-
 Identity Radicals
Identity RadicalsIdentity is the New Security Perimeter
Learn more -
 Identity Radicals
Identity RadicalsThe Trust Dividend: How Security Leaders Build Enterprise Value
Learn more -
 Compliance
Compliance7 user access review software tools to know in 2025
Learn more -
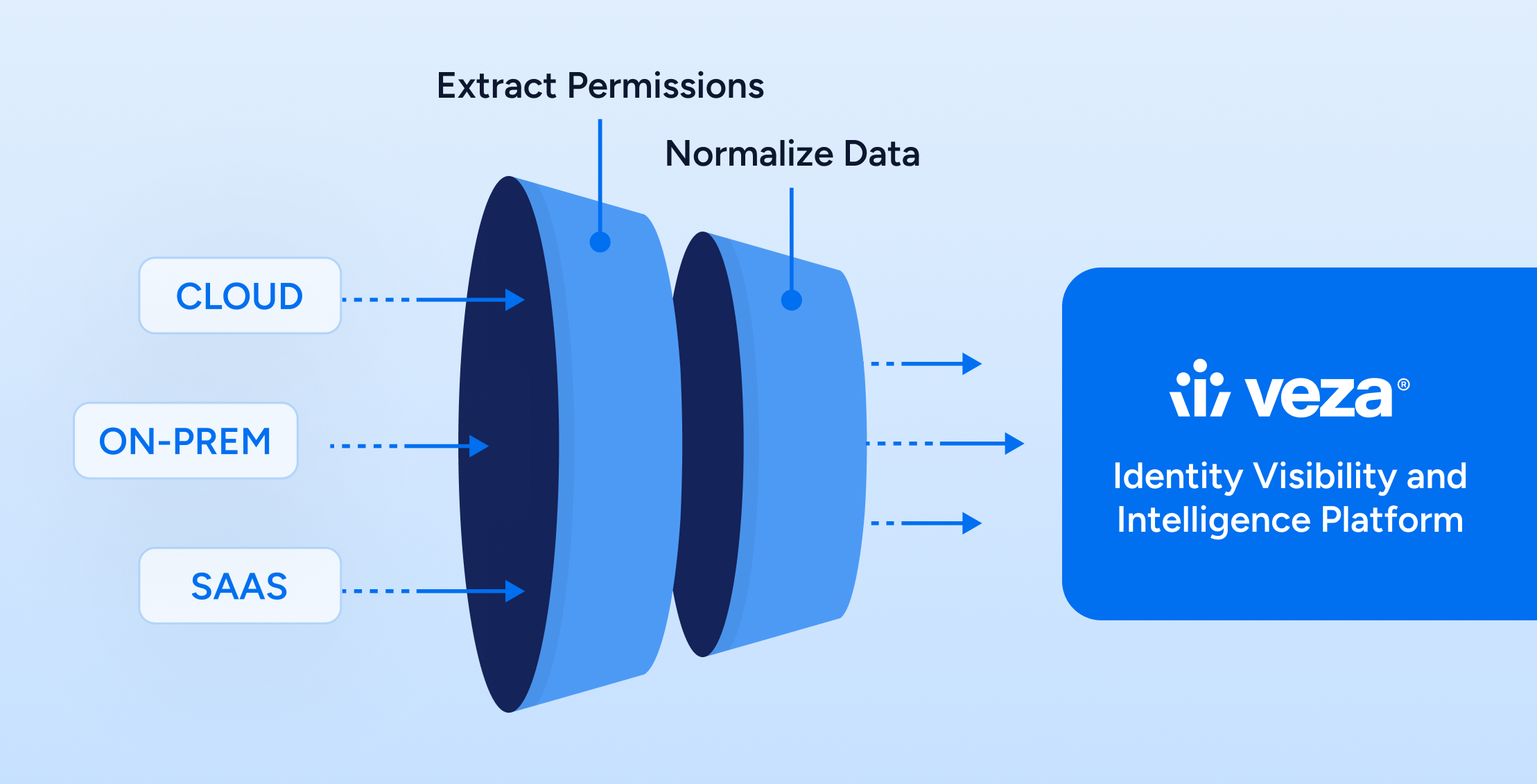
 Identity Security
Identity SecurityUnderstanding ISPM: Closing the Identity Gap with Identity Security Posture Management
Learn more -
 Compliance
ComplianceVeza for Oracle Applications: Solving the Access Management Puzzle
Learn more -
 IAM
IAMIdentity Attack Surface Analysis: Securing the New Perimeter
Learn more