The rules of cybersecurity just changed.
Anthropic recently unveiled Project Glasswing, deploying a specialized model called Claude Mythos to find software vulnerabilities at a scale and speed previously unimaginable. The results are a genuine breakthrough: it found a 27-year-old vulnerability in OpenBSD and a 16-year-old flaw in FFmpeg—bugs that had remained hidden despite millions of scans by traditional automated tools.
This discovery speed is a monumental win for Cyber Resilience. But it raises a critical question that vulnerability discovery alone cannot answer much more immediate questions: What is the agent blast radius? Agent Least Privilege Posture? Agent to Agent access authorization? Agent Identity? Human to AI App to Prompt to LLM to NHI Account (Service Account) to Data? And many many more unanswered questions.
Defense-in-Depth: Controlling the Agent Blast Radius for the AI Era
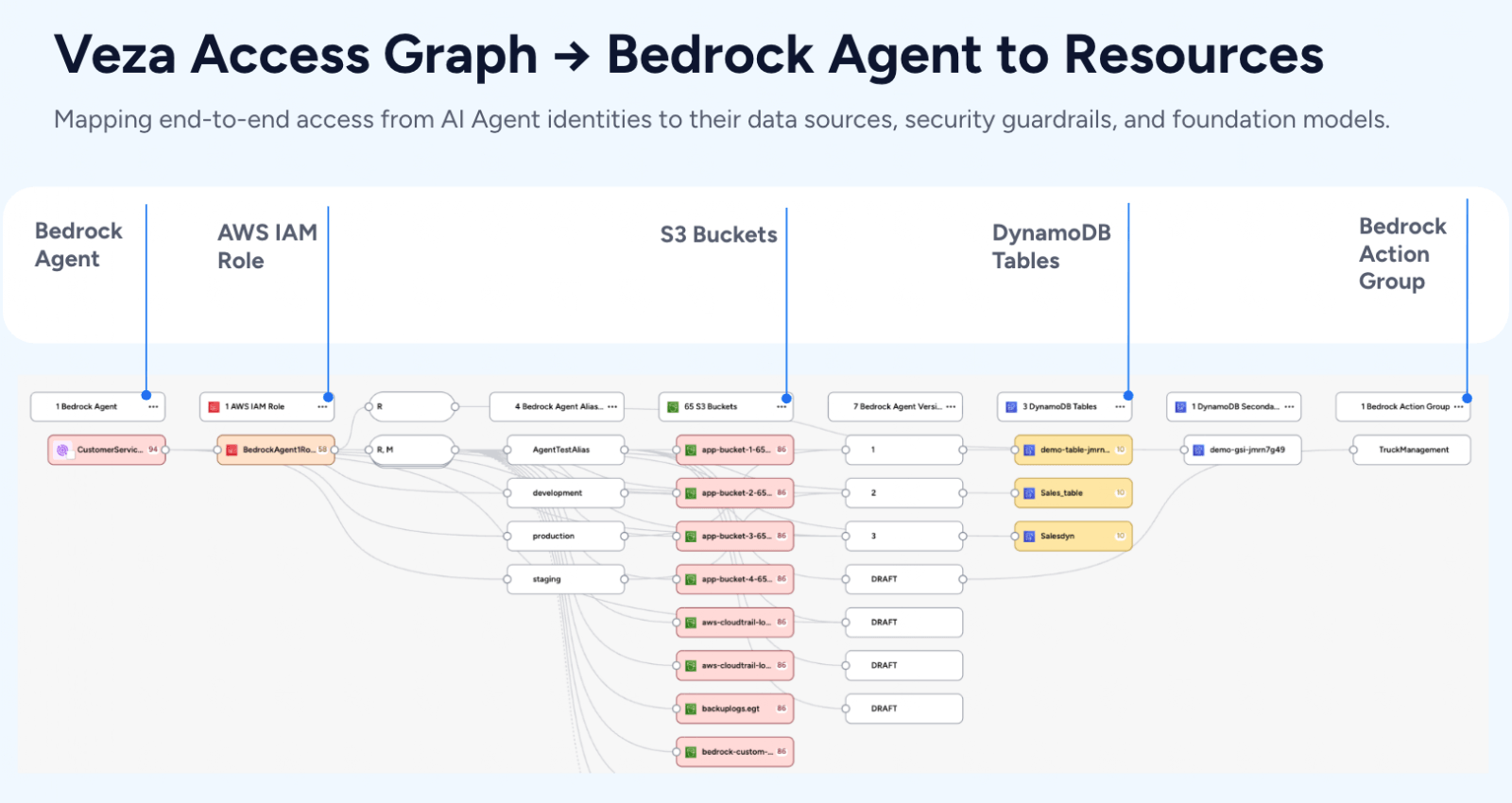
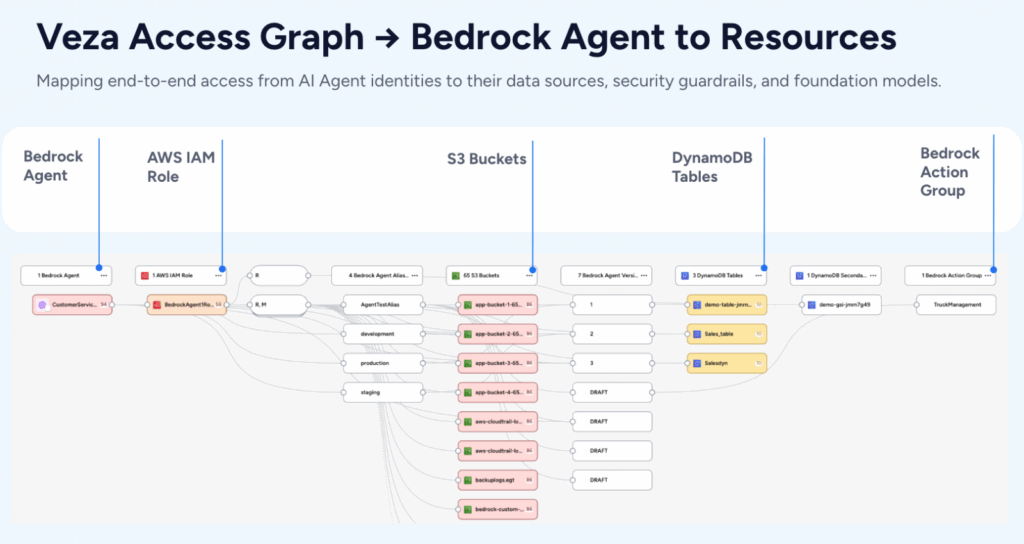
Claude Mythos may be the most capable frontier model yet, but it won’t be the last. Models and agents access data, make decisions, and thus create risks – i.e. agent authorization to access data, agent identity meets the least privilege principles, agent to agent interactions, human authorization to agent, human authorization to agent A to agent B to data, etc. Hardening the application codebase layer is a massive leap forward, but in a true Defense-in-Depth architecture, you must secure the layer that governs every action: Identity is that layer. This is especially critical as Claude Mythos and other frontier models are deployed via AWS Bedrock, Microsoft Azure AI Foundry, and Google Cloud (GCP) Vertex AI.
These platforms are driving a surge in autonomous AI agents that hold real, delegated permissions to write code, invoke APIs, and manage production infrastructure. For example, Anthropic is increasingly becoming an “Agent Operating System (OS),” providing an infrastructure layer that manages the full lifecycle of autonomous agents – from sandboxed execution environments to long-running sessions and coordinated tool orchestration. As agents become more persistent and capable, the challenge shifts beyond execution to governance: managing agent identities, controlling their permissions across enterprise resources, and defining how they interact not only with enterprise resources but also with other agents and human users. In this rapidly evolving agentic landscape, organizations must treat “what can do what on resources” and “who can do what on whom” as equally critical questions, ensuring access control to both resources and agents are tightly defined to support security, accountability, and traceability.
If an agent has excessive permissions on resources or other agents, the Blast Radius of a single error or compromised session is effectively unlimited. Hardening the code fixes the “entry point,” but only the Agent Access Control Permissions allows you to contextualize the reach and provides the controls to remediate access before a path leads to your most sensitive data.
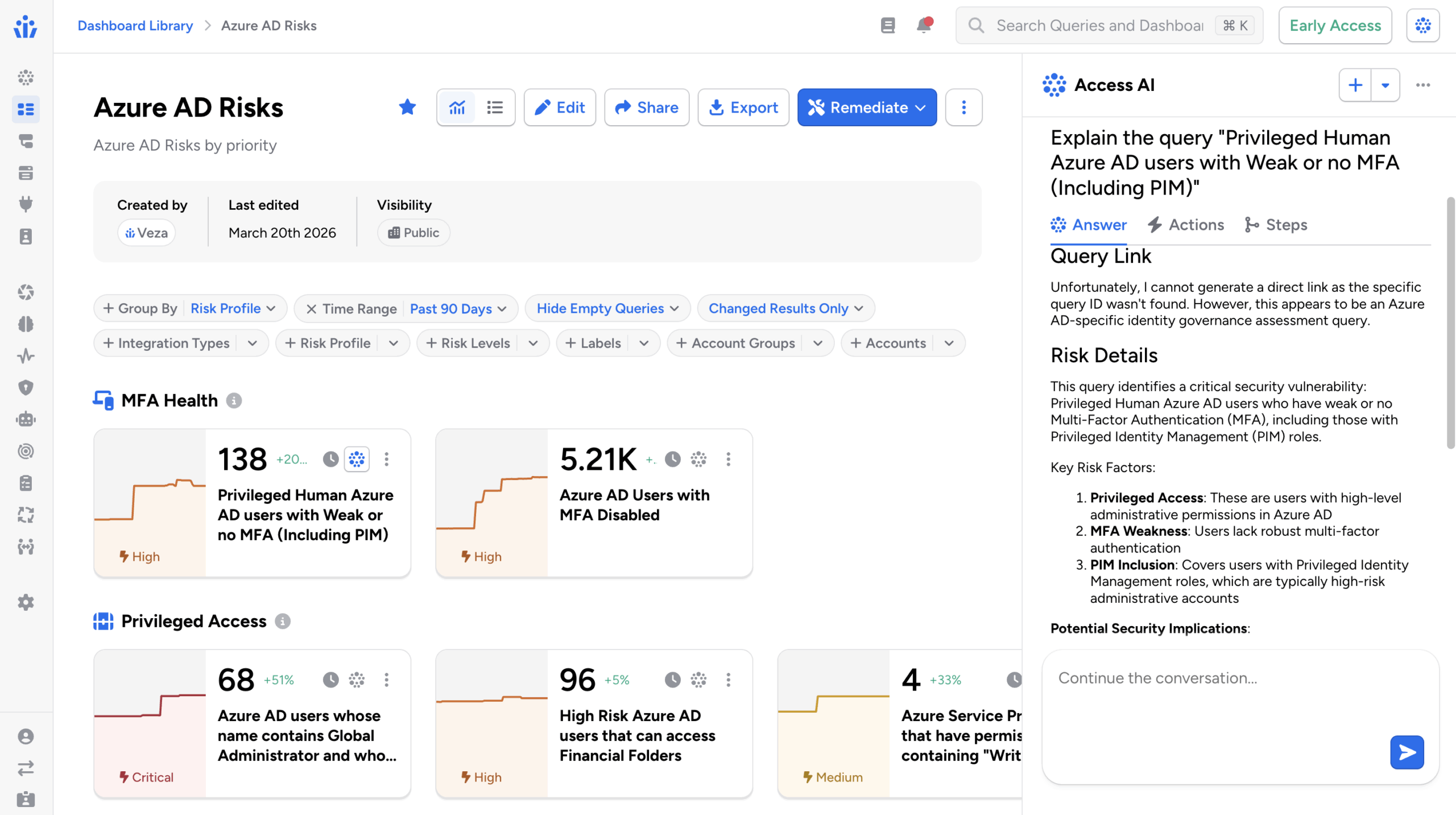
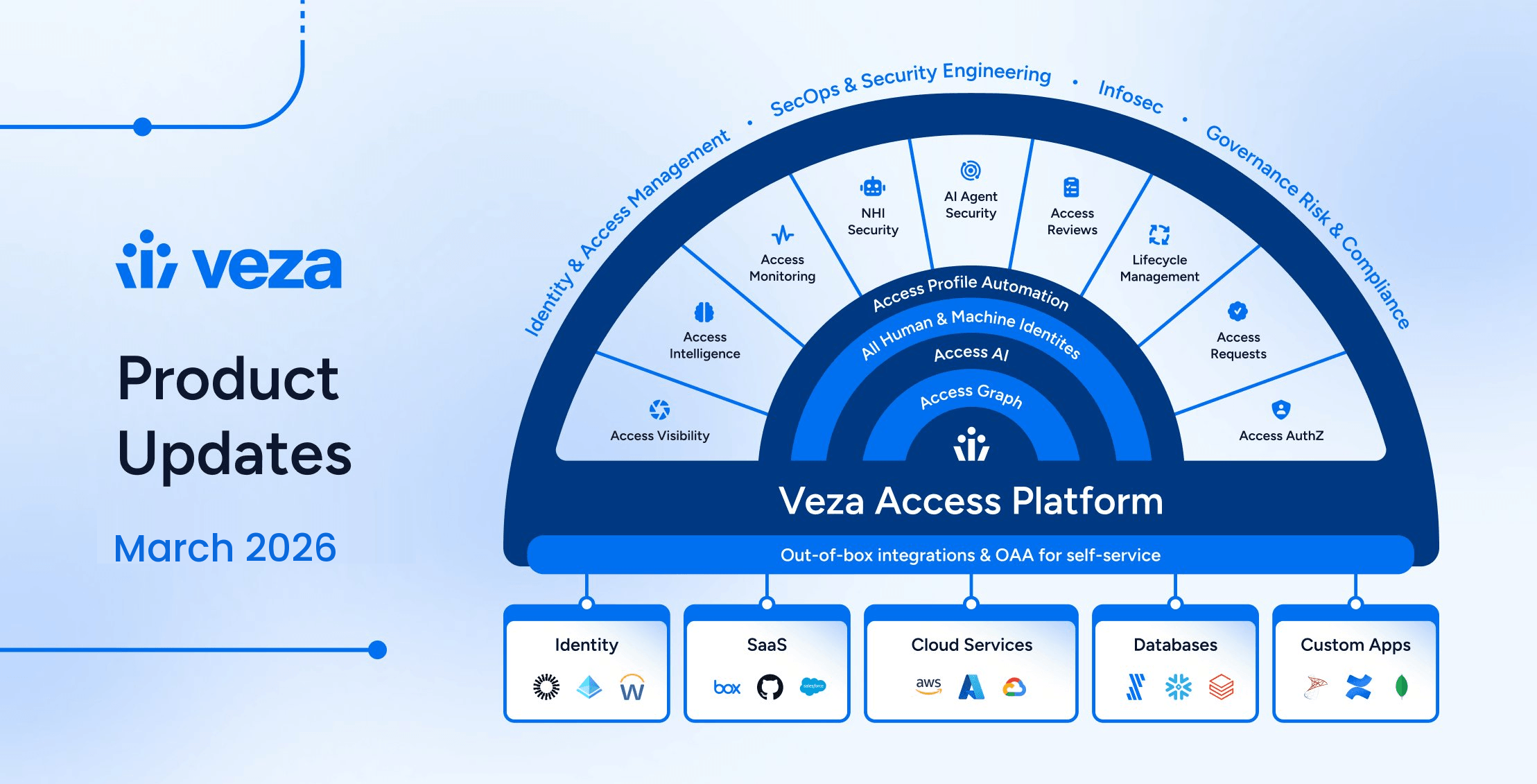
Veza Access Graph Architecture was purpose built and designed for AI Era
At Veza, we believe that in the Agentic Era, an AI agent must be governed as a first-class agent identity. Whether it was built in AWS Bedrock, Azure AI Foundry, GCP Vertex AI, Microsoft Copilot Studio, OpenAI or Salesforce Agentforce, Veza treats it as an identity in the Access Graph, our canonical data model designed for ALL identity types for ALL permission models for ALL systems.
The Access Graph doesn’t just show you “what role” an agent has. It provides the Effective Access: the actual, effective permissions that an agent holds across every resource it can touch.
- The Glasswing View: Hardens the software so there are no “cracks” to slip through.
- The Veza View: Hardens the identity so that even if an agent is compromised—or goes rogue—its reach is strictly limited to what is necessary.
The Two Pillars of Defensive AI
To survive the AI-driven threat landscape, security organizations need a strategy built on two simultaneous pillars:
- Hardened Code: Using Project Glasswing to find and fix holes in software before they can be exploited.
- Least Privilege Agent Identities: Using the Veza Access Graph to ensure the AI agents operating on top of that software aren’t themselves an unchecked attack surface.
The future of enterprise security is built on two pillars: hardened code and least privilege agent identities. We are proud to build alongside the ecosystem that Project Glasswing represents, providing the map of access that ensures the AI revolution remains secure.
The era of the Agent Access Permissions Graph is here.