Mergers, acquisitions, and divestitures are a part of the healthy and dynamic business environment. However, they introduce massive security, compliance, and operational risk as organizations rapidly combine and separate identities, systems, and access.Their identity programs rarely keep pace with this chaos.
Instead, security teams inherit a patchwork of directories and unknown identity architectures, unmanaged non-human identities, and permission sprawl that neither legacy IGA tools nor cloud identity providers can fully address.
Identity (employees, third parties, service accounts, AI agents, and machines) is the connective tissue of modern enterprises. If identity isn’t unified, nothing else in the business can be.
This is where Veza stands apart.
The Identity Problem during Mergers, Acquisitions, and Divestitures: Complexity, Blind Spots, and Risk
Identity challenges surface not only when organizations integrate new acquisitions, but also when they must cleanly separate identities and access during divestitures, often under even greater regulatory scrutiny.
1. Fragmented Identity Stores
Acquired or divested companies bring their own tech stack: Microsoft Active Directory, HR systems, Identity Providers (IdPs), SaaS apps, CI/CD pipelines, secrets managers, and more. This creates Identity sprawl. There’s no single source of the truth.
Each contains different scopes for “user,” “group,” “role,” and permissions, making consolidation or clean separation nearly impossible with traditional tools.
Legacy IGA tools do not provide the full visibility as they have challenges visualizing nested groups and roles. Further, they do not normalize effective permissions into simple natural language (create, read, update, delete) that can be understood by non-technical people in the organization.
2. Outdated or Unknown Access
Teams must answer critical questions immediately:
Who are these users spread across multiple IdPs?
Who currently has access to what?
Where do dormant or orphaned accounts exist?
Which entitlements create compliance or segregation-of-duties violations?
What non-human identities and AI agent identities were created, and who owns them?
Who still has access to systems that are being divested?
Which identities violate the principle of least privilege?
Legacy IGA platforms have challenges connecting to all of an organization’s apps and mostly focus on groups and roles. They miss permission-level details.
3. Onboarding & Offboarding at Speed
Business leaders want fast integration. Regulators want proof of control. During M&As, the instances of employees leaving, joining and moving to different roles happen in a concentrated span of time. Lack of a clear line of sight into these dynamic activities leaves a massive blindspot. An overprivileged disgruntled employee might be accessing sensitive data for nefarious purposes.
In divestitures, the problem reverses: organizations must rapidly and precisely remove access without disrupting remaining business operations.
In both cases, manual, script-heavy provisioning processes simply do not scale. They are time-consuming and error-prone.
4. Regulatory Scrutiny Intensifies
Banks, healthcare providers, and public companies experience a spike in audits. Regulators demand proof of “who has access to what.”
During divestitures, this challenge reverses. It requires fast, precise access removal without breaking business operations.
Identity failures become deal blockers.
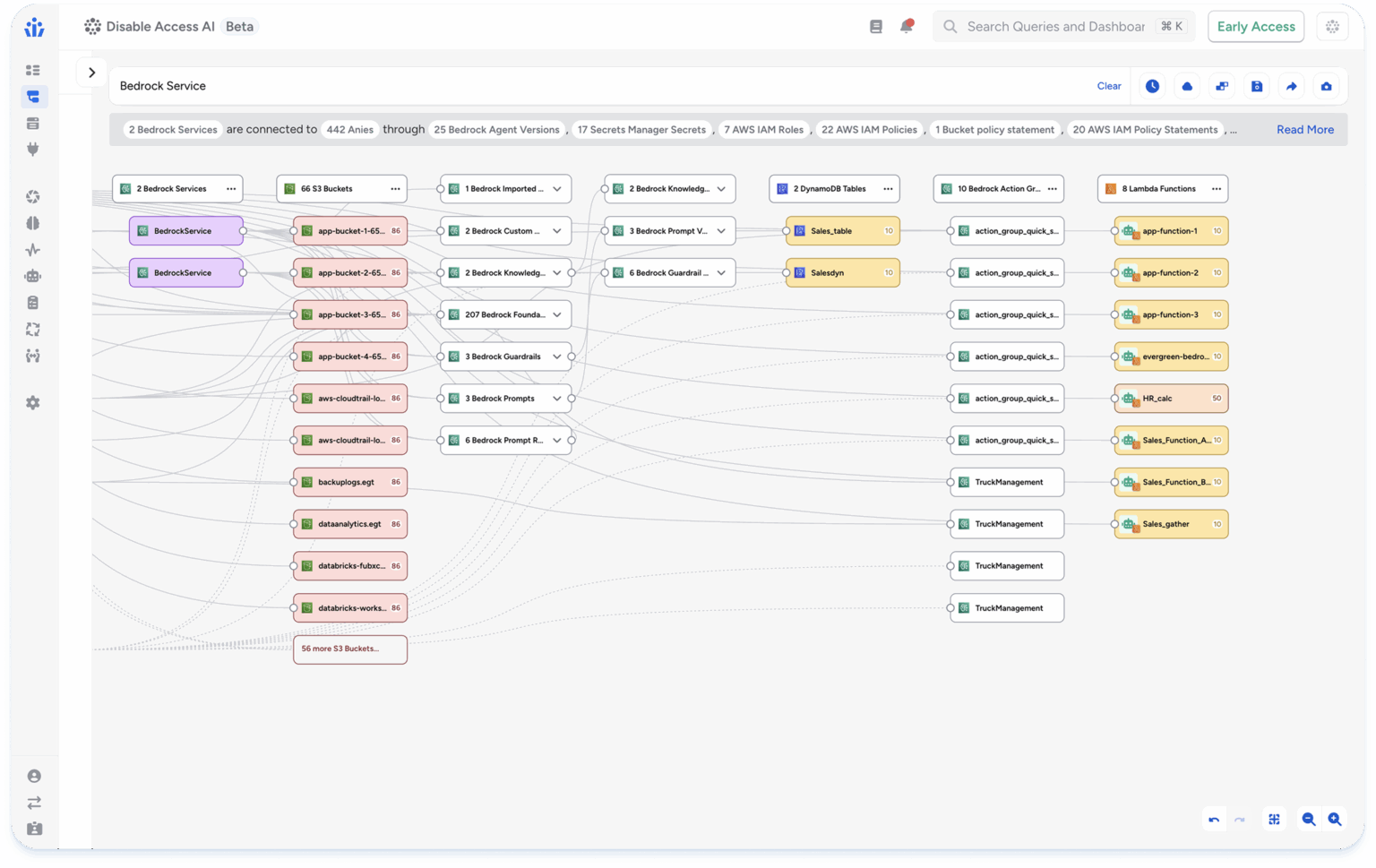
5. Non-Human Identity & AI Agent Security Multiply Risks
Mergers and acquisitions dramatically increase the number of non-human identities (NHIs) and AI agents (service accounts, API keys, cloud roles, automation, and autonomous agents) that often lack clear ownership or governance.
These identities frequently carry broad, persistent permissions and are rarely reviewed during M&A, creating blind spots that traditional IGA and PAM tools were not designed to address. As AI agents take on more autonomous actions, inherited machine access can significantly expand the attack surface and regulatory risk if left unmanaged.
Why Veza Solves Identity Challenges in Mergers, Acquisitions, and Divestitures Better Than Any Other Platform
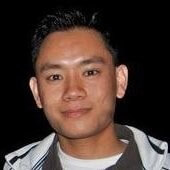
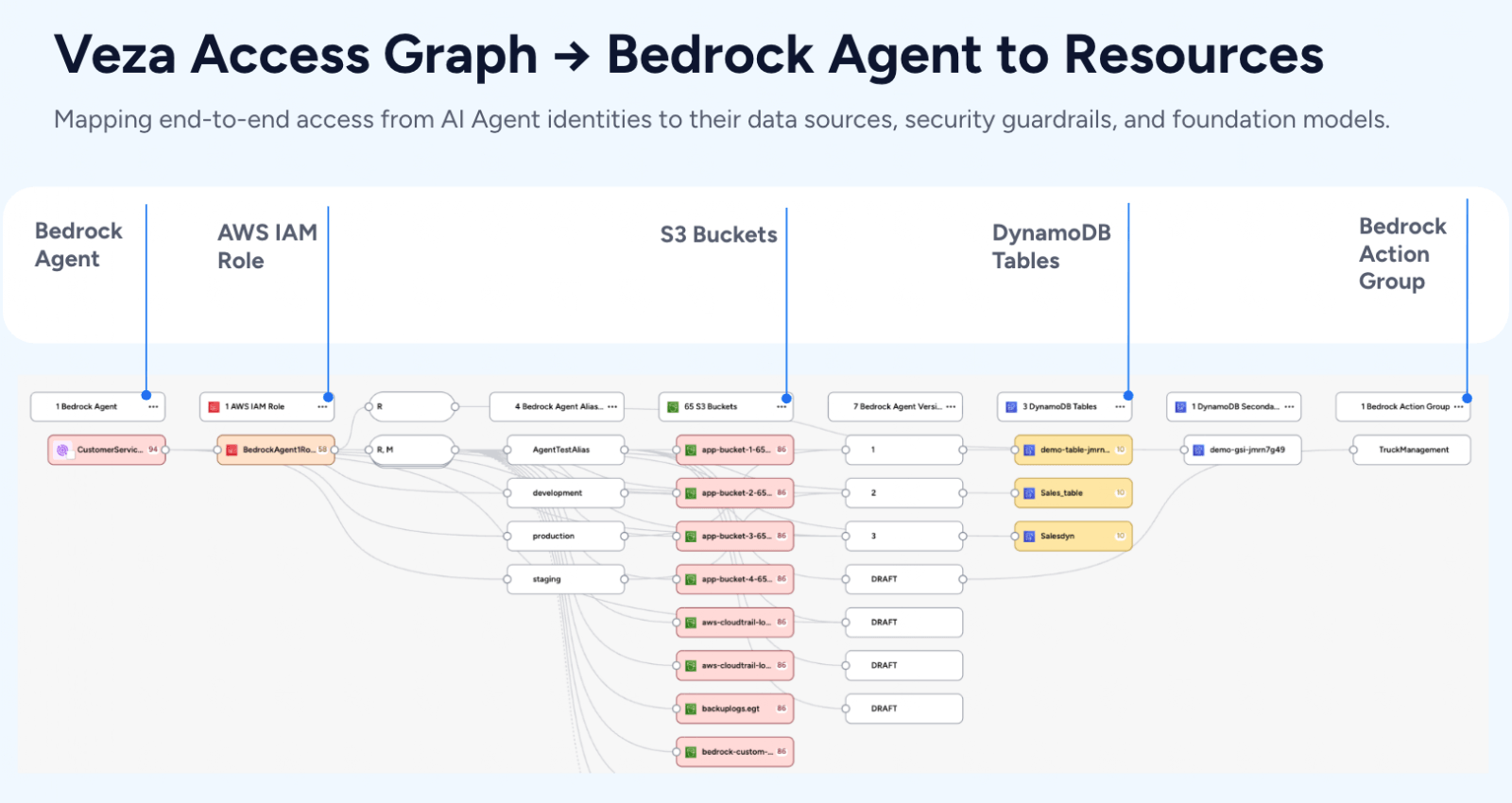
Veza is built on the Access Graph, a normalized, permission-level map of every human, non-human, and AI Agent identity across all systems.
Instead of relying on brittle connectors or generic roles, Veza gives organizations a unified, end-to-end view of identities to resources, improving visibility during M&As.
1. Unified Identity Visibility Across Both Organizations
Veza unifies disparate systems, apps, and fragmented identities:
One normalized data model means one truth.
This is why a major global hospitality company chose Veza to gain immediate visibility into the identity infrastructure they inherited from an acquired company.
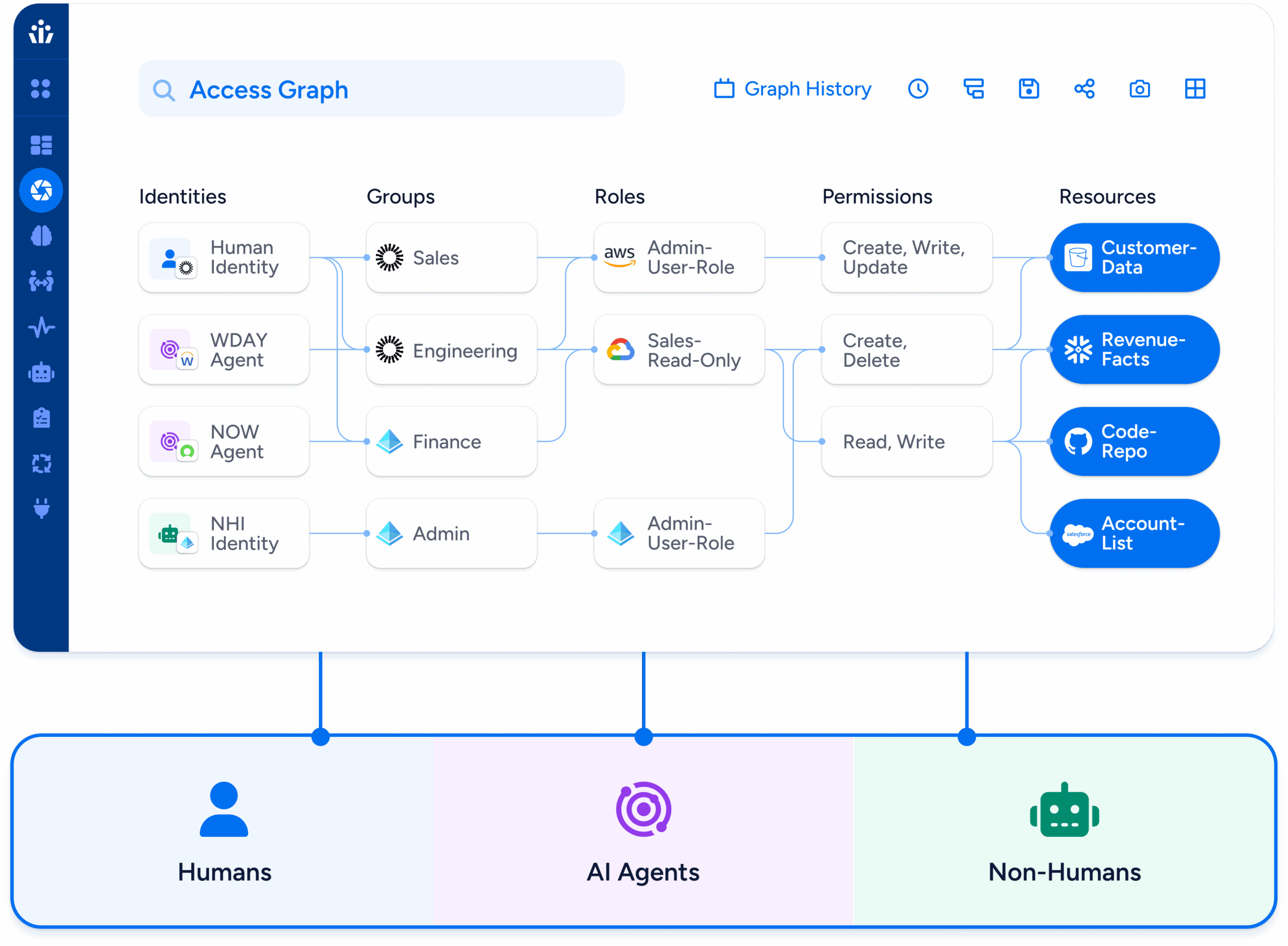
2. Fast, Accurate Mapping of Every Permission
Veza shows:
When a company merges, unknown permissions create a massive attack surface. Veza eliminates that uncertainty on Day 1.
After aggressive M&A activity that created identity sprawl across disconnected systems, a business services company embraced Veza’s modern IGA approach—starting with visibility into their identity sprawl to lay the foundation for a scalable identity governance program.
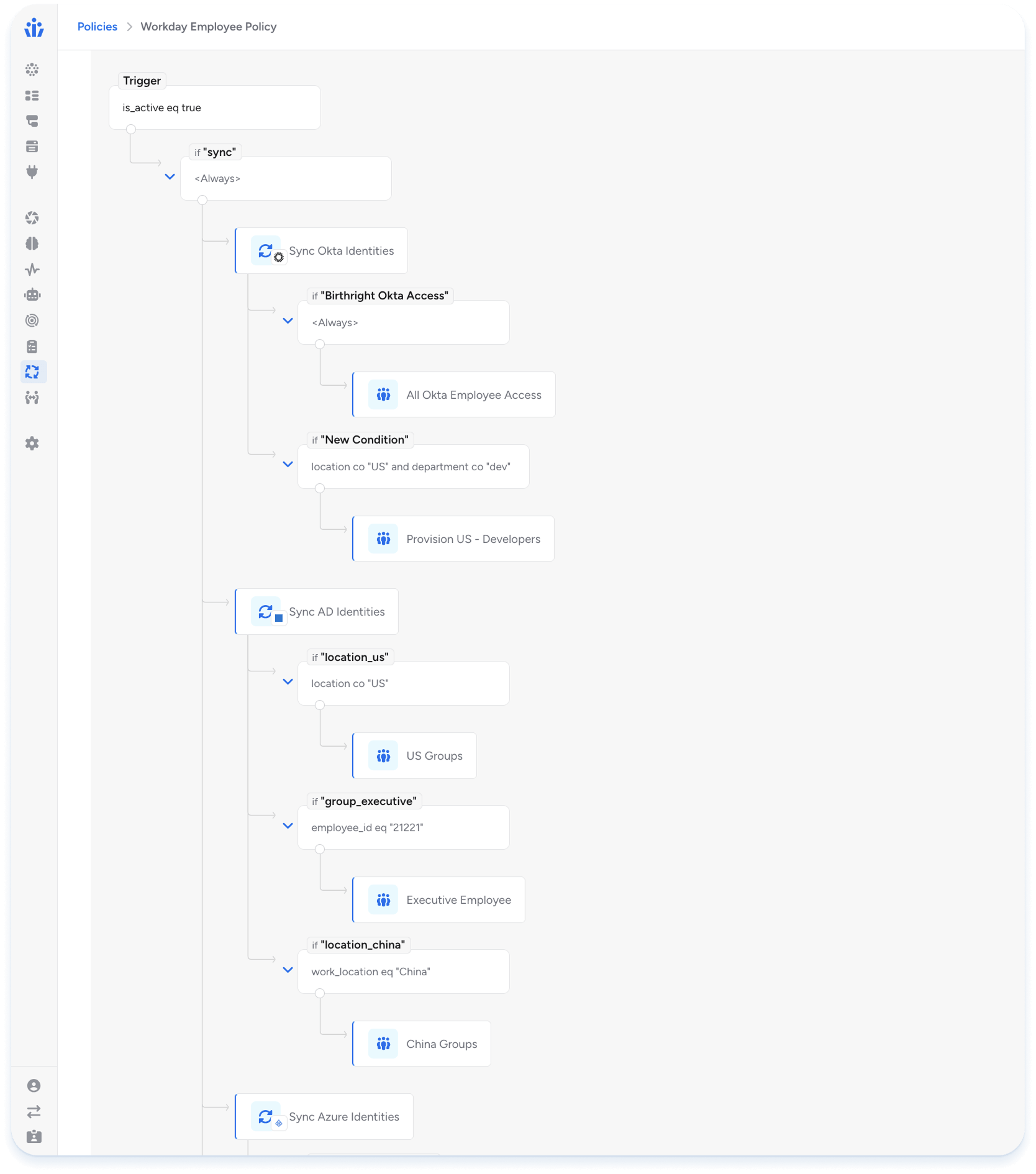
3. Automated, Risk-Aware Onboarding & Offboarding
Veza enables:
A software provider used Veza to automate provisioning for a new business unit—without the complexity of traditional IGA.
4. Rapid Compliance Alignment
Deal teams can’t proceed without audit-ready proof of:
A US bank was growing rapidly via acquisition. Regulators (FDIC, OCC, and Federal Reserve) demanded proof of “who had access to what” and evidence of risk reduction before approving further acquisition. They chose Veza to reduce their identity sprawl and consolidate identity visibility across 2,000+ applications after acquiring multiple banks.
5. Securing Non-Human Identities (NHIs) and AI Agents Across Merged Environments
M&A doubles or triples hidden NHIs. According to Veza’s State of Identity & Access 2026 report, just 0.01% of NHIs control 80% of cloud resources across enterprises—meaning a very small number of accounts can bring an entire business to a halt.
API keys | Service accounts | Bots | Terraform identities | AI agents
Veza is the first unified platform that:
A European bank, formed through a major financial merger, relied on Veza to uncover thousands of risky, inherited service accounts across legacy Active Directories (AD). Prior to Veza, they had shut down what they thought was a dormant service account only to create an outage.
How Veza Supports the Full M&A Lifecycle
Due Diligence/Identity Assessment
This is the task, typically done by the acquiring company, to understand and assess what the identity landscape of the acquired company looks like. This includes outlining risks, developing project plans, and asking for budget allocations. This could be done as part of the official pre-merger due diligence process, but, more often than not, it is after the fact. In either case, it is done on an extremely tight timeframe and has the highest level of executive visibility.
Veza allows organizations to:
Divestiture Identity Redesign and Validation
Divestures pose a particular challenge for identity professionals. In particular, they require separating a single organization into multiple entities, each with their own identity systems. Data and permissions for each organization must be distinct and not violate the new organizational boundaries. Once designed, the implementation must be done and validated for auditors, and is often in the critical path timeline for completing the transaction.
Veza allows organizations to:
Post-Merger Integration
After a merger closes, then the real work begins! Due to lack of visibility, many identity systems and architectures of acquired companies simply run alongside existing ones in perpetuity. Then, at some point, the complexity becomes overwhelming and a massive “identity integration” project is kicked off to try and repair years (or decades) of technical debt. Handling integrations as they come and developing a playbook for future integration saves a tremendous amount of time with modest up-front investment.
Why Veza Delivers What Legacy Identity Tools Can’t
| Requirement | Legacy Tools | Veza |
|---|---|---|
| Permission-level visibility | Limited, app-by-app | Unified Access Graph across all systems |
| Fast integration of acquired apps | Slow, complex, PS-heavy that take months | Hours to days to integrate apps |
| NHI and AI Agent discovery & ownership | Minimal or none | Comprehensive NHI & AI agent identity security |
| Multi-cloud & SaaS entitlement visibility | Incomplete | Full effective permissions + usage context |
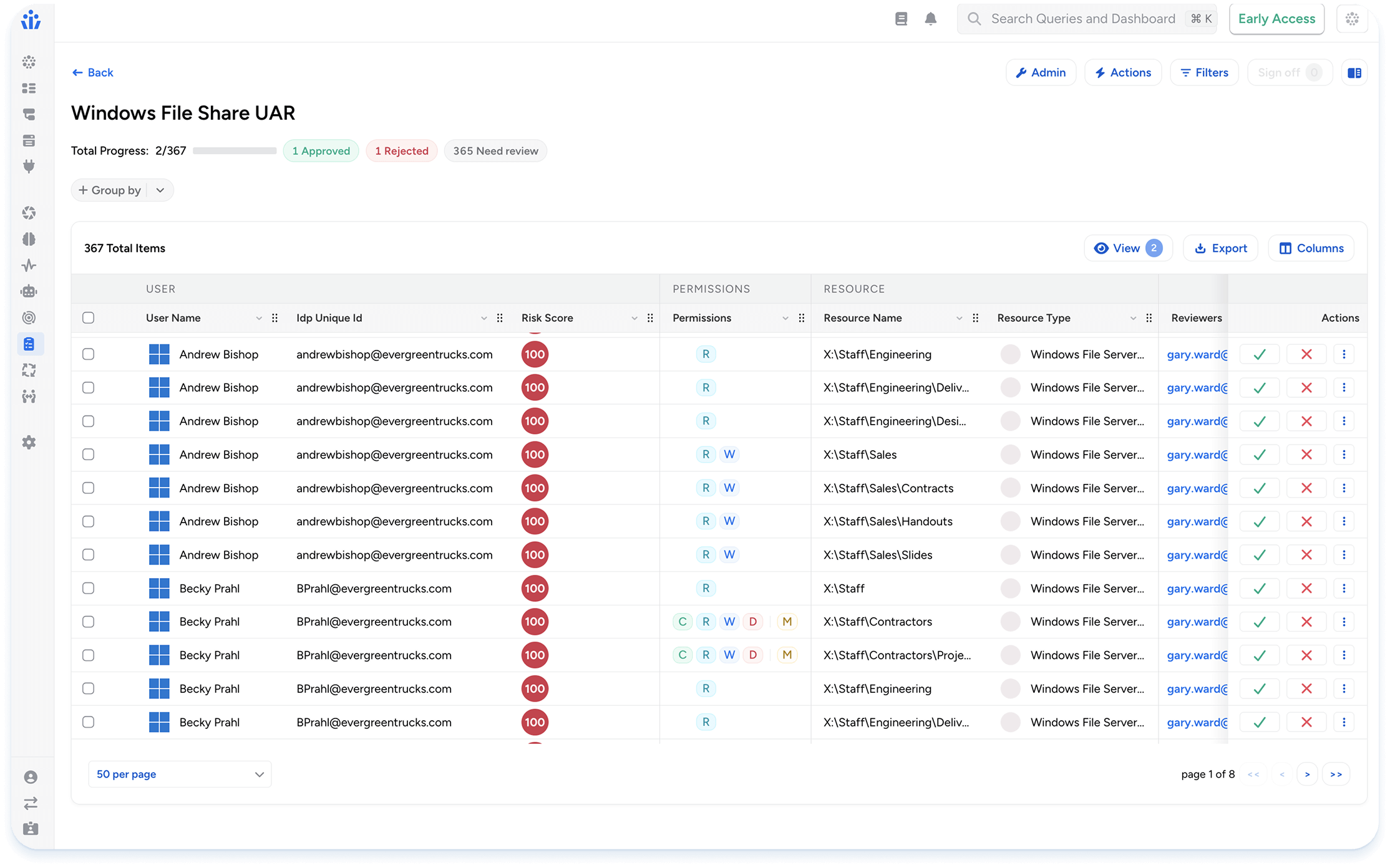
| Access Reviews | Narrow, role-only | Enterprise-wide, risk-based reviews and targeted micro-certifications |
Identity Security During Divestitures
While much of the focus in M&A is on integrating identities, divestitures often present an even greater security challenge. When a business unit is carved out, especially in highly regulated industries, organizations must prove, often under tight timelines, that access has been fully and correctly separated.
This requires answering critical questions:
Who still has access to divested systems?
Which identities, roles, and service accounts must be removed or retained?
Are there any lingering permissions that could expose sensitive data post-transaction?
A software provider faced this challenge while divesting a highly regulated business unit. They needed immediate, permission-level visibility to ensure that access was cleanly separated before the transaction could proceed.Rather than relying on traditional Identity Security tools that stakeholders viewed as expensive, slow to deploy, and offering limited visibility, the organization turned to Veza. Veza quickly delivered a unified view of who had access to what across the environment, enabling the team to confidently complete the divestiture without introducing residual risk.
Another example comes from a financial services customer, which was divesting several business units. Traditional IGA tools would have required larger access review campaigns, along with coordinating constant review meetings with the business teams. Instead, the customer used Veza to time-bound and run targeted micro-certifications. This allowed the team to progressively remove access, enforce least-privileged controls and provide clear, auditable proof that access was being safely and systematically separated throughout the divestiture process.
Conclusion: Mergers, Acquisitions and Divestitures Demand Vendor Agnostic Identity Visibility With Data-Driven Insights
Every merger introduces identity debt. Every acquisition expands the attack surface.
Veza gives organizations the ability to:
If identity is the new perimeter, then Veza is the only platform with the depth, scale, and agility to secure that perimeter through the chaos of M&A.