Non-Human Identities (NHIs)—the service accounts, bots, and API keys that run modern IT infrastructure—now outnumber human users by a factor of 17 to 1, according to the Veza 2026 State of Identity and Access Report. The report also highlights that a mere 0.01% of NHIs control 80% of cloud resources across the enterprise. While humans have MFA and single sign-on, NHIs are often overlooked, creating a massive “shadow” attack surface.
In this post we will share the top 4 best practices to secure your NHI lifecycle without compromising on deployment speed.
1. Establish a Single Source of Truth
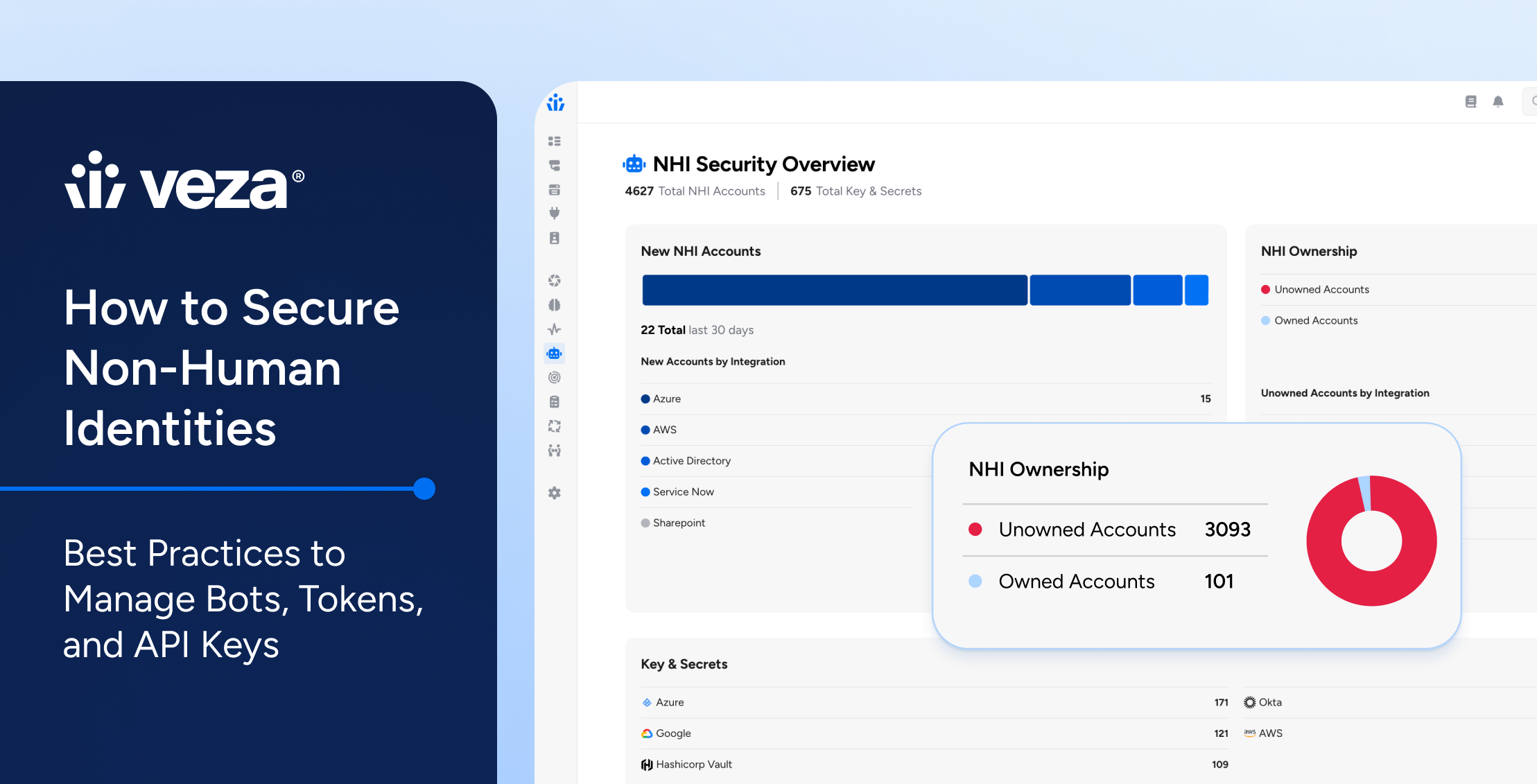
The biggest risk with NHIs is that you can’t protect what you can’t see. Most organizations have “orphaned” identities from former projects still holding administrative privileges.
Continuous Discovery: Move beyond static spreadsheets. Use automated tools to scan code repositories, CI/CD pipelines, and cloud environments to build a real-time inventory of every secret, token, and service account.
Assign Ownership: Every NHI should be mapped to a human “owner” or a specific engineering team. If an identity doesn’t have a clear purpose or owner, it should be flagged for decommissioning.
2. Implement “Identity-First” Security
Treat your machine identities with the same rigor as your human employees. If a developer needs MFA to access a server, why should a service account have a permanent, hard-coded key?
Principle of Least Privilege (PoLP): Review your NHI permissions. Many bots are granted “Owner” or “Admin” roles for simplicity during setup but only require “Read” access for a specific database.
Short-Lived Credentials: Transition away from “forever” API keys. Use Workload Identity Federation or ephemeral tokens that expire in minutes or hours rather than years.
Zero Trust Architecture: Never assume an internal NHI is safe. Require continuous verification for every request, regardless of where the bot is “calling” from.
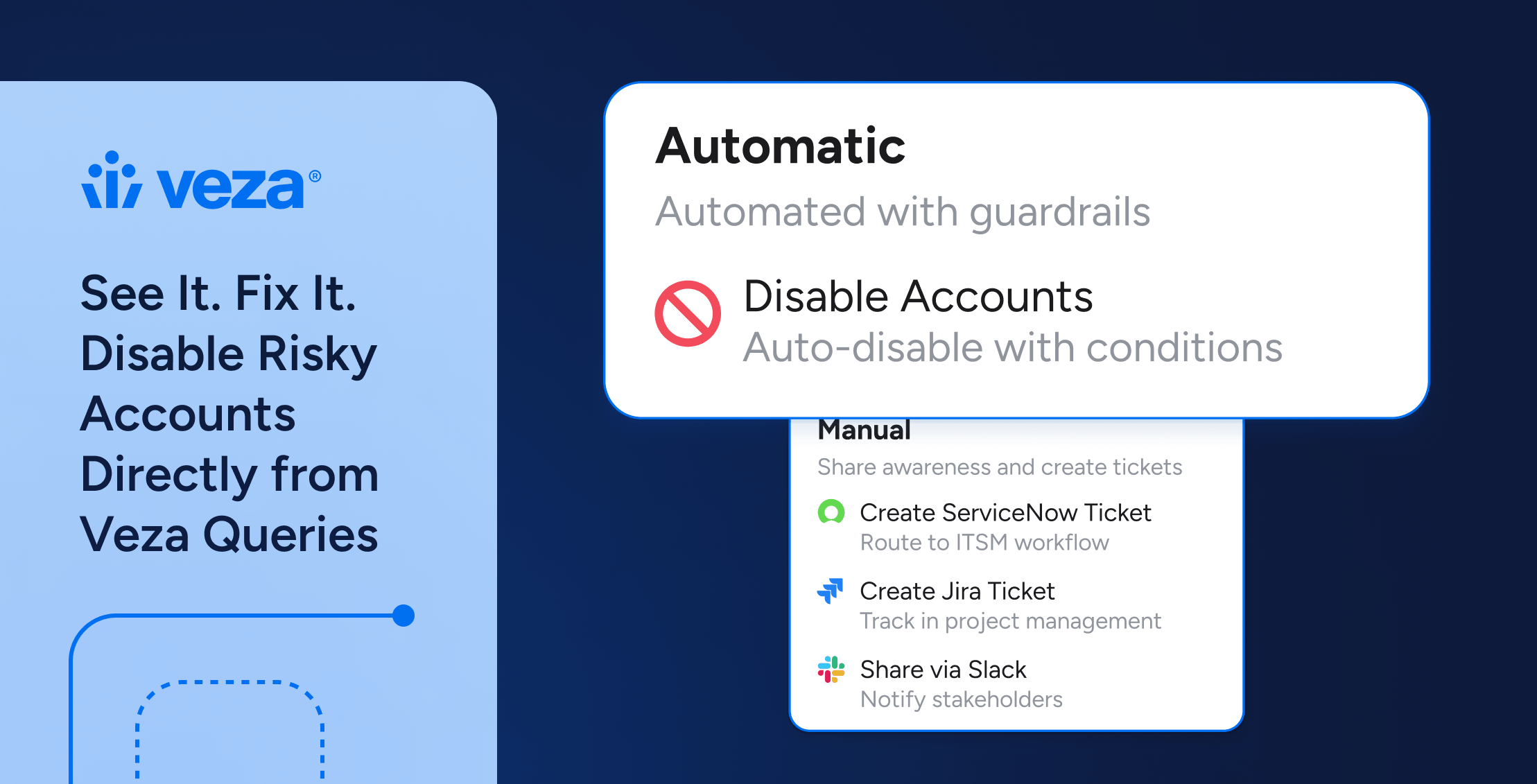
3. Automate the Lifecycle
Manual secret management is the enemy of security. Humans are prone to forgetting to rotate keys or leaving them in .env files.
Secrets Vaulting: Centralize all NHI credentials in a secure vault. Applications should pull secrets programmatically at runtime rather than having them hard-coded in the source code.
Automated Rotation: Set up automated workflows to rotate keys every 30–90 days. This limits the “blast radius” if a credential is leaked.
Rigorous Offboarding: When a workload or application is retired, the associated NHI must be deleted immediately. This prevents “shadow” identities from lingering in your environment.
4. Monitor Behavioral Patterns
NHIs are predictable. A backup bot should only behave like a backup bot. If it suddenly starts exporting user data at 3 AM from a new IP address, you have a breach.
Anomaly Detection: Establish a baseline for “normal” NHI behavior. Use monitoring tools to alert on spikes in API calls, unusual access times, or attempts to access unauthorized resources.
Audit Logging: Ensure every action taken by an NHI is logged. This is critical for forensic analysis if a machine identity is compromised.
Summary Table: Human vs. Non-Human Identity
| Feature | Human Identities | Non-Human Identities (NHI) |
|---|---|---|
| Volume | Low (1x) | Extremely High (45x+) |
| Security | MFA, SSO, Biometrics | API Keys, Tokens, Certificates |
| Lifespan | Long (Years) | Variable (Minutes to Years) |
| Behavior | Unpredictable | Highly Predictable |
A final word of encouragement for the operations teams in the middle of this battle: The sheer scale of NHI management can feel overwhelming, but the secret lies in a classic engineering principle: decomposition. Break the identity lifecycle into its smallest, most manageable units.
By building a systematized, repeatable workflow, much like a software delivery pipeline, you can transform an unmanageable volume of identities into a streamlined process. As automation takes over, the operational burden drops, ownership becomes clear, and your attack surface is significantly mitigated.