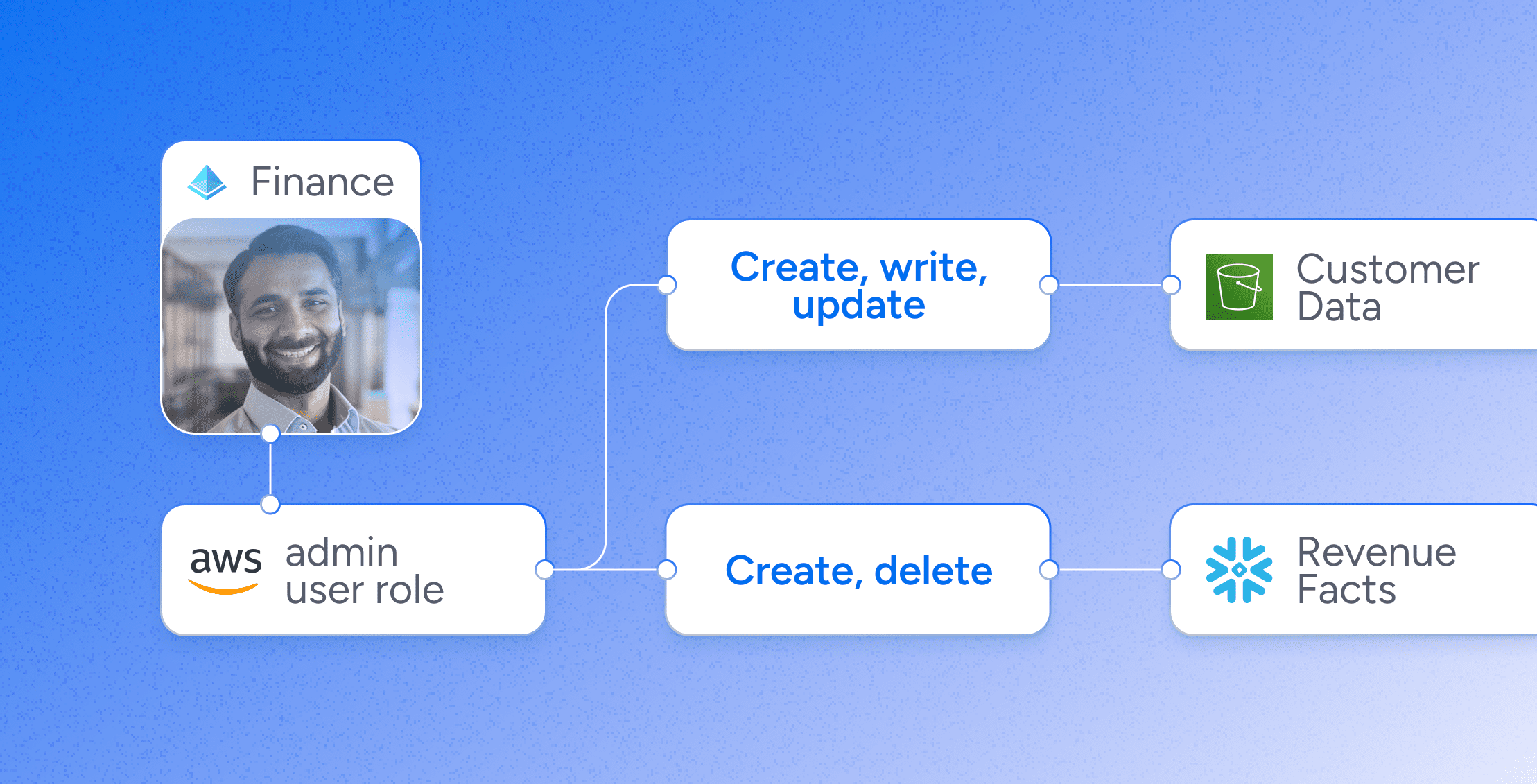
Enforce Least Privilege – Detect and remediate excessive permissions with data-driven insights into effective permissions across identities, roles, and resources.
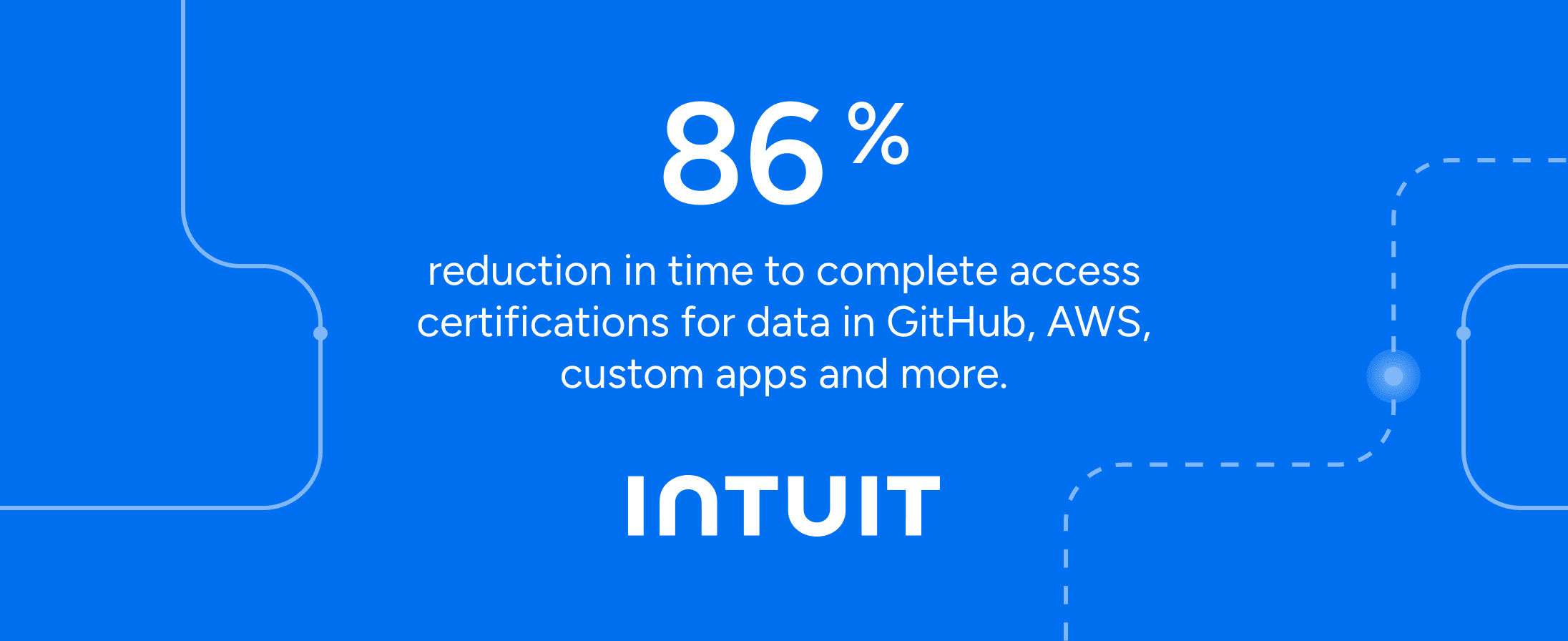
Realize Continuous Compliance – Prove access control effectiveness with audit-ready reports and meet compliance requirements such as SOX, ISO 27001, SOC 2, and GDPR.
Key Features
Unify Access Visibility – Map your entire identity ecosystem – users, NHIs, AI agents, groups, roles, entitlements, policies, permissions, and resources to understand who has access to what and what they can actually do.
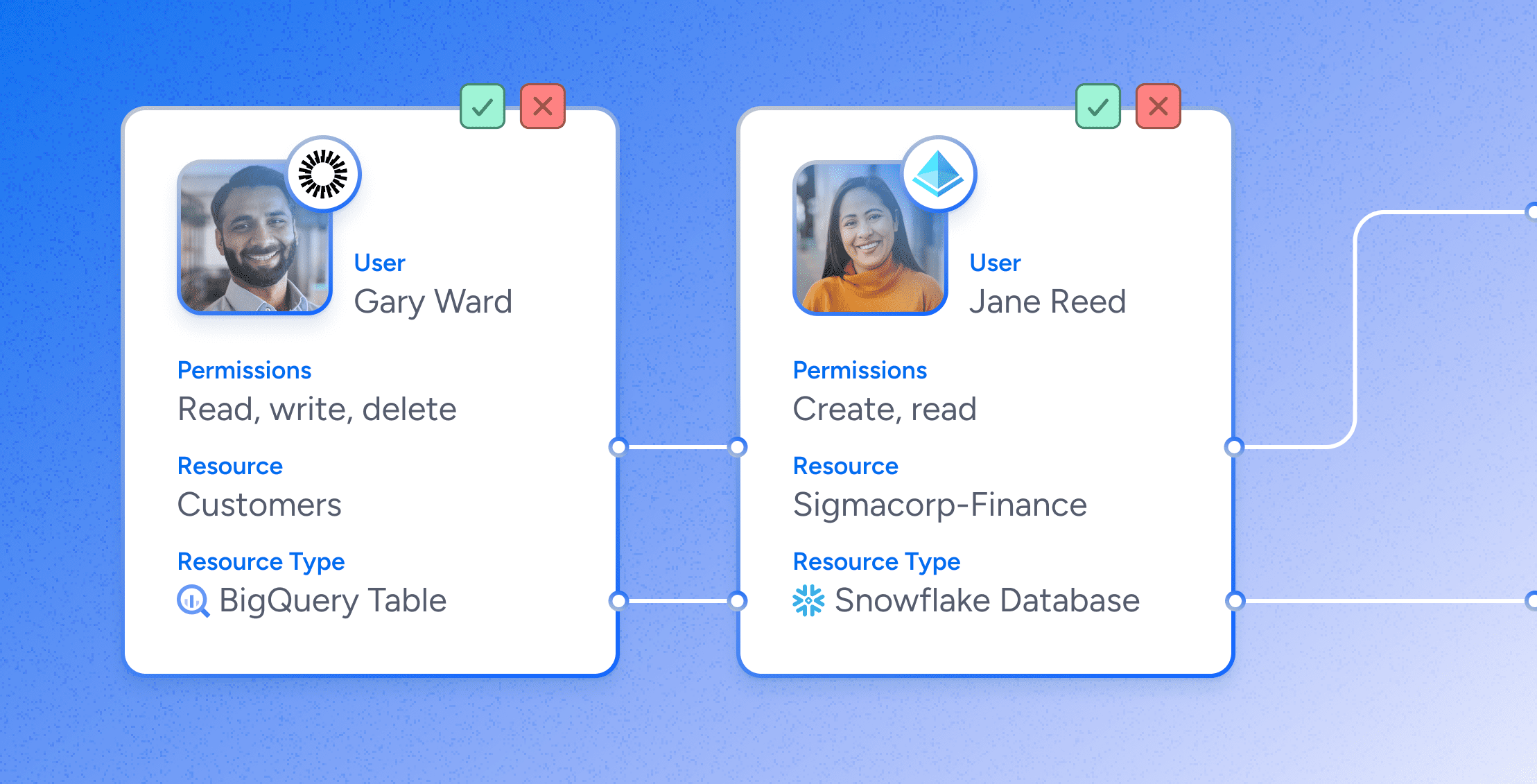
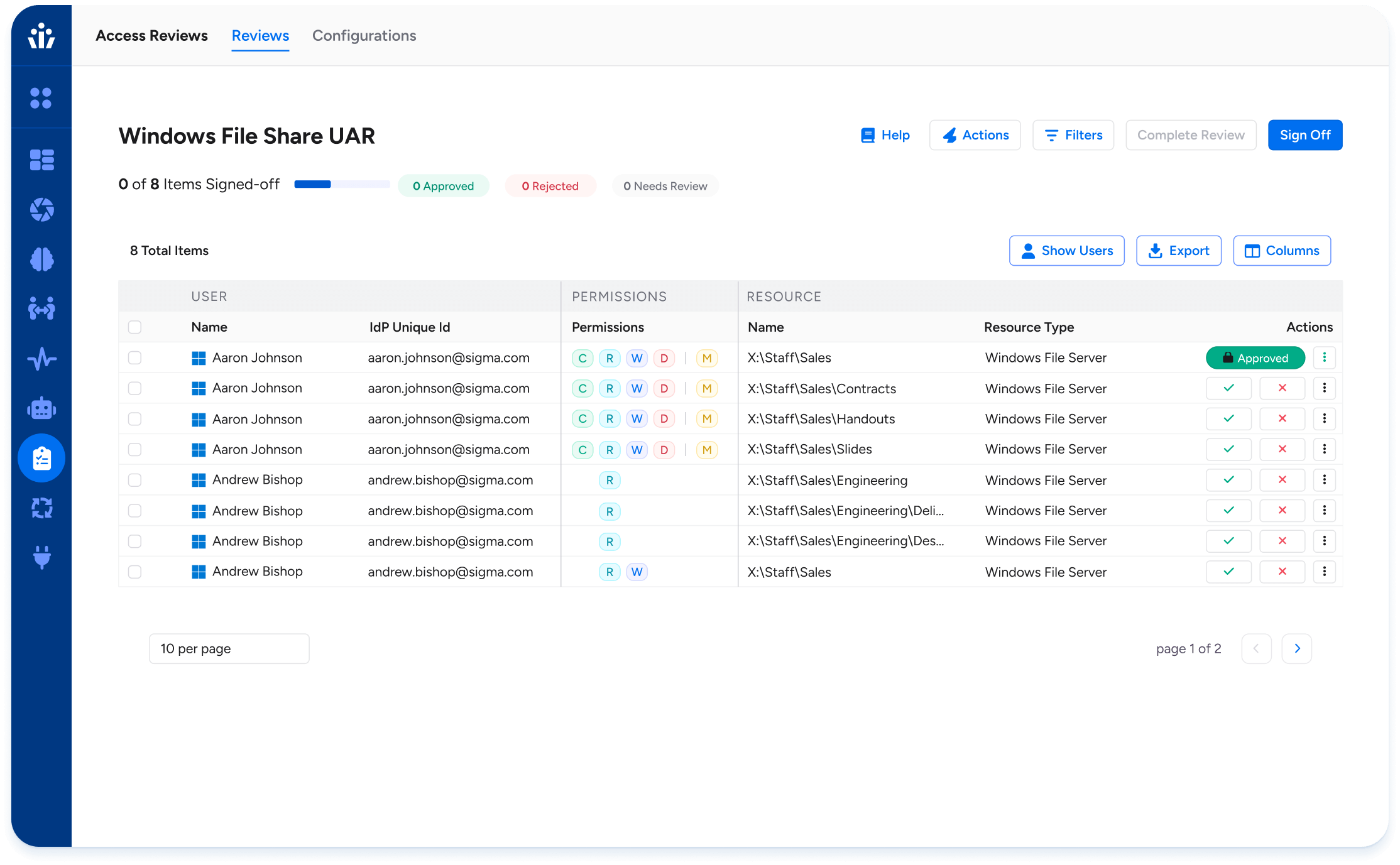
Harness AI-Powered Access Reviews – Focus on high-risk access paths first with risk scoring and provide clear explanations and recommendations to reviewers while surfacing policy violations, access outliers, usage insights and historical certification decisions to execute fast, informed campaigns.
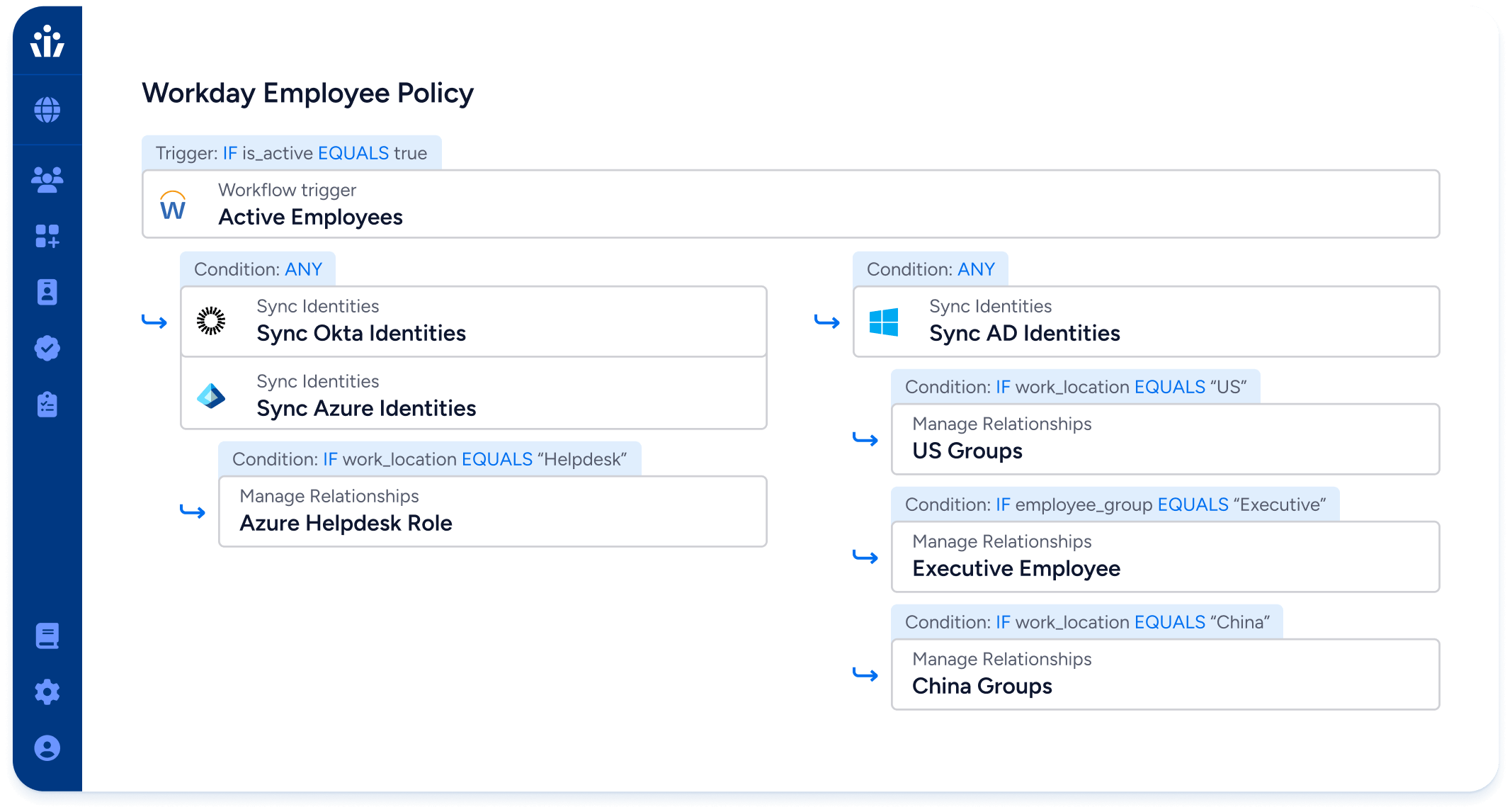
Automate Identity Lifecycle Management – Automatically grant or revoke birthright access when a user joins, changes roles within or leaves the organization – ensuring Day 1 user productivity, improving organizational identity security posture,and eliminating time-consuming and error-prone manual provisioning
Enable Self-Service Just-In-Time Access Requests – Empower users to view, request, and remove their own access without the need for ticket creation or manual application owner intervention. Request time-bound privileged or non-privileged access to reduce the risk of standing privilege
Identify Separation of Duties Violations – Discover and mitigate toxic combinations and separation of duties violations within applications and across platforms.
Integrate Across Your Application Ecosystem – The Veza Access Platform integrates with 325+ applications natively plus native SCIM provisioning capabilities adds support for thousands of SCIM-native applications; OAA/OAA Write Frameworks extend support to custom, homegrown, and legacy applications; includes full CSV-based flat file support


“As a fintech company, our customers rely on us to maintain a strong compliance posture to keep their data secure. Veza helped us implement governance standards within our Snowflake deployment by giving my team visibility to manage all identities and their access to data in Snowflake. Veza empowers my teams with the insights they need to manage and mitigate risks.”
Steven Hadfield | Senior Staff Product Security Engineer

“Our current user management is federated across multiple systems, and that makes it very tricky for us to manage and understand who has access to what. So looking at a system like Veza, it allowed us to really understand that in a very simple and easy way. And honestly, the first time we plugged it in, we knew we needed to get this product.“
Stephen Cihak | Senior Director, Cloud Platform & Site Reliability


“Veza has given our team unprecedented visibility to manage all identities and their access, enforce policies, and mitigate risks. We appreciate Veza’s flexibility in adding new integrations for both common and industry unique applications.”
Brad Lontz | SVP of IT & CIO