Blog
-
 AI
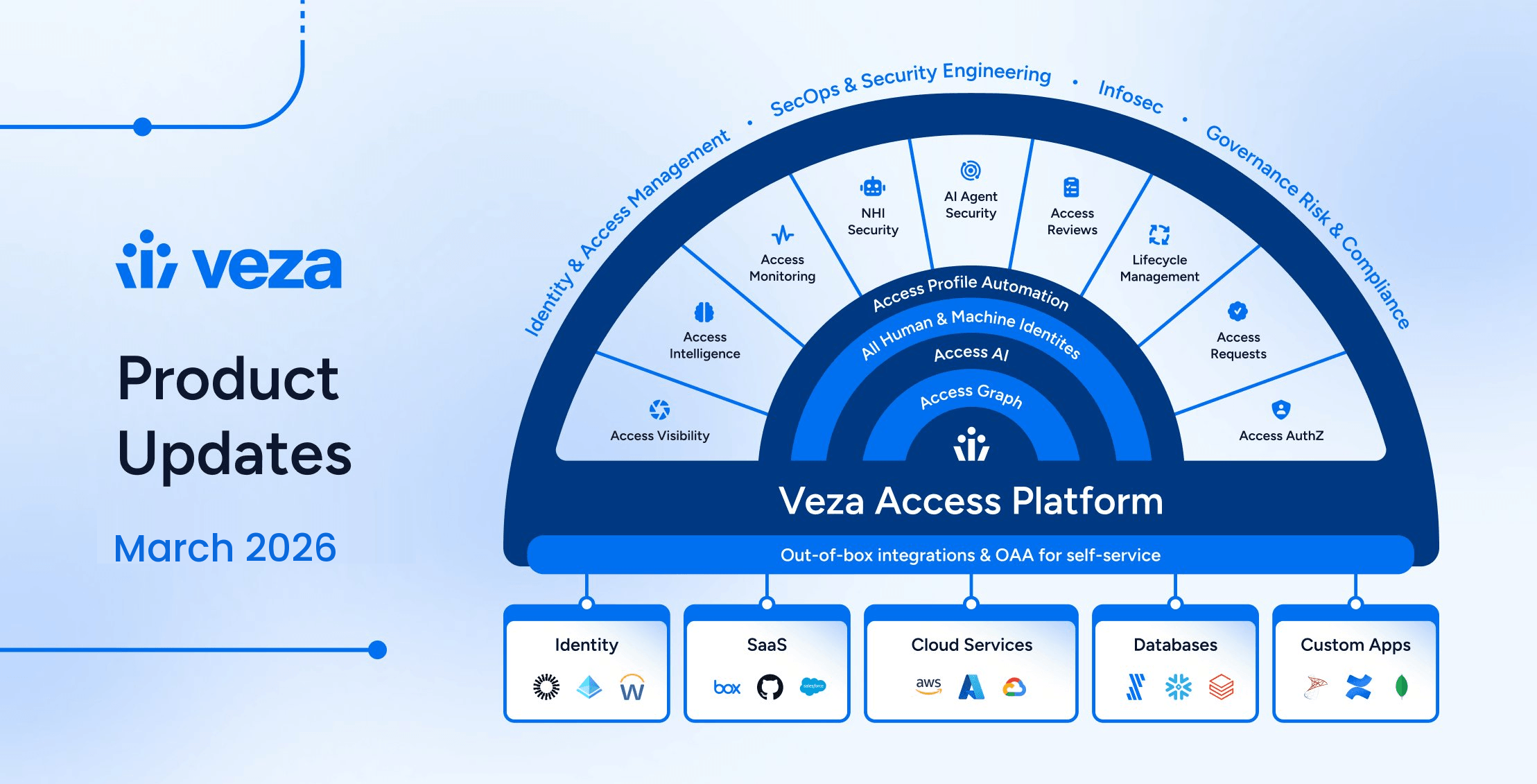
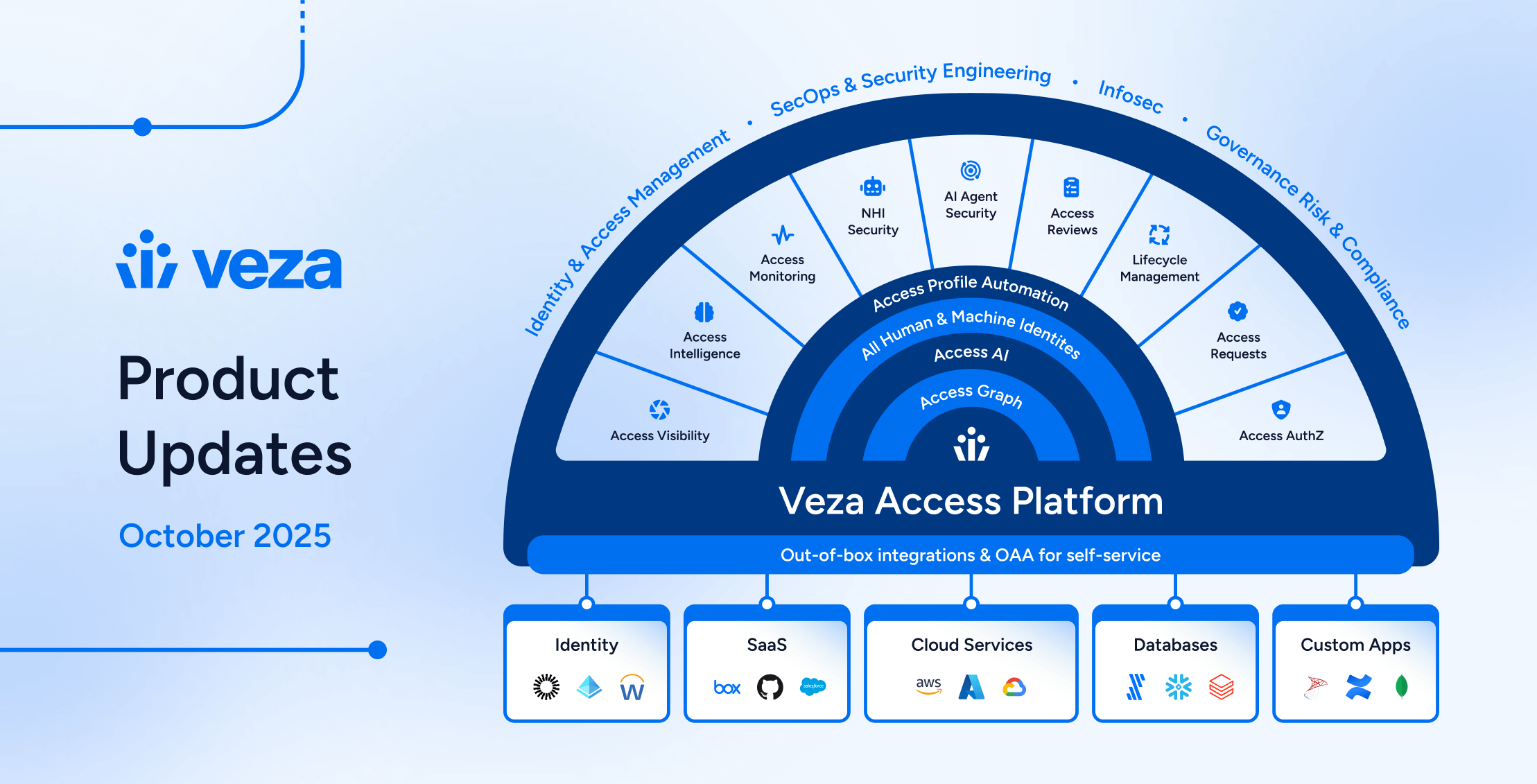
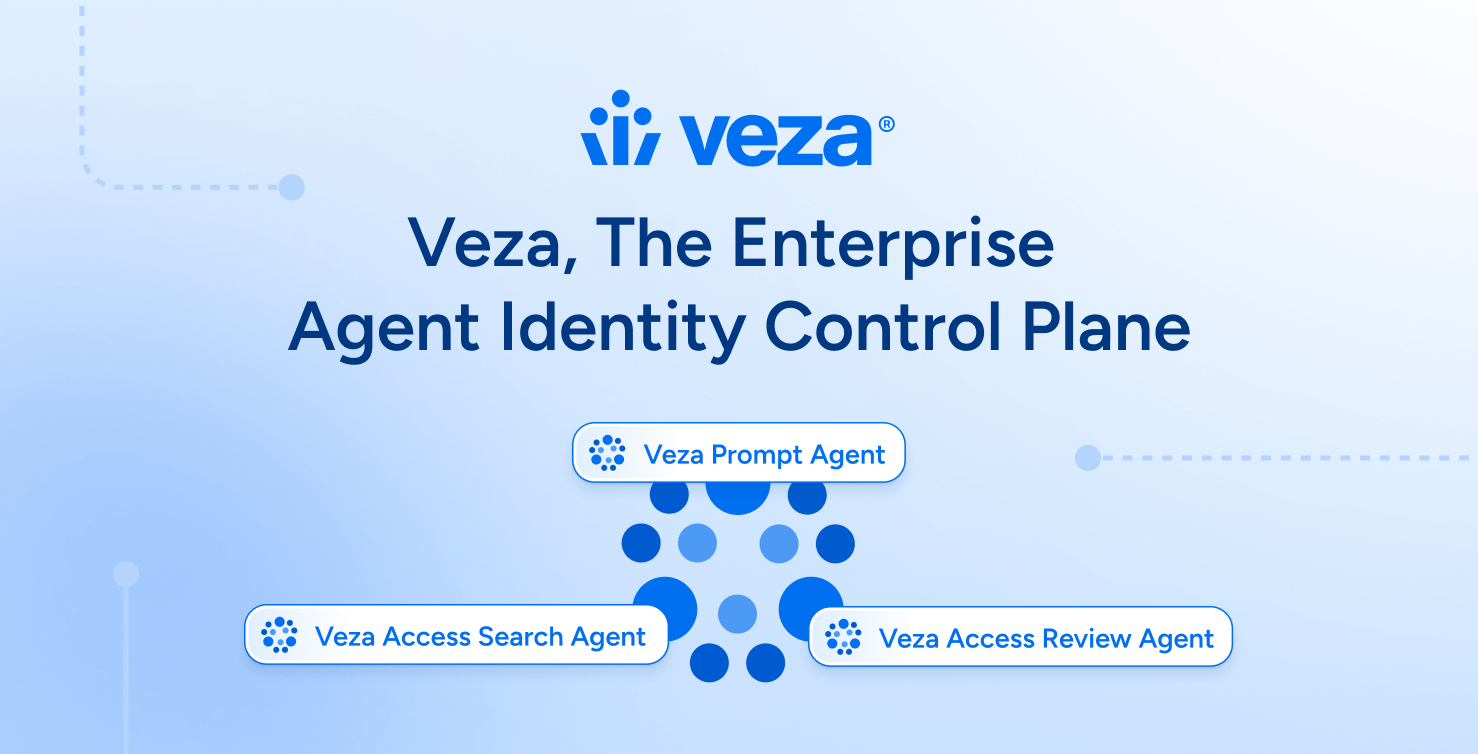
AIVeza – The Enterprise Agent Identity Control Plane
Veza’s 2026 State of Identity and Access Report found that in a typical enterprise, an average worker holds 96,000 entitlements, 38% of IdP accounts are dormant and only 55% of permissions are safe and compliant. The volume and complexity of identity-based attacks is exacerbated by the explosion of AI agents and non-human identities (NHIs). In […] -
 Company
CompanyServiceNow + Veza: A new chapter in identity security
Today marks a pivotal moment—not just for Veza, but for the entire identity security industry. I’m deeply proud to share that ServiceNow has signed a definitive agreement to acquire Veza. Together, we will accelerate the mission to secure identity across the modern enterprise as organizations transition into the era of agentic identities. When Maohua, Rob, […]
Explore our posts
-
Identity is Eating Security: Why Access Is the New Perimeter
Learn more -

When Logging In Is the New Hacking: Nicole Perlroth on the Evolving Cyber Threat Landscape
Learn more -

Simplifying CMMC 2.0 Compliance: Modern Access Control Strategies for Government Contractors
Learn more -
The Evolution of Identity and Security at Workday: Insights from CISO Josh DeFigueiredo
Learn more