The first statistic from Accenture’s State of Cybersecurity Resilience 2025 report that strikes me is this: only 10% of organizations have reached what they call the “Reinvention-Ready Zone“—possessing both the strategy and capabilities to defend against modern AI-driven threats. As someone who’s spent two decades securing identities across very large enterprises, this finding doesn’t surprise me. What does surprise me is how many organizations still treat identity as a compliance checkbox rather than the cornerstone of AI security.
The report’s stark assessment—90% of companies lack the maturity to counter AI-enabled threats—will hopefully drive action. But buried within the data is an even more critical insight: the path from “Exposed” to “Reinvention-Ready” runs directly through modern identity security.
The AI-Identity Convergence
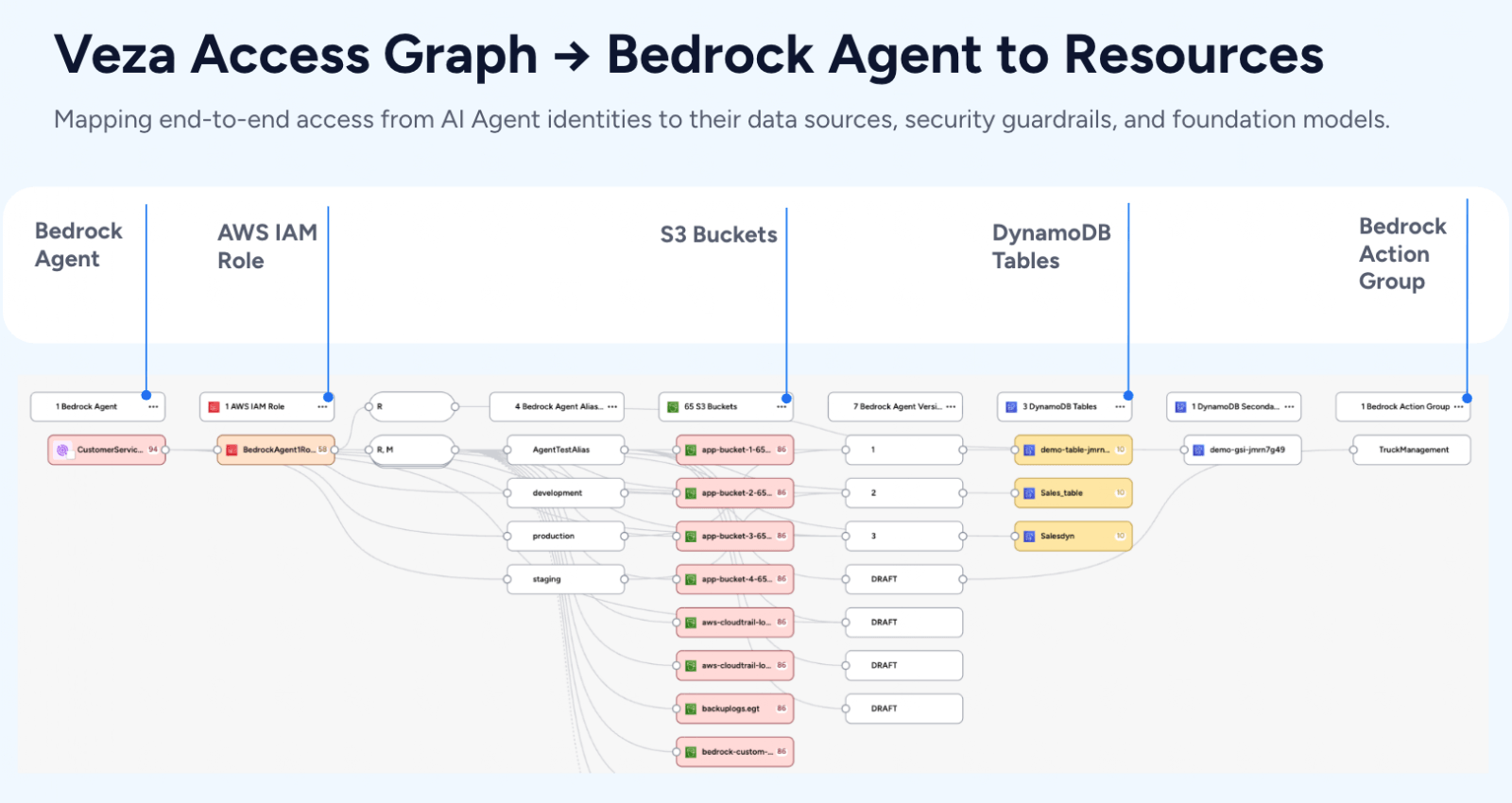
As Accenture rightly points out, AI is moving faster than security. But here’s what I’ve observed: AI isn’t just outpacing security—it’s fundamentally reshaping what identity means. When AI agents can access 50,000 files in an hour, when they operate with composite identities spanning multiple systems, when they make decisions at superhuman speed, traditional IAM becomes not just inadequate but dangerous.
A recent Gartner report highlights that non-human identities now outnumber human ones by 40:1 in large organizations. Other reports referencing larger enterprises highlight ratios even higher—sometimes 60:1 or more when accounting for all the AI agents, service accounts, API keys, and machine identities proliferating across modern enterprises. Each of these represents a potential attack vector, yet most organizations can’t even tell how many they have, let alone what they can access or actions they can take.
Why Traditional IAM Falls Short in the AI Era
Accenture’s research confirms what we’ve been seeing firsthand: traditional IAM cannot keep pace with today’s dynamic threats. Legacy systems were built for a world of predictable access patterns, human-speed interactions, and well-defined perimeters. AI obliterates all three assumptions.
Consider the Morris II AI worm mentioned in the report—it can embed malicious prompts into AI models, allowing attackers to hijack systems without human intervention. Traditional IAM would never catch this because it’s not looking for self-replicating prompts or adversarial inputs. It’s checking whether a valid credential accessed a system, not whether that access pattern makes sense for an AI agent.
The report notes that only 37% of organizations assess AI security before deployment, despite 66% recognizing AI’s transformative impact. This gap exists because most security teams lack the tools to understand AI’s actual access footprint. They can’t see the permission chains, the inherited privileges, or the potential blast radius when an AI agent is compromised.
The Modern Identity Security Imperative
What resonated most deeply in Accenture’s findings was their emphasis on “AI-driven access intelligence.” This isn’t about adding AI to existing IAM—it’s about fundamentally reimagining how we govern identity in an AI-dominated landscape.
Modern identity security for AI requires several critical capabilities:
1. Real-Time Access Intelligence
The report emphasizes continuous authentication and context-aware controls. In practice, this means understanding not just who or what is accessing resources, but why, how, and whether that access aligns with expected behavior. When an AI agent suddenly accesses sensitive customer data at 3 AM, modern identity security should instantly surface the risk and enable automated response.
2. Unified Visibility Across Human and Non-Human Identities
Accenture correctly identifies that the distinction between human and non-human identities is blurring. Every identity—whether it’s a developer, an AI agent, or a service account—needs the same rigorous lifecycle management. This requires platforms that can normalize permissions across cloud, SaaS, data, and on-premise systems, translating technical entitlements into business-understandable risk.
3. Zero Trust at AI Speed
The report’s finding that Reinvention-Ready organizations are twice as likely to have implemented Zero Trust is telling. But Zero Trust for AI isn’t just “never trust, always verify“—it’s about verification at machine speed. This means automated policy enforcement, dynamic risk scoring, and the ability to revoke access in milliseconds, not minutes.
4. Granular Access Controls for AI Data Lifecycle
As Accenture notes, 91% of Reinvention-Ready organizations implement end-to-end encryption and granular access policies. But encryption alone isn’t enough. There is a need to understand and control access at every stage of the AI data lifecycle—during training, inference, and output generation. This requires identity systems that can enforce policies not just on data at rest, but on data in use by AI models.
From Reactive to Proactive: The Trust Architecture Advantage
What sets Reinvention-Ready organizations apart isn’t just their technology—it’s their mindset. They’ve moved from reactive security to proactive trust architecture. As I’ve written extensively, trust has become the currency of digital transformation, and nowhere is this more critical than in AI adoption.
The report’s economic modeling shows that a 10% increase in security investment can help organizations detect and remediate threats 14% faster. But the real value isn’t in faster response—it’s in preventing the need for response altogether. With real-time visibility into every identity’s effective permissions, with the ability to automatically right-size access, and to predict and prevent toxic permission combinations, the organization is not just defending—it’s enabling.
The Path Forward: Identity as AI Enabler
Accenture’s four-action framework provides a solid roadmap, but I’d add a critical fifth element: make identity security an AI enabler, not an AI inhibitor. This means:
Automate Everything Possible
The report notes that 71% of security analyst tasks can be augmented with AI. In identity security, this percentage can be even higher. Automated access reviews, intelligent role recommendations, and predictive risk scoring free teams to focus on strategic initiatives rather than manual processes.
Build for Attribution
Every AI action must be traceable to a responsible human. This requires identity systems that can maintain clear ownership chains, even as AI agents operate autonomously. It’s not enough to know an AI agent accessed data—there is a need to know who authorized that agent, who trained it, and who’s accountable for its actions.
Enable Business Velocity
The organizations succeeding with AI are those that make secure access frictionless. Modern identity security should accelerate AI adoption by providing clear guardrails, self-service capabilities, and real-time risk visibility that helps business teams move fast without breaking things.
The Bottom Line: Identity Is The AI Security Foundation
Accenture’s report makes it clear: the gap between AI adoption and AI security is widening dangerously. But for organizations willing to modernize their approach to identity security, this gap represents an opportunity.
The 10% of organizations in the Reinvention-Ready Zone aren’t there by accident. They recognized that in an AI-driven world, identity isn’t just about authentication and authorization—it’s about enabling innovation while maintaining control. They understand that every AI model, every automated process, every machine-to-machine interaction depends on identity as its security foundation.
As we race toward an AI-dominated future, the question isn’t whether to adopt AI—it’s how to do so securely. The answer starts with modern identity security that operates at AI speed, provides AI-scale visibility, and enables AI-powered innovation.
The path from Exposed to Reinvention-Ready isn’t easy, but it’s clear. It runs through identity. And for those willing to make the journey, the rewards—in terms of both security and business value—are transformative.
The time to act is now. In the race between AI adoption and AI security, identity security isn’t just a defense—it’s an accelerator.