In today’s complex IT landscape, managing who has access to what and why is a critical challenge. Smart organizations knew they needed to implement the principle of least privilege across their applications, systems, and platforms, but traditional identity management and identity governance tools struggled to meet the challenge. This is why Veza developed the Access Graph, our industry-first approach to deeply understanding permissions and entitlements as the purest form of identity access. With access visibility to true permissions, organizations now needed a framework for defining access across their applications and systems over the end-to-end user access lifecycle. Enter Veza’s Access Profiles, a powerful framework designed to streamline access provisioning and deprovisioning, ensuring least privilege and compliance across diverse systems and platforms.
The Challenge of Traditional Identity Governance
Traditionally, identity governance has struggled with visibility. Organizations often lack a clear picture of who holds which permissions, leading to over-privilege as well as associated security risks and compliance issues. Legacy “entitlement catalogues” promised a solution but frequently failed due to complicated integrations and lengthy, expensive deployments, leaving many organizations frustrated.
The Veza platform stands out from legacy IGA tools by offering dramatically faster and more agile integrations allowing constructs like Access Profiles to support entitlements from any Veza-integrated application. This provides a significant time-to-value advantage over traditional IGA tools.
Access Profiles: Building Blocks for Access Lifecycle Management
Veza’s Access Profiles act as building blocks defining collections of permissions and entitlements. These profiles can be tailored to specific needs, whether for birthright access or user-requested just-in-time access. Unlike application-specific roles, Veza’s Access Profiles are application-agnostic, mapping disparate entitlements across various systems and platforms.
Key Features of Veza’s Access Profiles
- Built on the Veza Access Graph: Leveraging a deep understanding of permissions and entitlements.
- Integrated with Veza Lifecycle Management and Access Requests: Supporting both birthright provisioning and just-in-time (JIT) access requests.
- Cross-Application and Cross-Platform: Encapsulating different types of entitlements across various applications.
- Strongly Typed: With the ability to create custom Access Profile types.
- Flexible Modeling: Supporting both flat and hierarchical structures.
- Delegated Management: Allowing designated owners and administrators to jointly manage profiles.
- Manageable via Console, Access Hub, or API: Providing multiple management options.
- Integrated into identity governance processes: As a first-class access granting entity, changes to Access Profiles can be subject to review and approval processes; versioning and rollback are supported; and the contents, membership, and ownership of Access Profiles can also be periodically reviewed using Veza Access Reviews as part of regular access review campaigns
- Scalable: Expanding support as more applications are integrated into the Veza platform.
Types of Access Profiles
Veza offers several out-of-the-box Access Profile types:
- Application Only: Granting access to an application without specific entitlements, such as access to Zoom.
- Single Entitlement: Defining a single entitlement within a single application, such as a user being added to the DNS Admin group in Active Directory or the Domain Name Administrator role in Entra ID.
- Application Entitlements: Defining multiple entitlements within a single application, such as access to multiple Okta Groups.
- Multi-Application Entitlements: Defining multiple entitlements across different applications, such as access to different applications, such as site reliability engineers who need access to GitHub, AWS, Jira, and Snowflake, along with one or more roles and group memberships within each of those applications.
- Business Roles: Inheriting combinations of other profile types to model sophisticated access privileges, such as all US Call Center employees inheriting US Employee access.
Custom Access Profile types are also supported for unique organizational needs.
Access Profile Automation
Access Profile Automation simplifies defining, governing, provisioning, and de-provisioning access. By defining rules and policies, organizations can manage user access throughout their lifecycle effectively. For instance, Access Profiles are heavily leveraged by Veza Lifecycle Management and Access Reviews, streamlining birthright provisioning, access requests, and access removal.
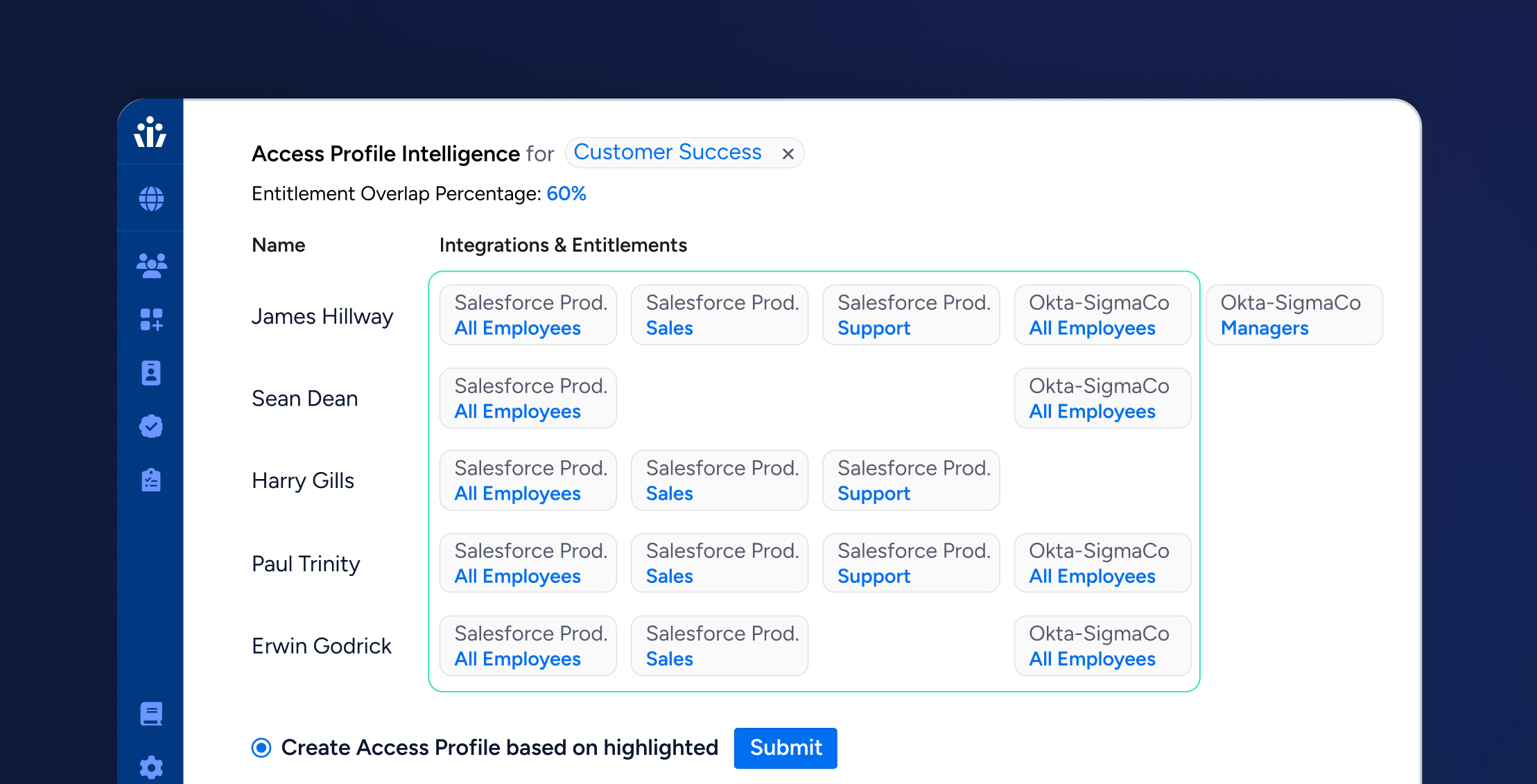
As part of the automation, Veza’s Access Profile Intelligence accelerates the creation of Access Profiles by analyzing existing entitlement assignments and providing a starting baseline. The two main approaches used are:
- Analyzing a single “typical” user’s entitlements as a baseline.
- Analyzing overlapping access entitlements from a group of related users.
For instance, the first approach is convenient for building Access Profiles for task-based user personas, especially non-knowledge workers. However, this method should be used sparingly and with caution because often the “best known” example of a worker in a given position is one who has been in that position for years and accumulated excess permissions over time.
The second approach can be applied to scenarios where an existing user cohort may have some diversity in each member’s access entitlements, but the overlapping access in common across the cohort yields a good starting point for determining baseline access to be granted to new members of the cohort.
While both these methods provide a starting point, administrators can always manually adjust the entitlements when building Access Profiles.
Managing and Governing Access Profiles
Veza provides a delegated management model, allowing both administrators and designated owners to manage profiles. Leverage Veza’s self-service Access Hub, designated Access Profile owners can manage membership (including requests for membership) and ownership. Administrators have comparable permissions, but a few additional privileges including adjusting entitlements and defining the Lifecycle Management workflows and access catalog items that leverage Access Profiles from within the Veza console.
Additionally, changes to Access Profiles can be subject to review and approval processes with support for both versioning and rollback. Governance is further enhanced through Veza Access Reviews, which supports recertifications of Access Profile memberships, ownerships, and application entitlements. Access Profiles also have the distinct advantage of simplifying the access recertification process by bundling many entitlements across multiple applications into relatively fewer profiles, making it easier for managers and application owners to understand and recertification user access on a regular basis.
Conclusion
Veza’s Access Profiles offer a powerful solution for transforming access lifecycle management. By simplifying the definition, provisioning, and governance of access, organizations can improve their security and compliance posture with better implementation of least privilege principles as well as gain efficiencies through more consistent birthright and just-in-time provisioning. With features like Access Profile Automation and delegated management, Veza empowers organizations to more effectively control and review user access in a more distributed manner while reducing overprivilege risk and streamlining compliance efforts.