Blog
-
 Identity Security
Identity SecurityUnderstanding ISPM: Closing the Identity Gap with Identity Security Posture Management
ISPM is a new category of identity security designed to help organizations continuously monitor and manage identity risk across cloud, SaaS, and hybrid environments. Learn how Identity Security Posture Management works, why it matters, and how Veza enables it. -
 AI
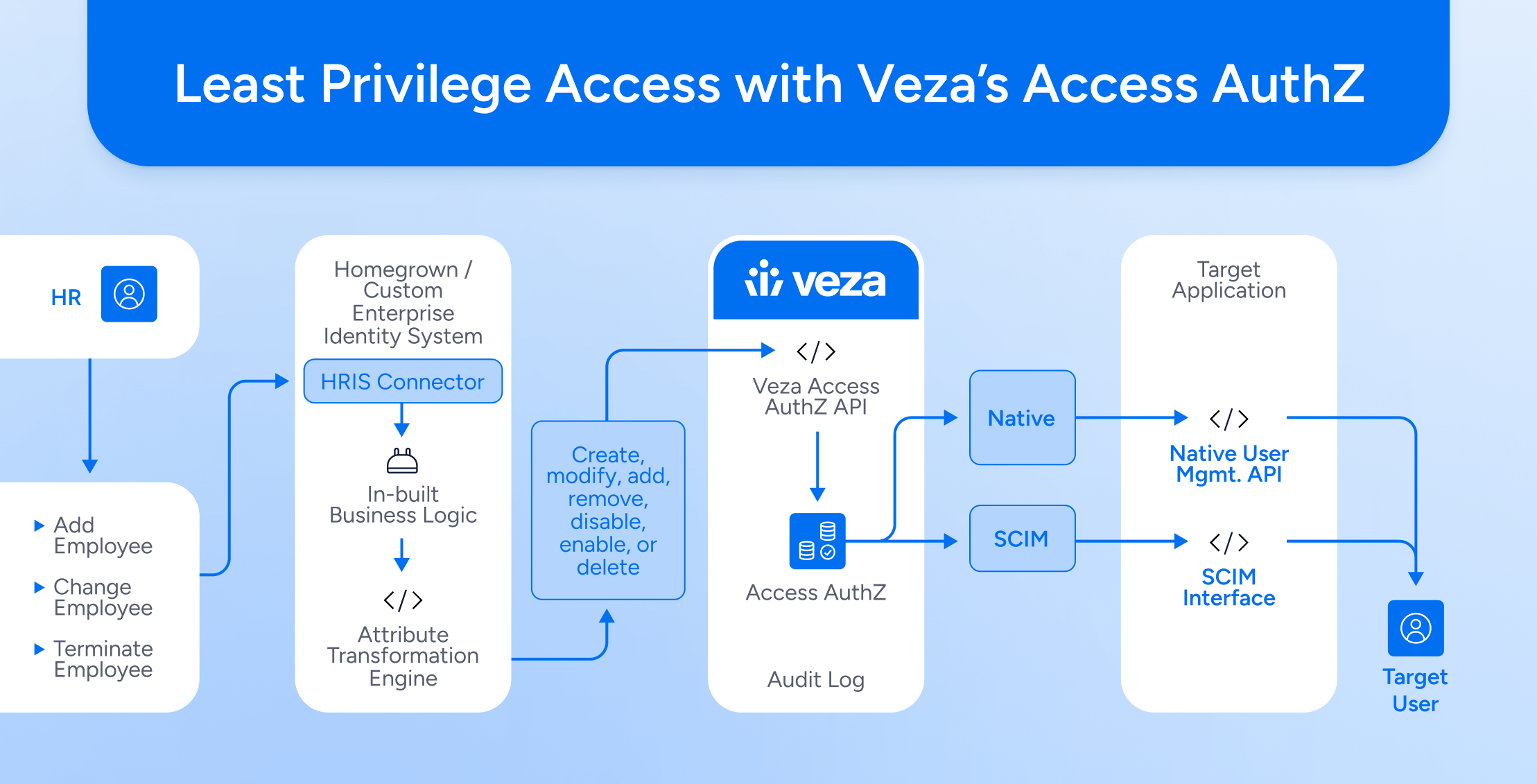
AIVeza Access AI – Applications of Gen AI for Identity Security Use Cases
Veza Access AI transforms identity security by enabling natural language queries to navigate complex access landscapes, empowering organizations to achieve least privilege effectively.
Explore our posts
-
Identity Targeting: A Growing Threat with Rachel Wilson | Ep 1
Learn more -
Welcome to the Identity Radicals Podcast
Learn more -

Join Us at Oktane: Explore “Bad Permissions” and Veza’s Access Solutions
Learn more -

Veza @ Fal.Con 2023
Learn more -
Building Veza’s Platform and Products
Learn more -
Veza Secures Strategic Investment from Capital One Ventures and ServiceNow Ventures to Accelerate Identity Security
Learn more
-

Decoding Identity Security for AI Security Posture Management (AISPM)
Learn more -
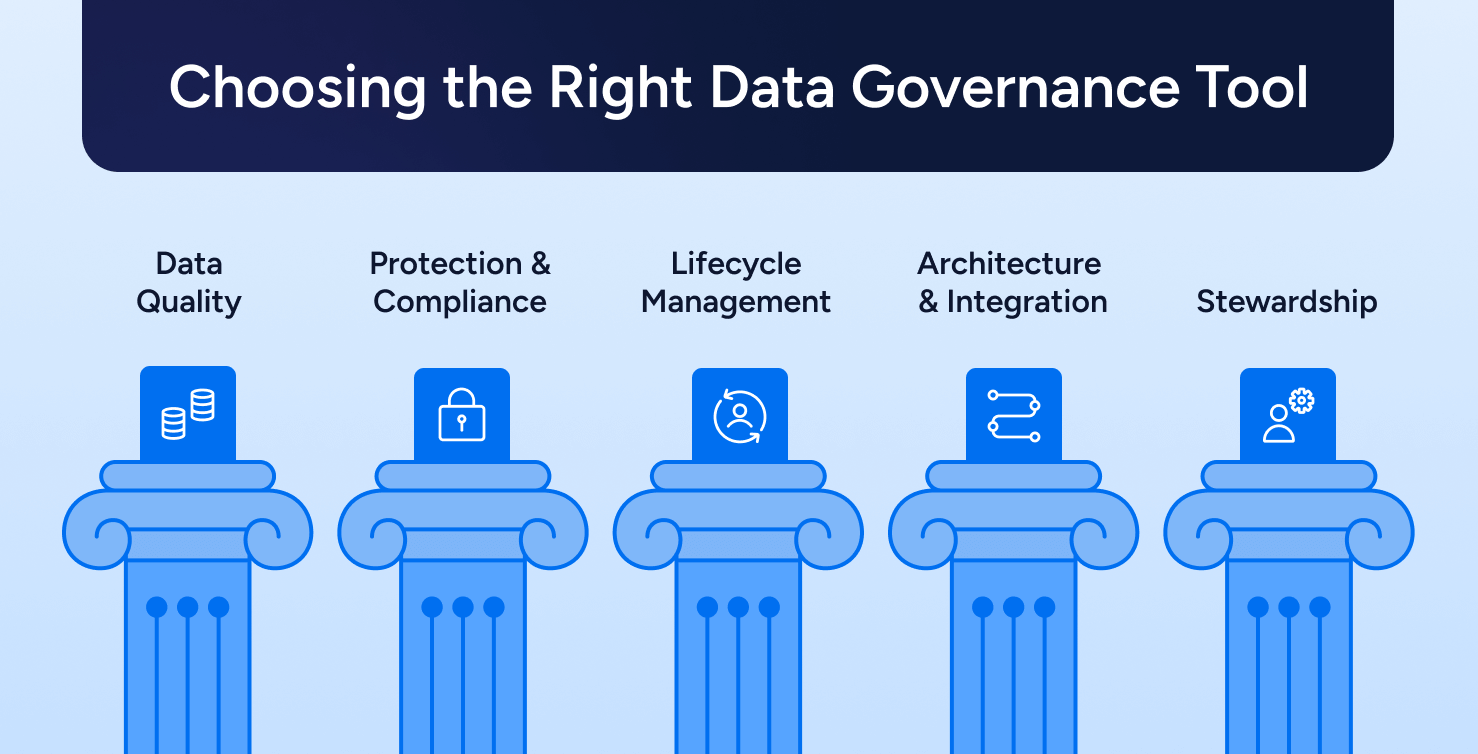
How To Choose the Right Data Governance Tools [2025]
Learn more -
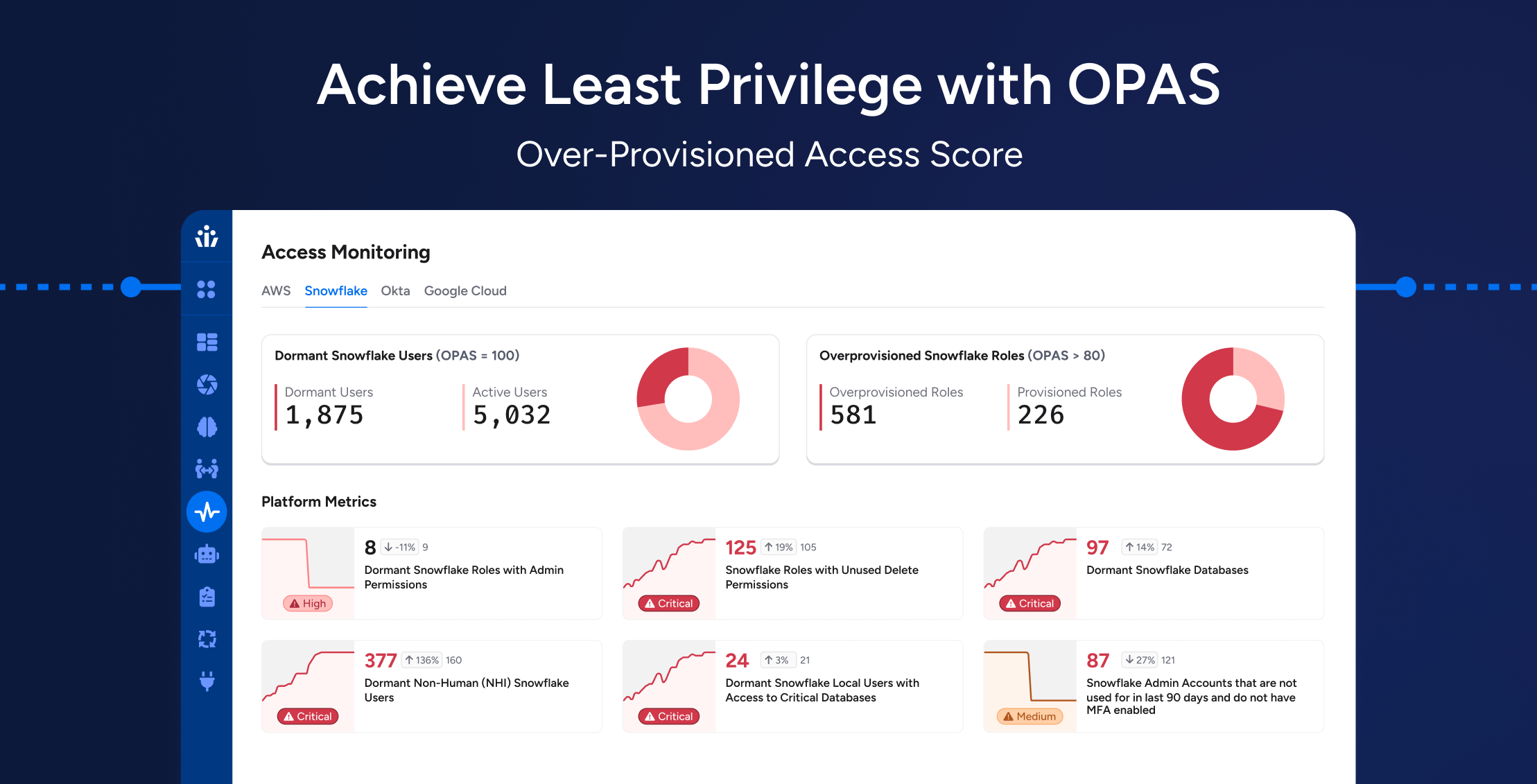
Achieving Least Privilege at Scale: How OPAS Helps Enterprises Reduce Hidden Access Risks
Learn more -
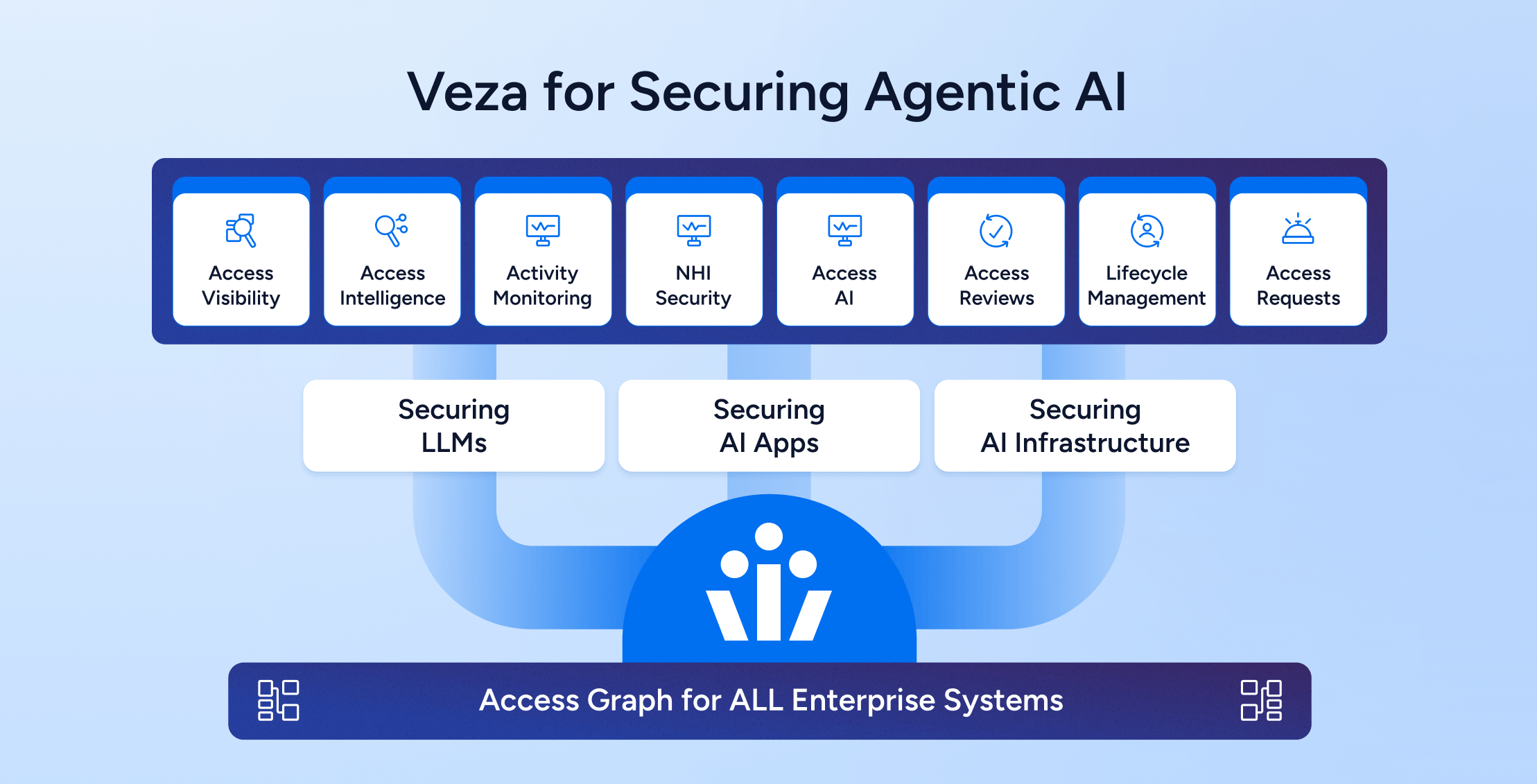
Trust as the Foundation for Agentic AI Architecture: Securing Access to all the AI layers – Models, Infra, AI Applications
Learn more
-
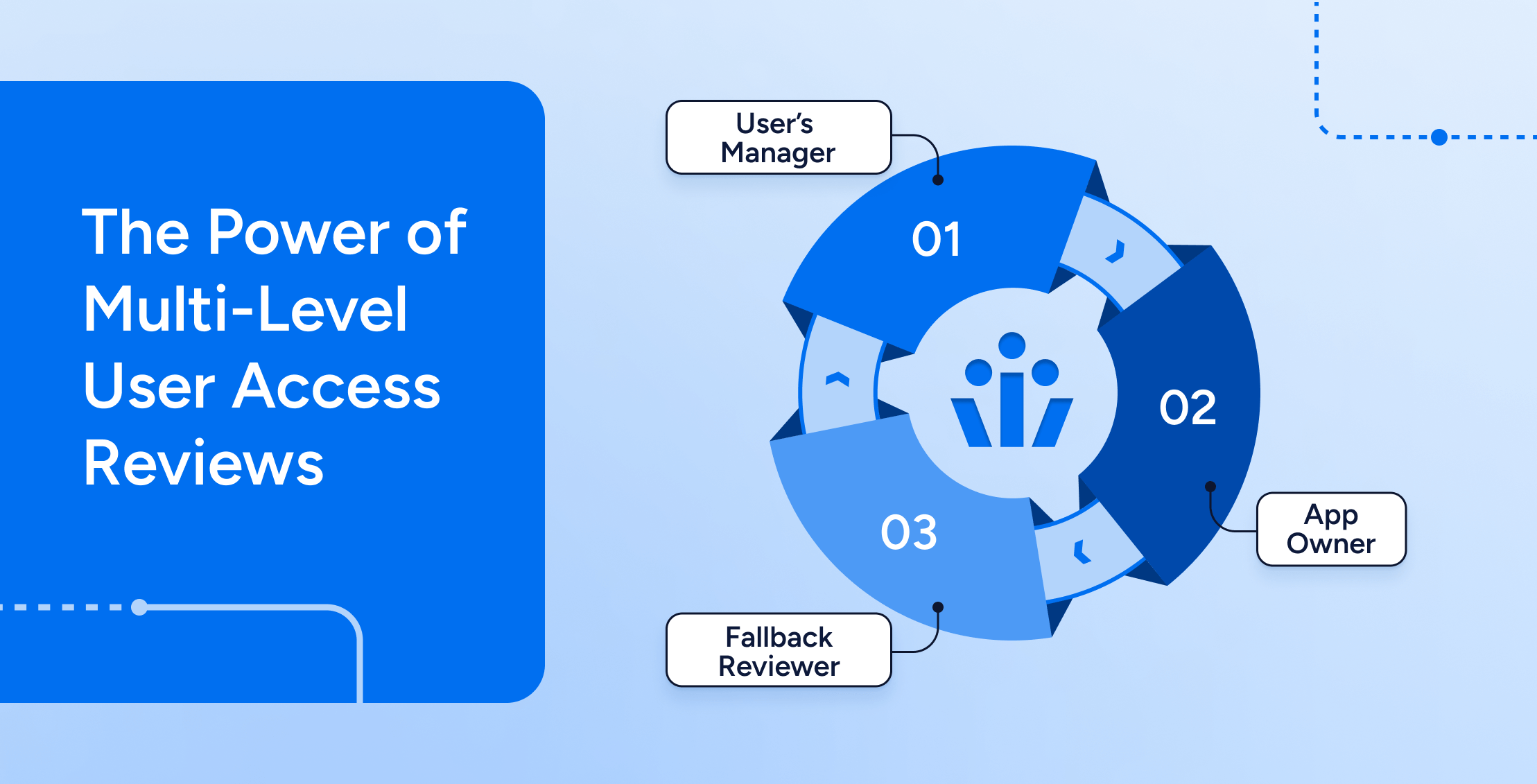
The Power of Multi-Level User Access Reviews
Learn more -
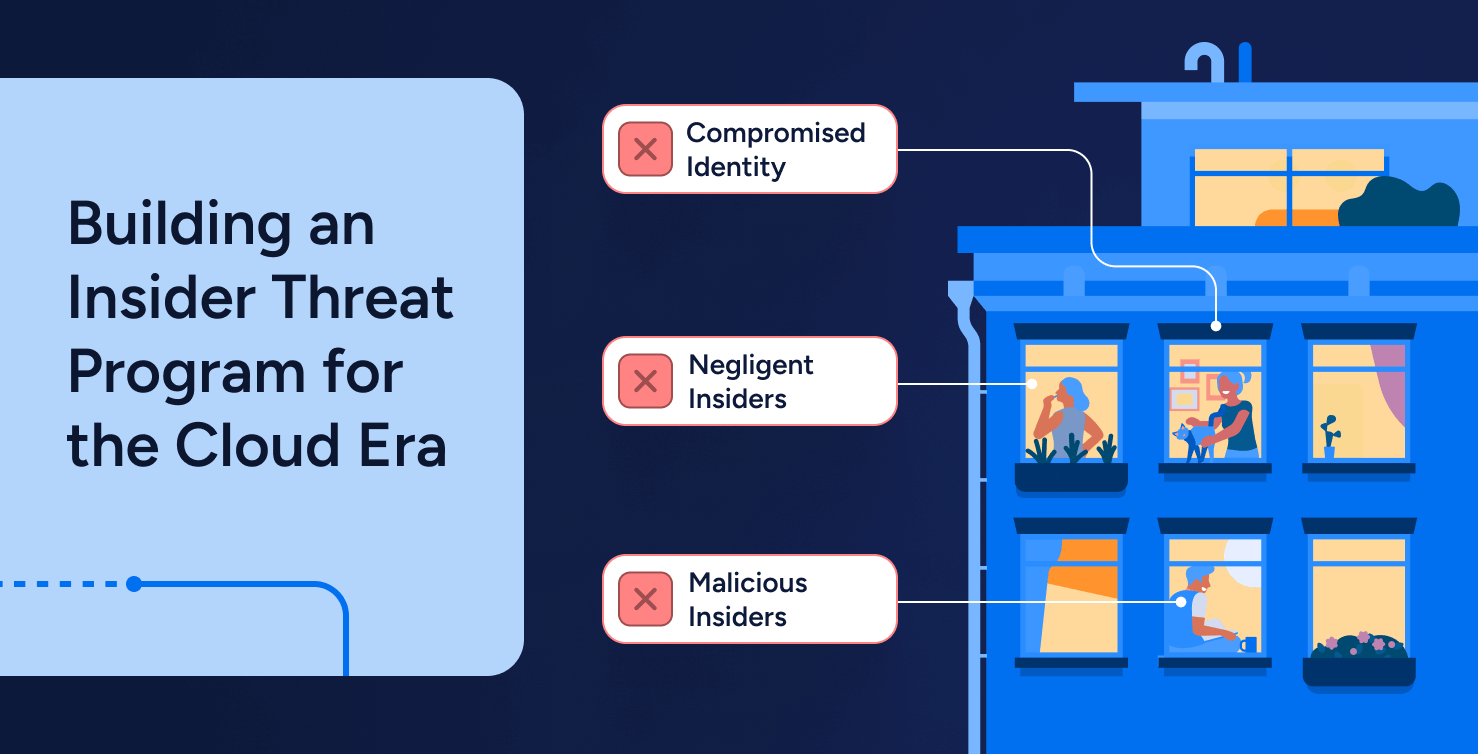
When Identities Turn Against You: Building an Insider Threat Program for the Cloud Era
Learn more -
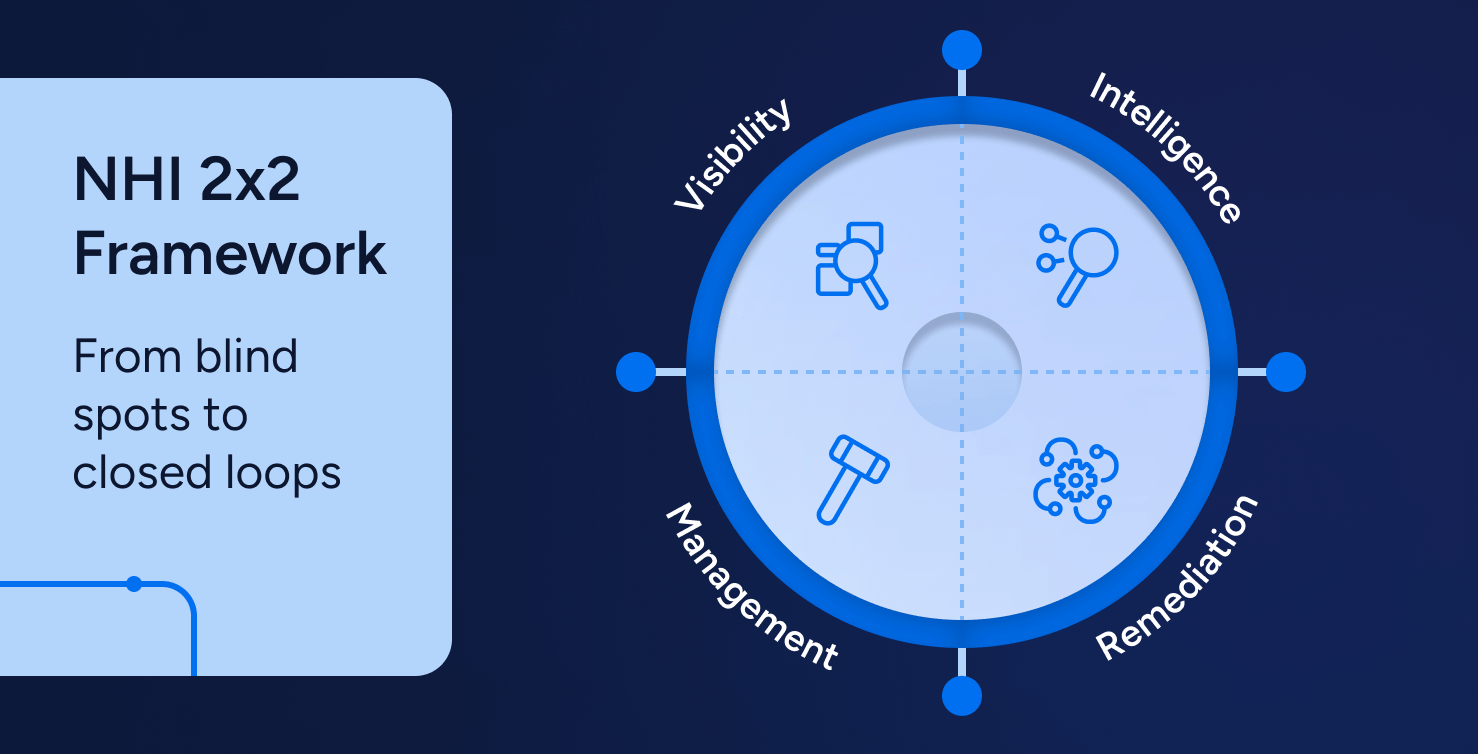
NHI 2×2 Framework: From Blind Spots to Closed Loops
Learn more -
All the Keys, Visualized: Governing 90+ Non-Human Identities
Learn more -
NHI Ownership: Solving the “Who Owns This Bot?” Problem
Learn more
-

When Logging In Is the New Hacking: Nicole Perlroth on the Evolving Cyber Threat Landscape
Learn more -

Simplifying CMMC 2.0 Compliance: Modern Access Control Strategies for Government Contractors
Learn more -

Achieving DORA Compliance: A Practical Guide for Financial Organizations
Learn more -
The Evolution of Identity and Security at Workday: Insights from CISO Josh DeFigueiredo
Learn more
-
I Attended the Verizon Data Breach Session at RSA So You Don’t Have To:
Learn more -
Reflections from Gartner IAM London: Visibility Leads to Observability
Learn more -

Achieving DORA Compliance: A Practical Guide for Financial Organizations
Learn more -

Join us at Black Hat USA August 3 – 8, 2024
Learn more -

Join us at RSAC May 6-9, 2024
Learn more -

Veza @ AWS re:Invent
Learn more
-

Decoding Identity Security for AI Security Posture Management (AISPM)
Learn more -
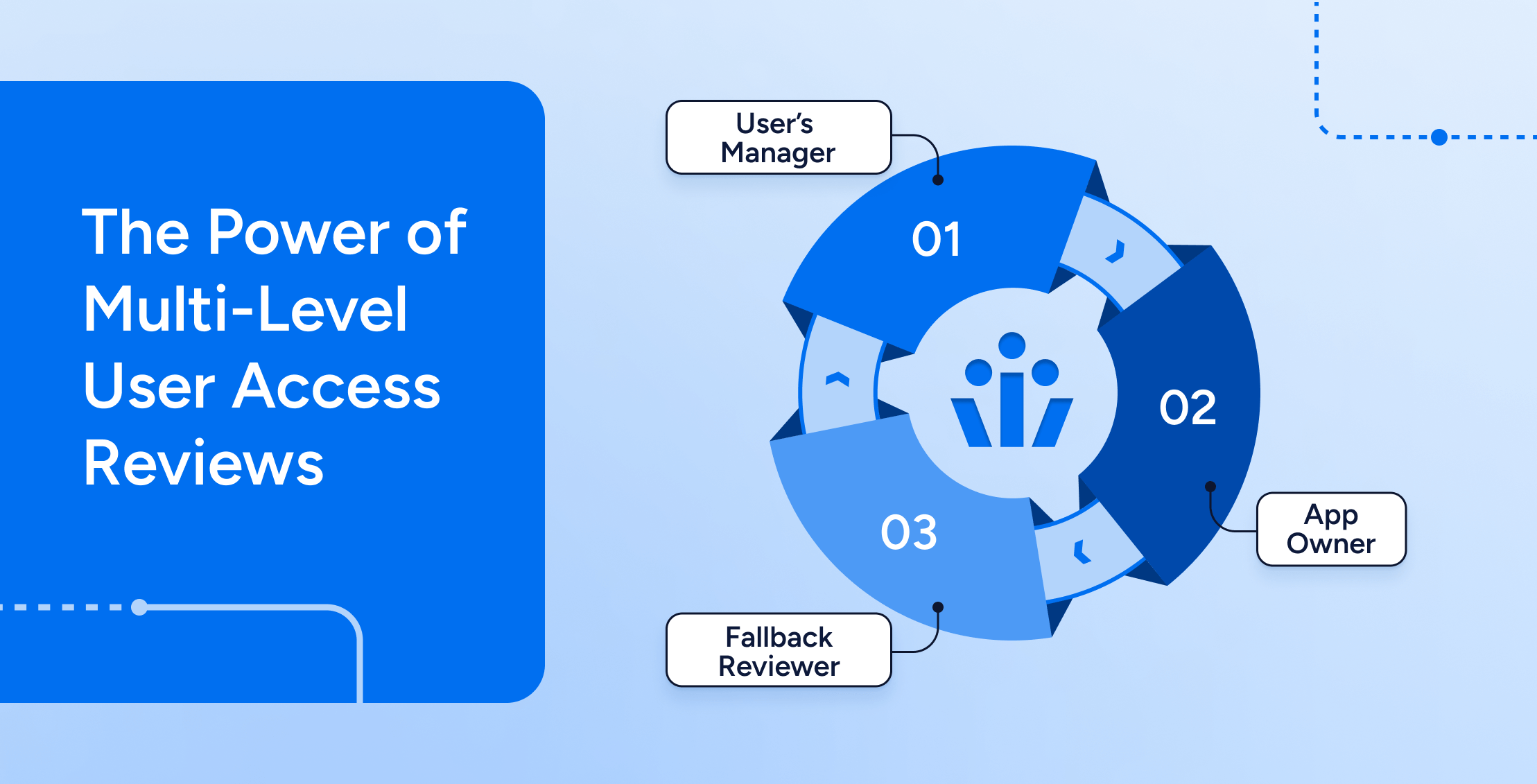
The Power of Multi-Level User Access Reviews
Learn more -
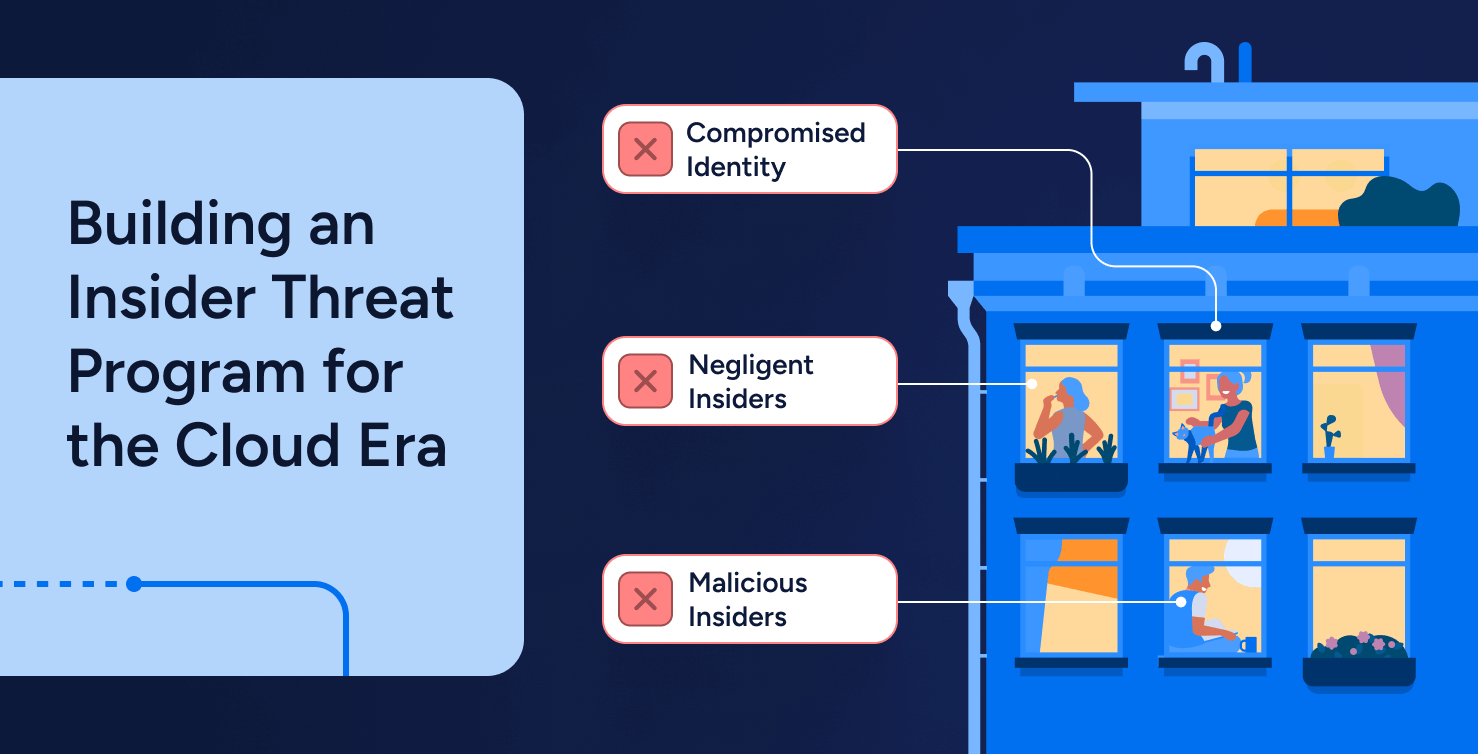
When Identities Turn Against You: Building an Insider Threat Program for the Cloud Era
Learn more -
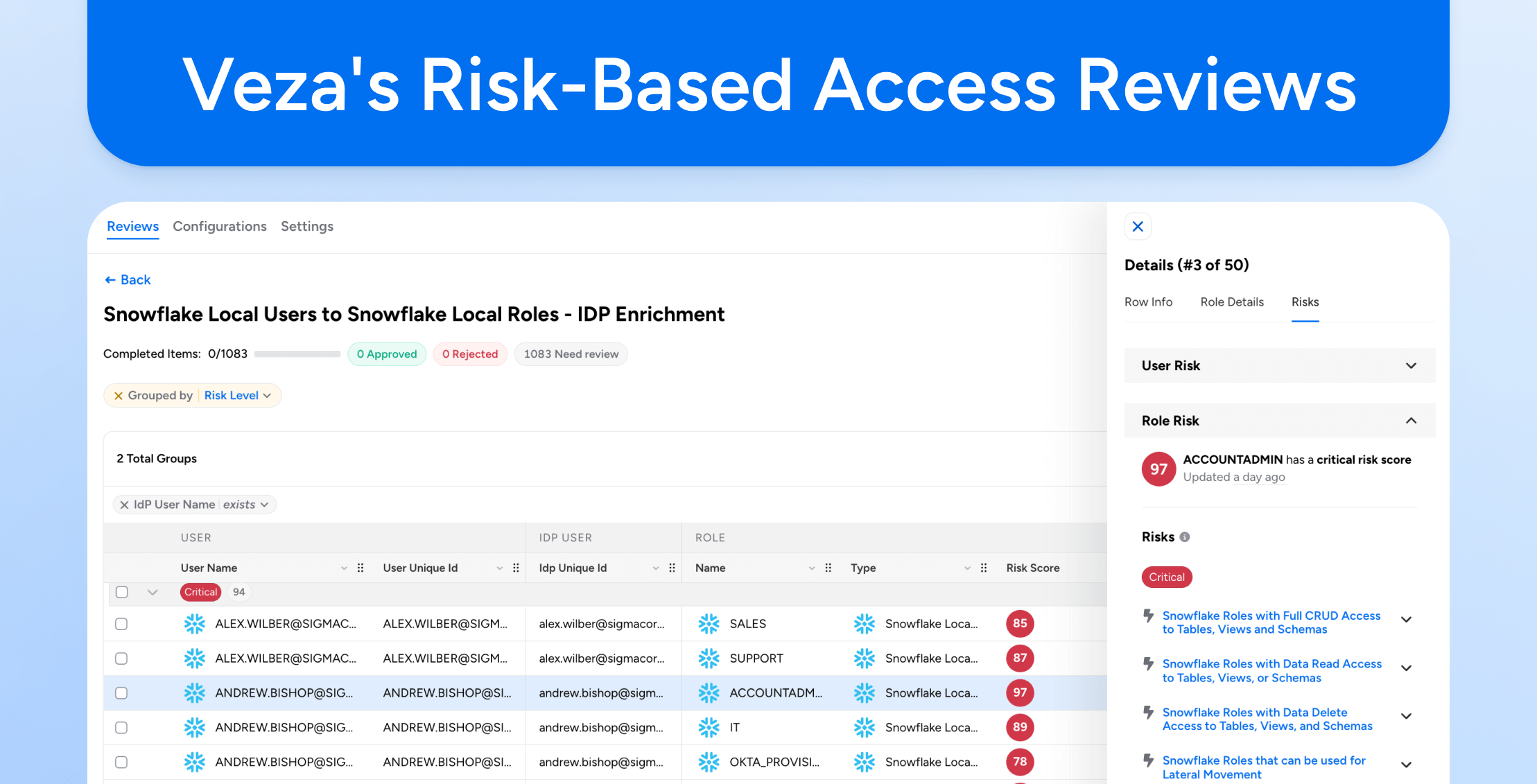
Veza’s Risk-Based Access Reviews and Recertifications
Learn more -
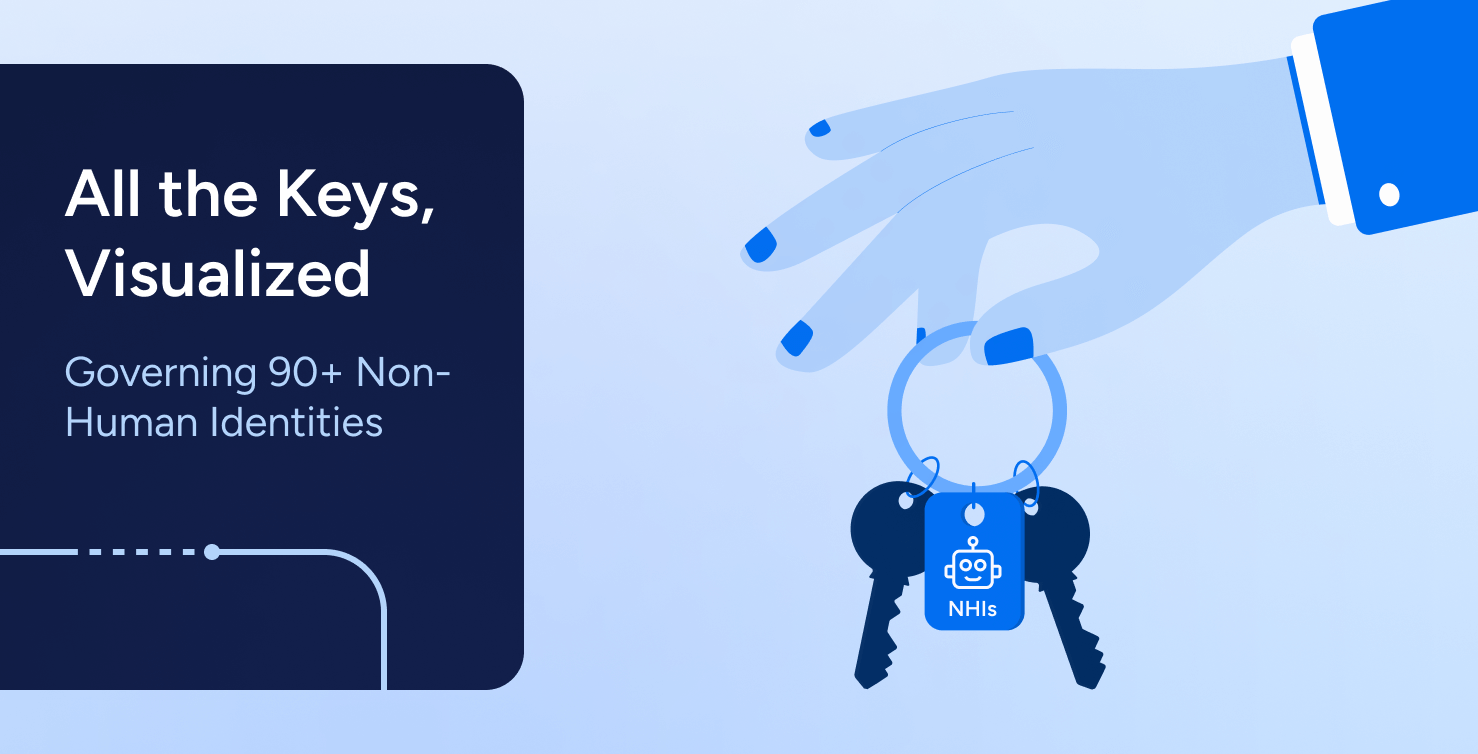
All the Keys, Visualized: Governing 90+ Non-Human Identities
Learn more