-
 Identity Security
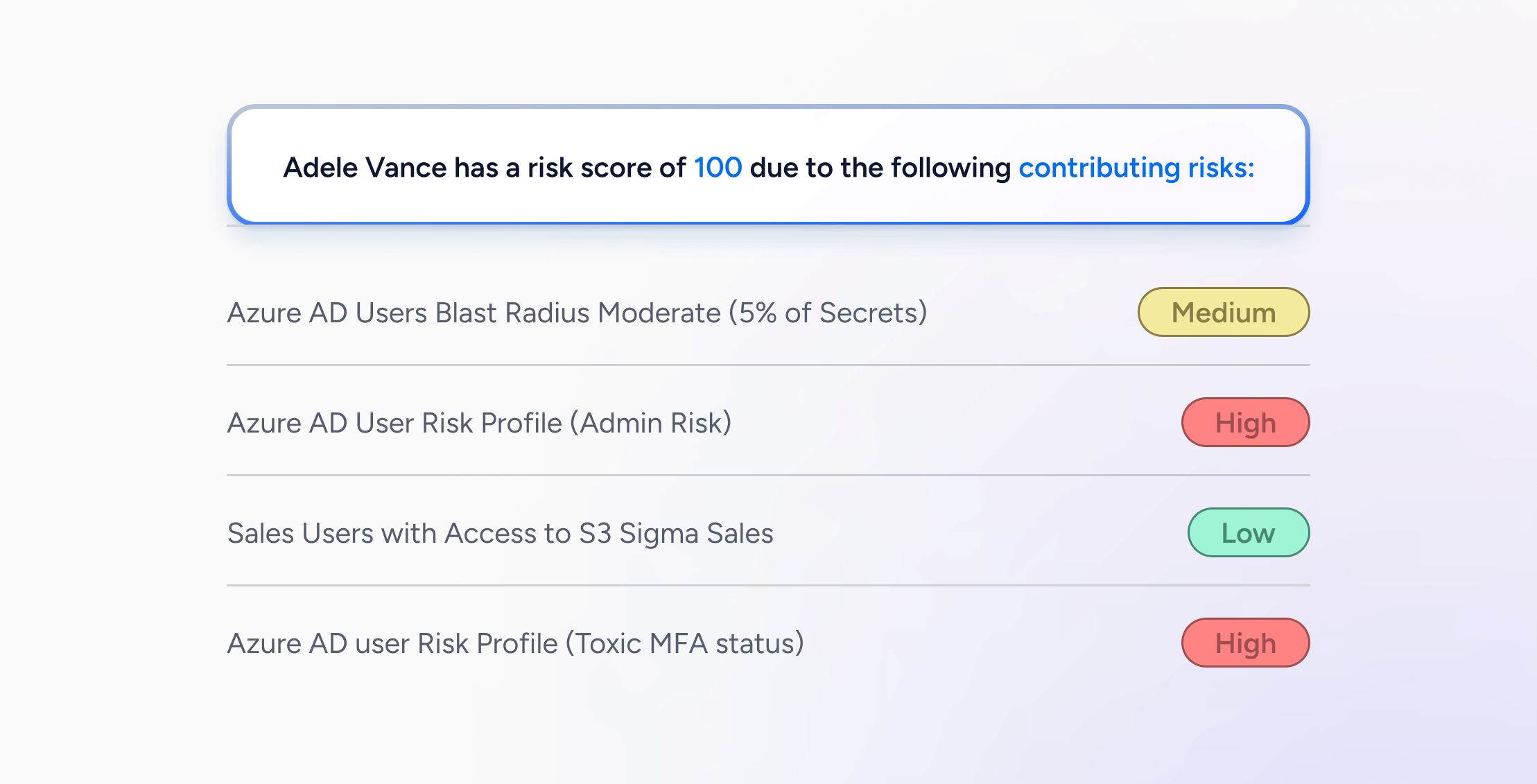
Identity SecurityApplication Risk Scoring: Enhance Identity Security
Learn more -
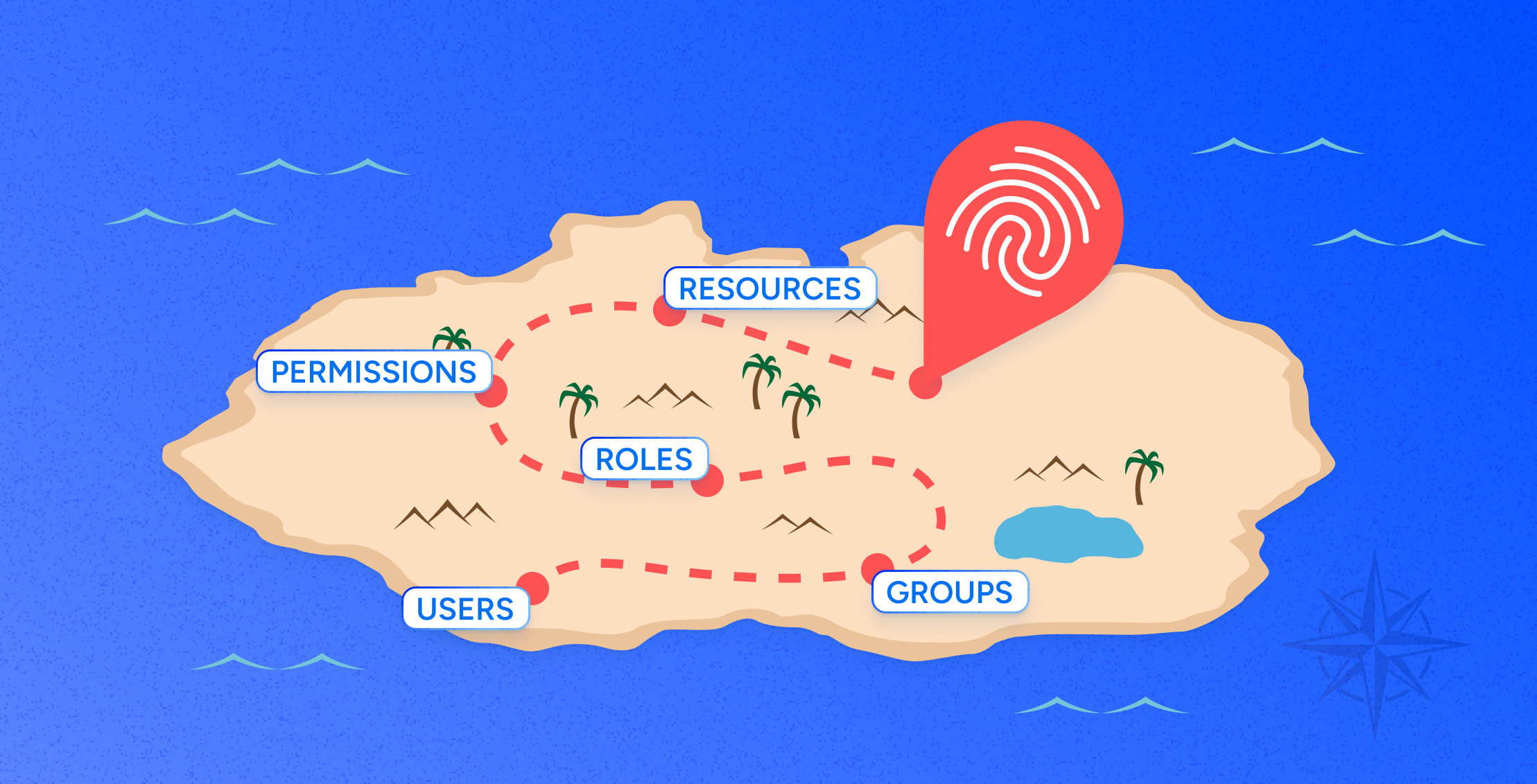 Identity Radicals
Identity RadicalsCharting a Path for the Future of Identity Security
Learn more -
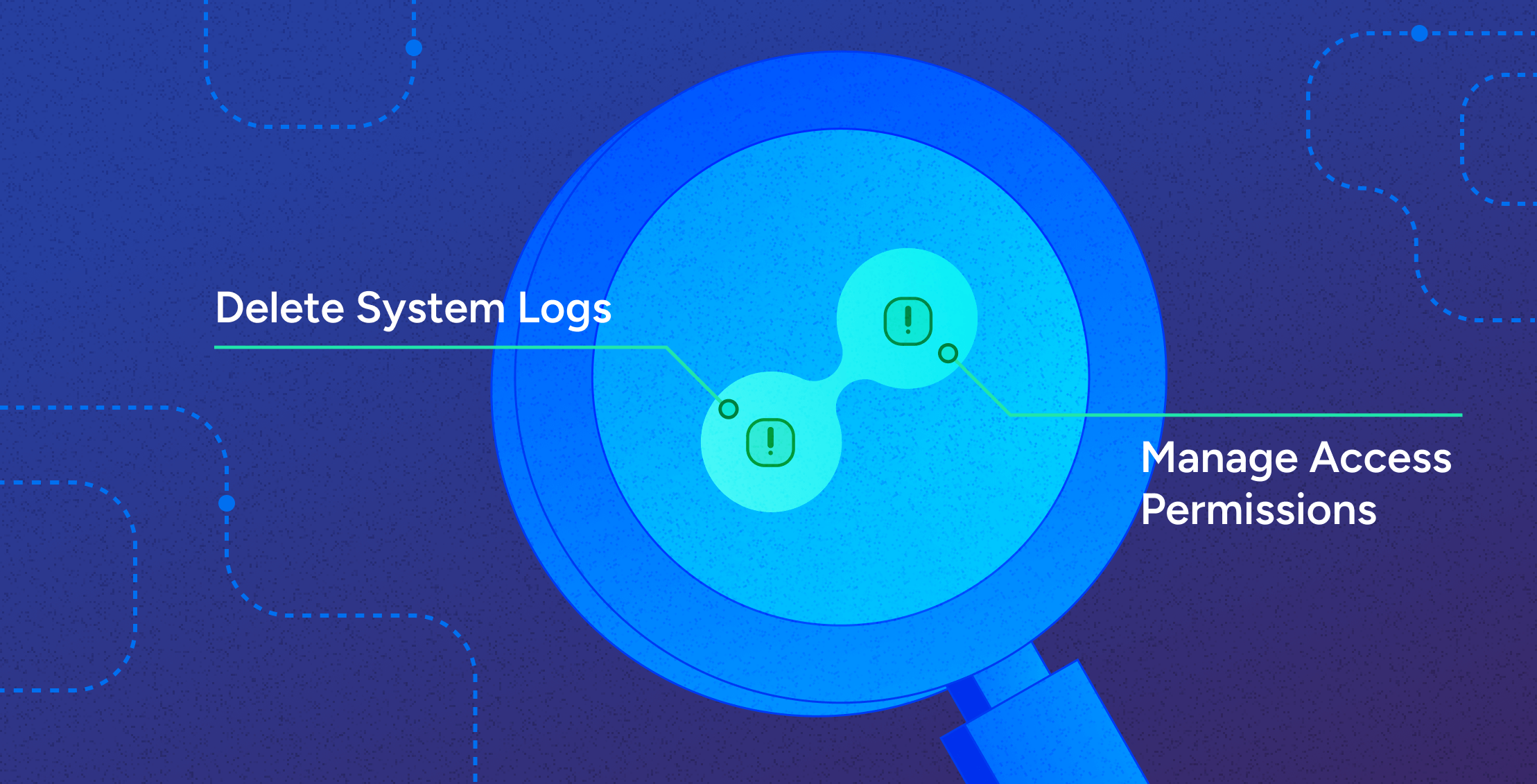 Compliance
ComplianceSeparation of Duties: Combating Toxic Combinations with SoD Controls
Learn more -
 Data Security
Data SecurityAccess AI: Introducing the Future of Identity Security
Learn more -
 Identity Security
Identity SecurityEmpowering Business Initiatives with Modern Identity Security
Learn more -
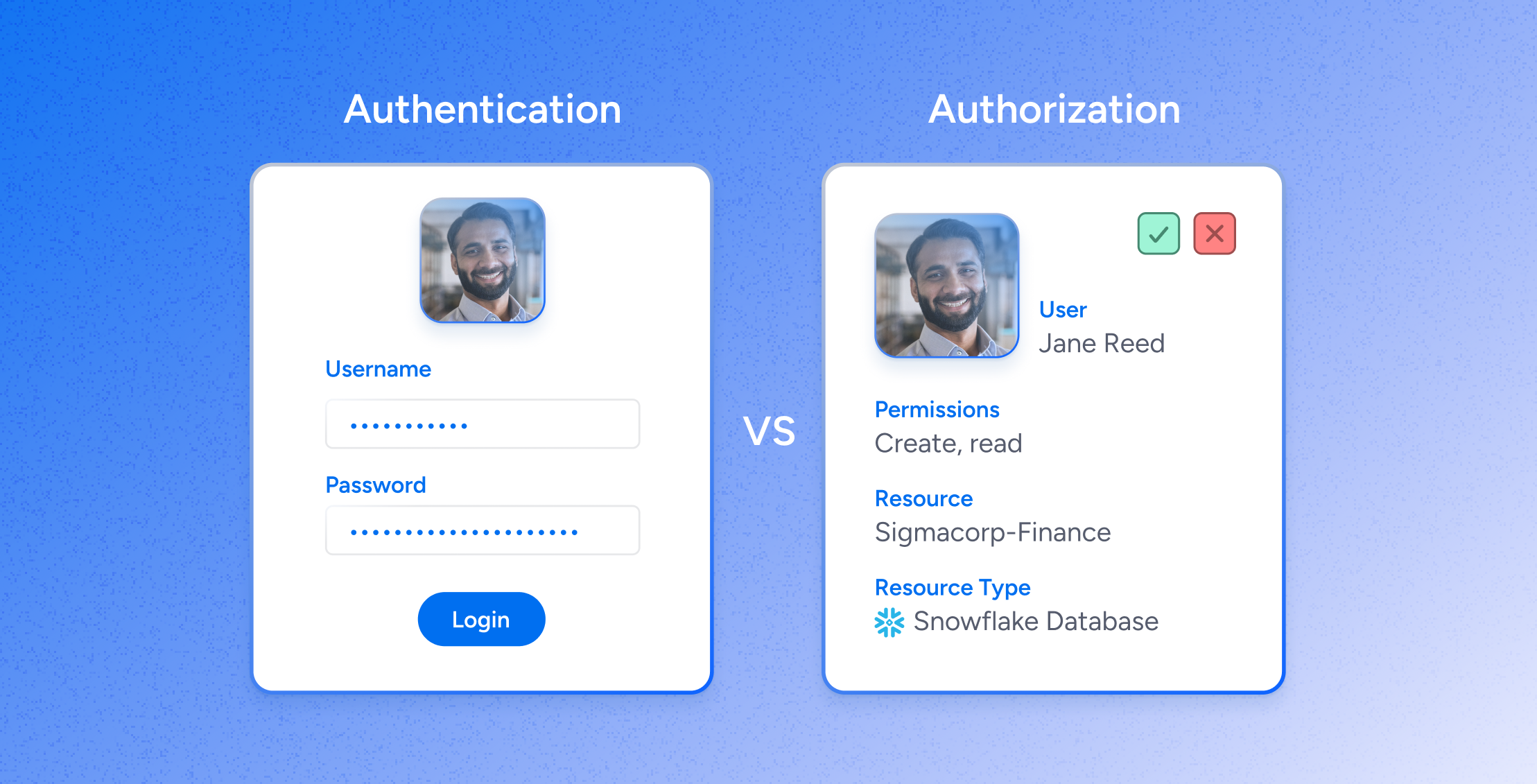
 IAM
IAMWhere Non-Human Identities (NHIs) and Human Identities Converge: A Comprehensive Approach to Identity Security
Learn more -
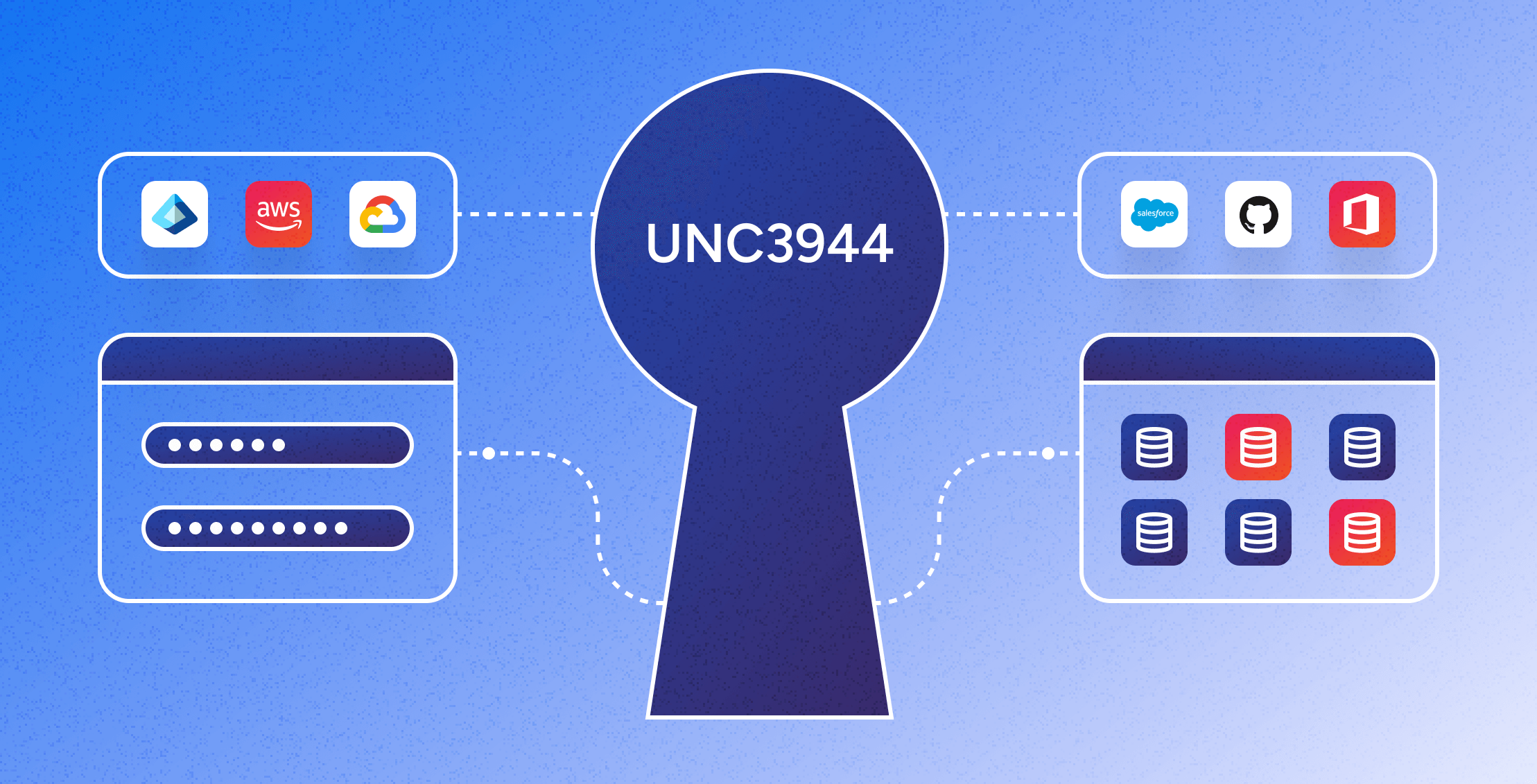 Identity Security
Identity SecurityMitigating the UNC3944 Threat: The Power of Modern Identity Security Platforms
Learn more -
 IAM
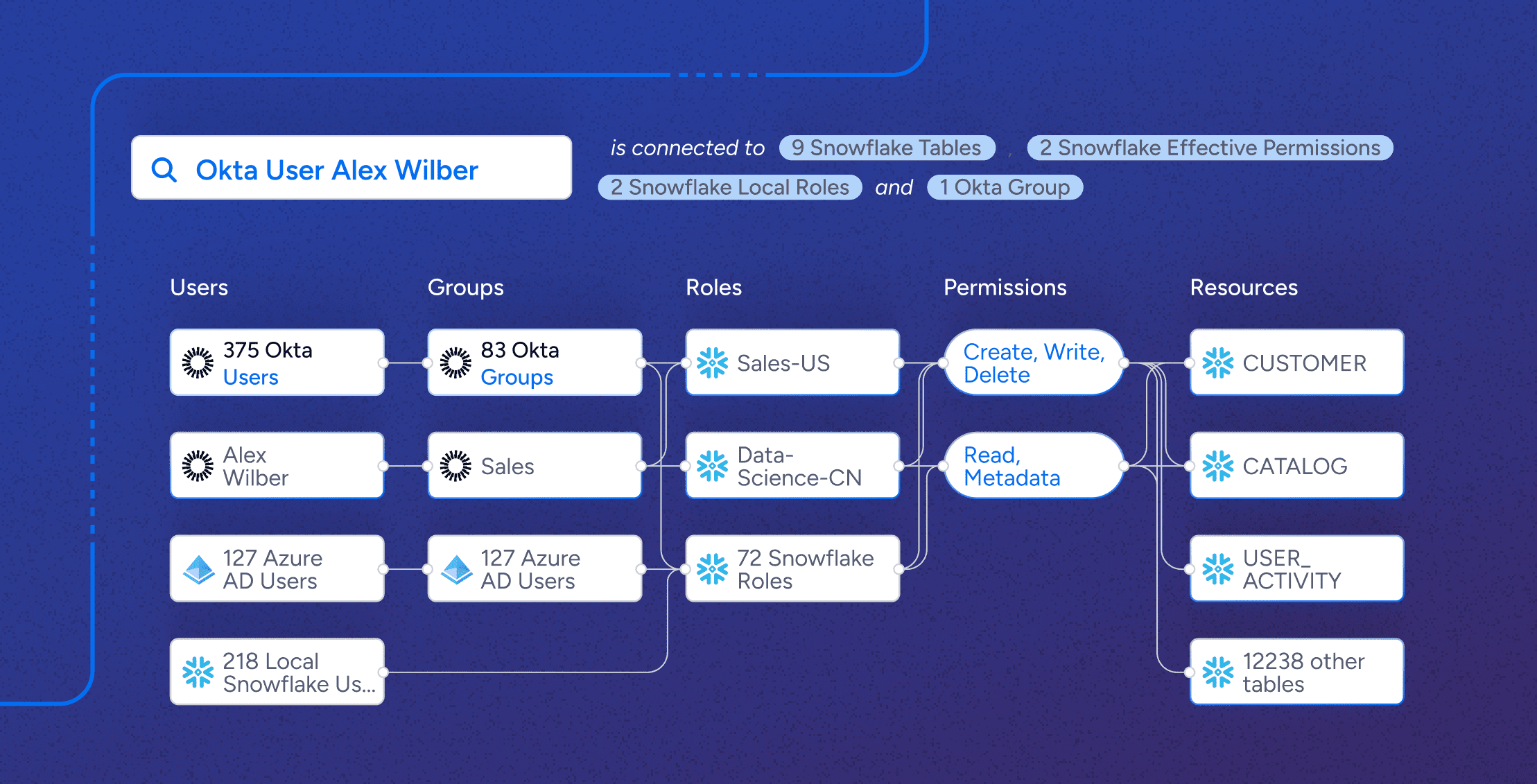
IAMSnowflake Roles Best Practices: Steps to Least Privilege
Learn more -
 Data Security
Data SecuritySnowflake View Permissions: Who Has Access to What?
Learn more