As T-Mobile’s EVP, CIO, and Chief Product Officer, my team and I led the company’s digital transformation into a more cloud-based and cloud-native technology stack. In addition to code velocity and scale benefits, we also aspired to become a product-centric technology organization that leverages the power of people, process, and technology to bring innovative experiences for customers and frontline employees. Today, as a board member and advisor to enterprise software and technology companies, I see companies of every size attempting to make the rapid shift of applications and infrastructure to the cloud.
Many enterprises are, unfortunately, stuck in the middle, and are forced to navigate between on-prem and cloud ecosystems with a blend of infra-first and cloud-first security models. Authentication technologies like single sign-on and multi-factor authentication are fairly universal now, ensuring people can safely access the resources they need, no matter where they are. Data is migrating to the cloud as well—and quickly—in the form of data lakes and operational data storage. But the tools available to secure that data are lagging behind; they simply don’t meet the needs of the multi-cloud era. And that’s a problem.
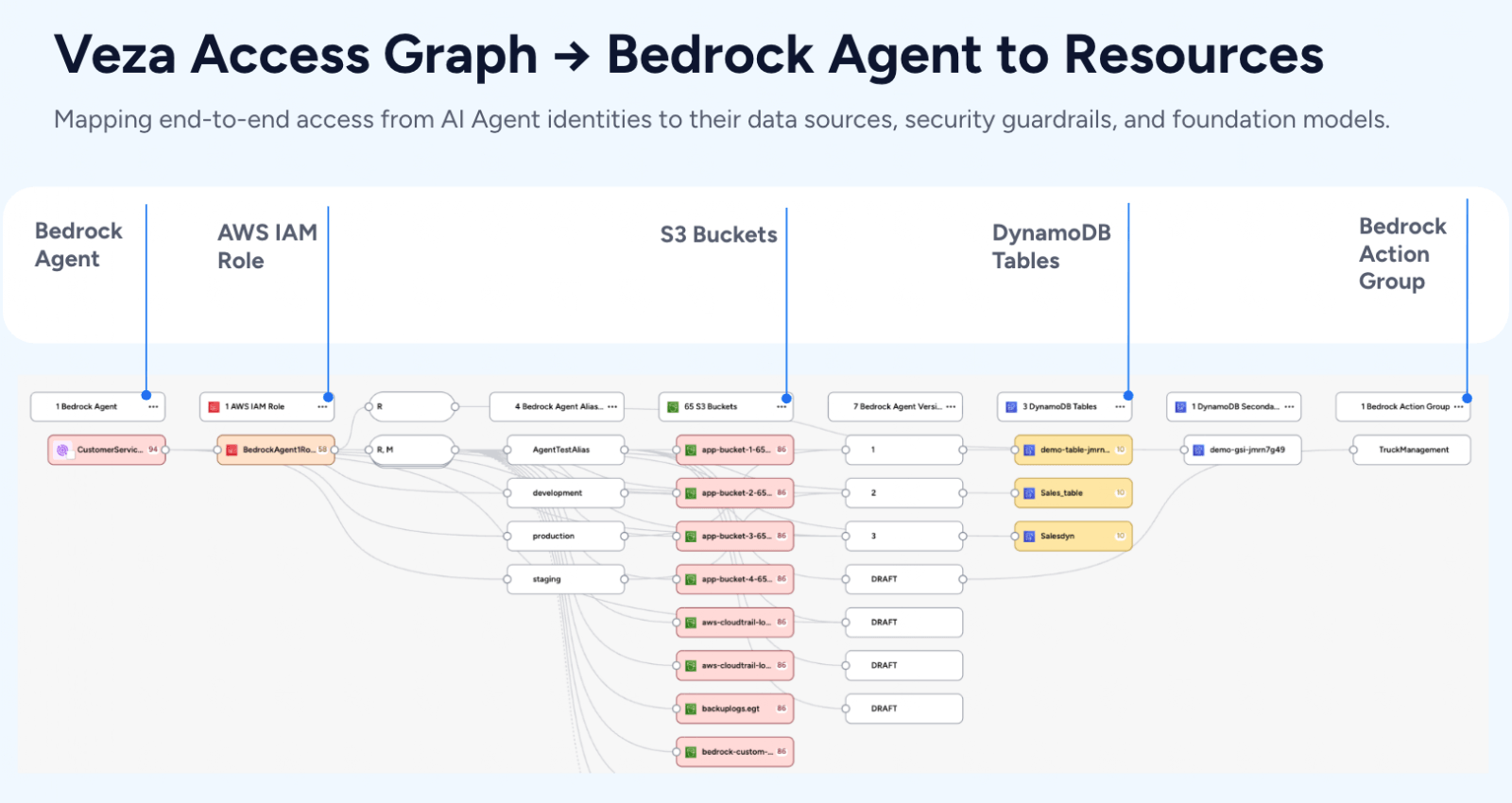
With unprecedented opportunity comes unprecedented risk. Organizations aren’t simply moving to the cloud—many are betting their businesses on it. And data security couldn’t be more critical. In today’s complex, multi-cloud, remote-access world, securing cloud data starts with understanding your effective access rules: beyond what data is stored where and who specifically can access that data – leaders need to control what users are permitted to do with it and under what conditions. That information needs to be intelligently visualized and easily actionable, and this is where authorization makes the difference.
What authorization actually is
Authorization works by defining and securing the specifically allowed interactions between an authenticated user and the enterprise resources that user needs to interact with. With authorizations in place, a typical company might have real permissions that look something like this:
- Anyone in the company can login to Salesforce, but only the Sales, Marketing and Finance teams can download and view confidential reports therein.
- Anyone in the company can log into GitHub, but only authorized developers are permitted to modify source code, and that access is scoped to specific engineering teams.
- Anyone in IT can log into ServiceNow, but only specific users are granted full admin access. Without authorization, ServiceNow users cannot access, view, or interact with information that doesn’t pertain to their specific job function.
Think of authorization as a way for enterprises to intelligently fine-tune access to a resource. First, a user proves their identity through authentication. Then, based on that verified identity, that user gains the access they need to specific, relevant resources via authorization. This allows an organization to carefully restrict access to any and all sensitive data (like customer accounts and PII), so they can support security best principles like managing least privilege, simplifying access entitlement reviews, conducting compliance/audit reports, and a lot more.
Why do you need authorization?
Fine-grained authorization ensures the right information is available only to the specific people who need to access it, only under certain conditions, and only over a specified time span—no more, no less. In our ever-evolving workplace, neither data, nor applications, nor organization structures are static, so authorization must be as dynamic as the environment it protects.
To support the authentication they need, businesses need to examine their current security posture and update to a zero-trust architecture (if they haven’t done so already). Legacy cybersecurity tools can secure information at the network edge with authentication, and that’s a start. But once a user gets past that security checkpoint, corporate systems often allow this authenticated identity to move laterally within the network. And in an age of rampant identity fraud, this kind of easy access can be disastrous. Authorization controls restrict users to the least amount of privilege and movement necessary to do their jobs, and the failure to institute strong authorization controls has contributed to devastating breaches for some of the world’s leading organizations.
Global cybercrime damages are predicted to cost enterprises $10.5 trillion annually by 2025.
Cybercrime Magazine
Upgrade your security posture through authorization
Every CIO and CISO is challenged with controlling data storage, determining access to it, and understanding each user’s ability to interact with information—a monumental task. With strong authorization controls, an enterprise can provide all necessary access, even at scale, while severely limiting every user’s ability to move across platforms where access isn’t necessary or falls outside their scope of work. This way, if authentication is breached by a cybercriminal or bad actor, authorization’s limits on that compromised user’s access and abilities across the system can drastically mitigate the risk and control the damage.
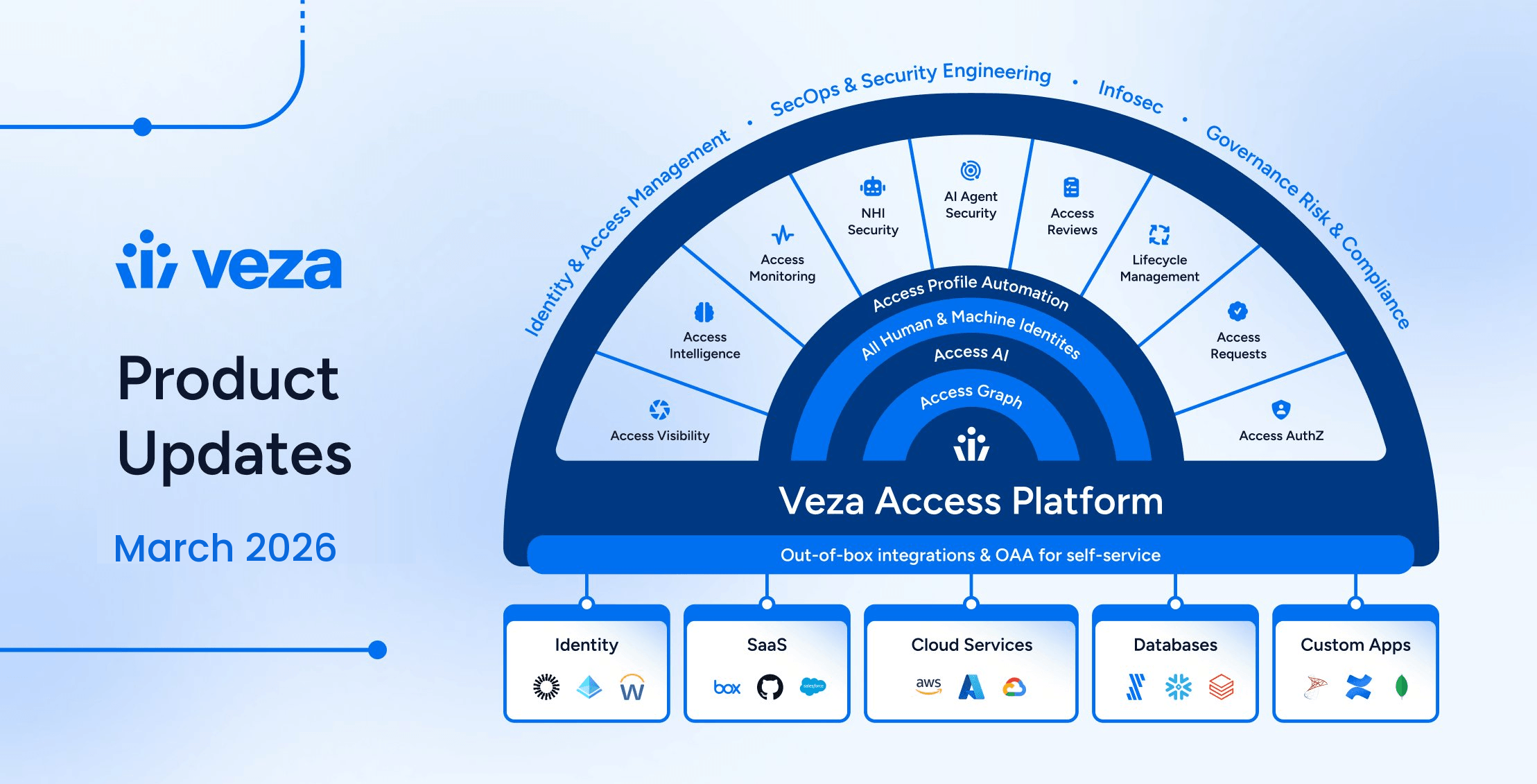
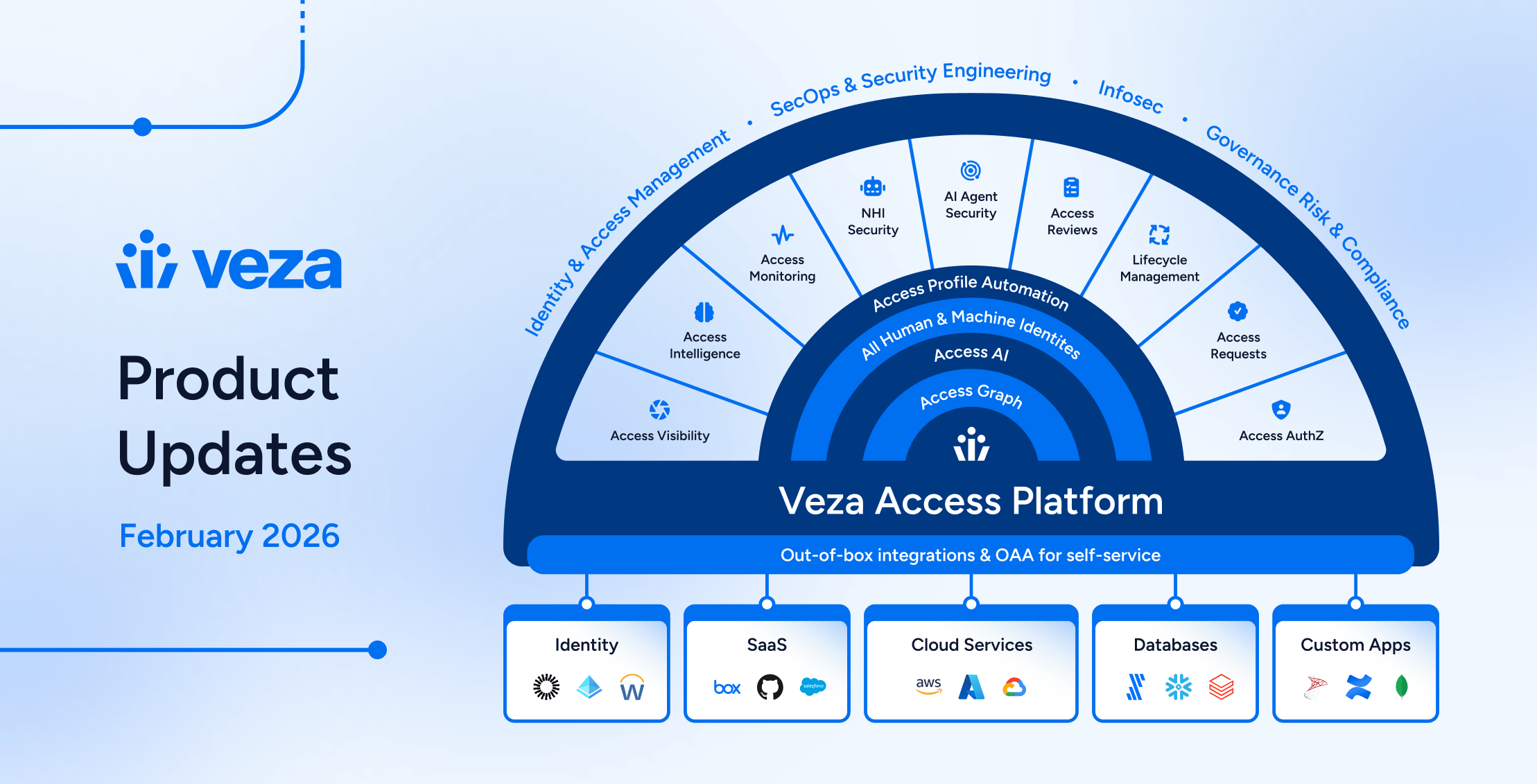
Veza is a first-of-its-kind data security platform that helps organizations establish the end-to-end authorization they need now, in this rapidly unfolding era of multi-cloud data storage and information exchange. Simplifying the daunting complexity of permission structures across different identity providers, IAM tools, apps, and data systems, Veza presents your teams with a complete data access map in a single pane of glass that includes actionable information on how to centrally monitor and universally adjust authorization rules to enforce company policy and best-practices security standards.
With a strong vision and a goal of becoming the standard in modern data security, Veza is just getting started, and I’m excited to watch this company move forward out of stealth and continue to grow its stellar reputation and global enterprise partnerships.