Veza and Crowdstrike
Leverage CrowdStrike Falcon Identity Protection’s risk scores and severities in Veza to quickly identify, manage, and restrict access to critical applications, systems and data in the event of an identity-based threat.
Benefits
Determine blast radius from a compromised identity
- Veza instantly helps visualize effective permissions of a compromised human or machine user identified by CrowdStrike Falcon Identity Protection across cloud and on-premise applications (i.e. Snowflake tables, GitHub repositories, CRM applications such as Salesforce).
- Visualize permissions and conduct automated access reviews and certifications to quickly mitigate impact by a compromised user or a machine identity.
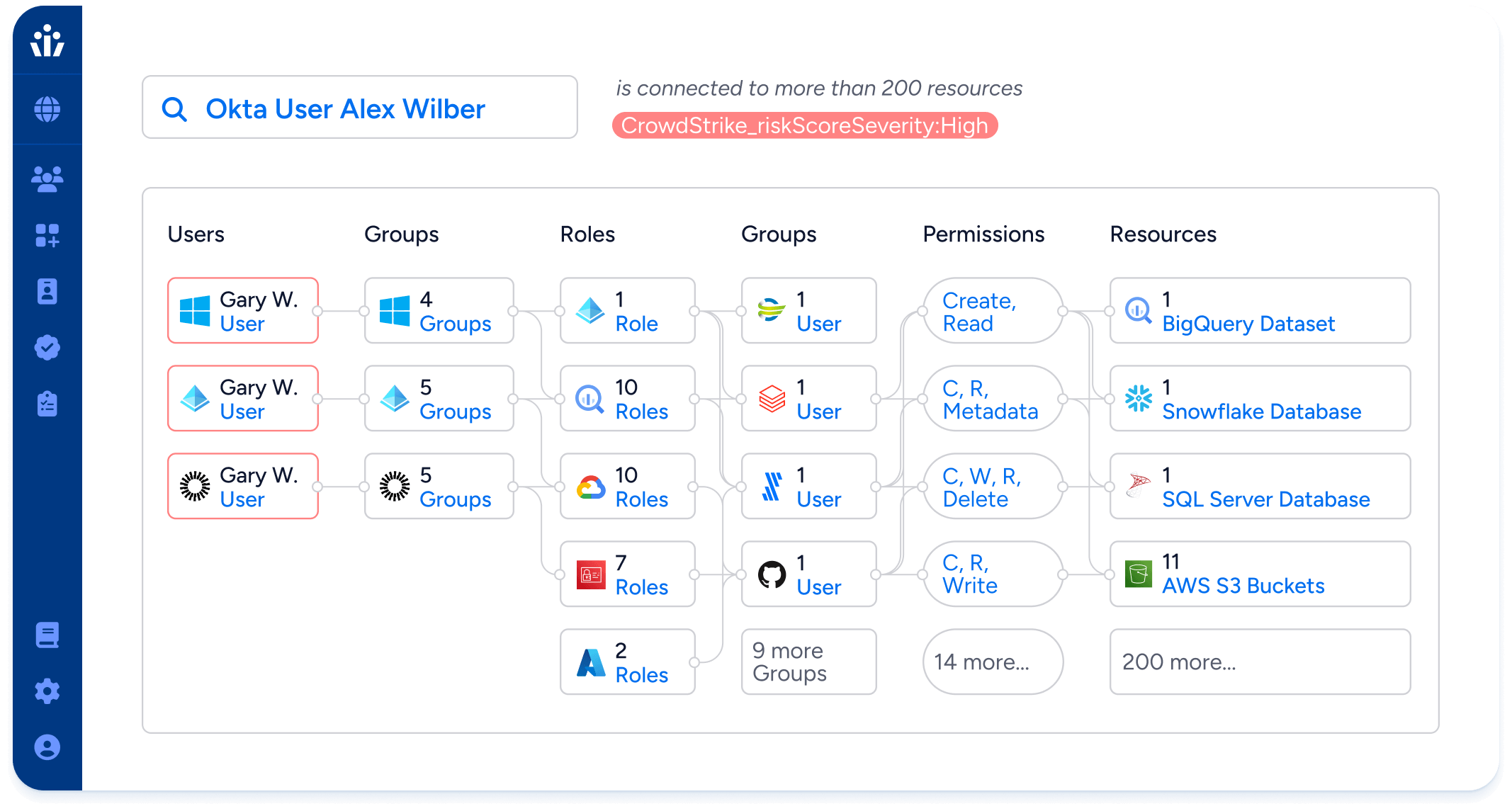

Prioritize threat response based on user access
- Use the Veza Access Graph to prioritize remediation for users with the most access to sensitive data.
- Streamline remediation and minimize the attack surface to prevent breaches of sensitive data.
Conduct micro-certifications and just-in-time access reviews
- Modernize identity access and identity governance processes by immediately reviewing at-risk access from CrowdStrike’s identity-based risk scores.
- Improve security posture and prevent risk exposure without waiting for the next full access review.