Executive Summary
The recent Treasury Department breach, caused by unauthorized access privileges, highlights the persistent risks organizations face with identity security and access governance. This breach was not the result of an advanced cyberattack but rather stemmed from simple misconfigurations and gaps in access controls. It underscores the urgency for organizations to rethink their identity security practices—moving from traditional, manual approaches to automated, continuous monitoring and granular, permission-level access management.
As identity security professionals, we must adapt to an increasingly complex digital landscape. In this post, I’ll share five critical lessons from the Treasury incident that can help organizations better protect sensitive systems while ensuring necessary access for their workforce. Modern identity platforms are key to providing real-time visibility, automated risk detection, and dynamic governance processes.
The Permission-Group Gap Remains Dangerous
Despite advanced security measures, the Treasury breach was ultimately caused by a misconfiguration in access permissions—granting unintended write access to sensitive payment systems. This highlights a fundamental flaw in relying solely on role-based access control (RBAC). Organizations that base their visibility and decision-making on role and group names (e.g., Sales-Readonly) and their descriptions risk missing the effective permissions actually granted to users—including those inherited through nested roles and groups. Without a deeper, permission-level understanding, critical access risks remain hidden, leaving sensitive assets exposed.
How to Close the Gap
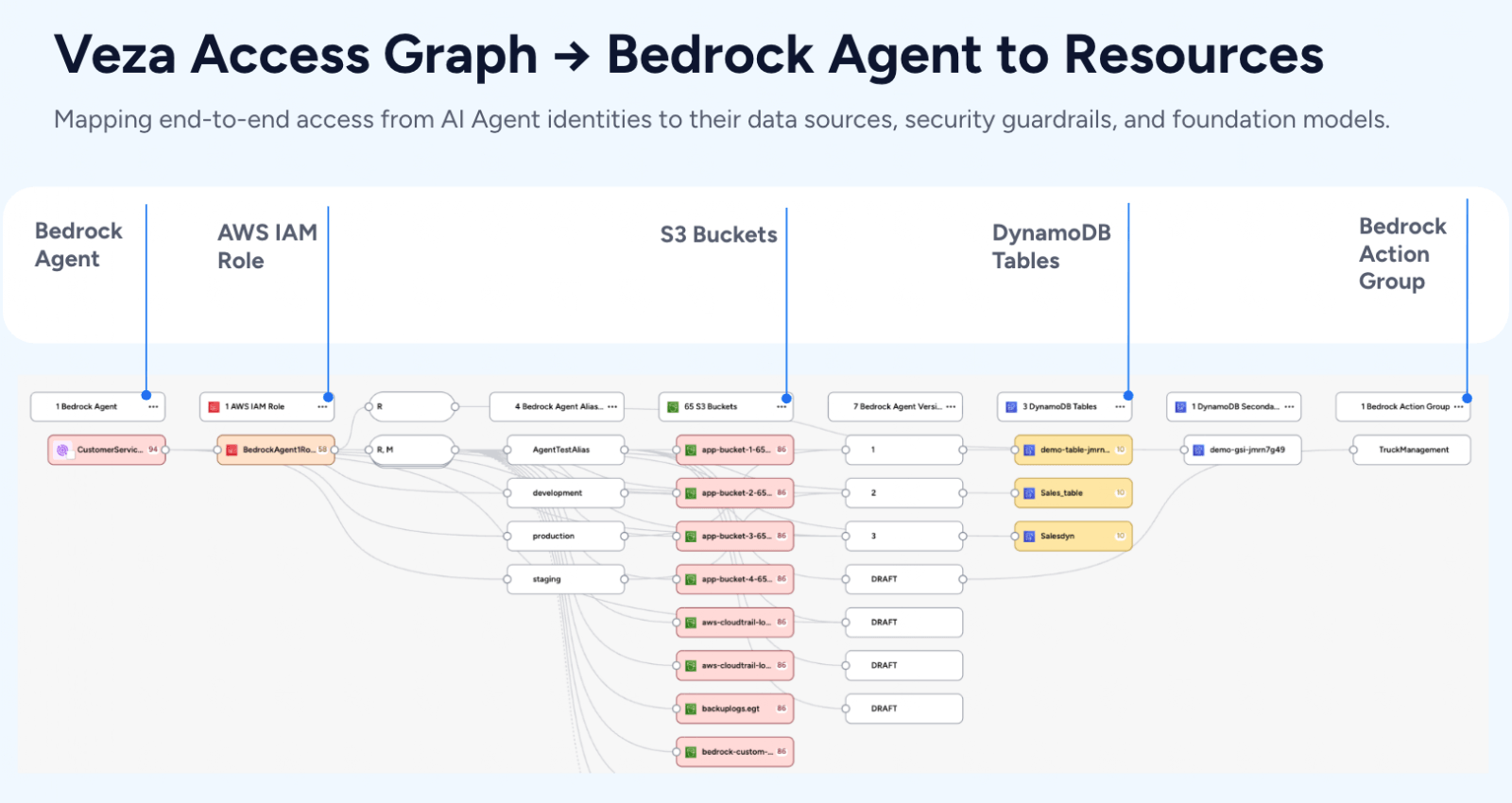
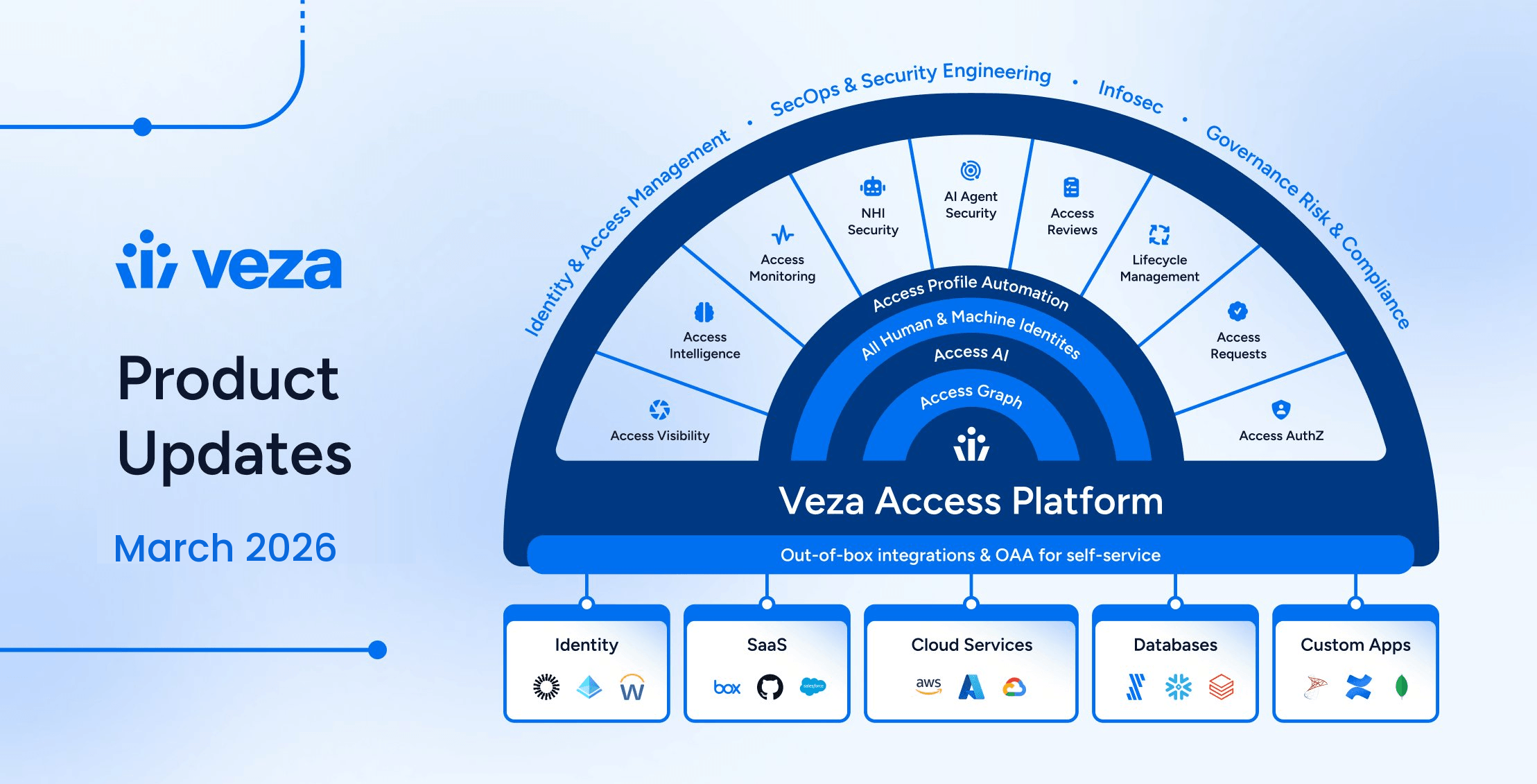
Organizations need more than just a high-level view of group-based access—they need granular, permission-level visibility across all systems. Modern identity security platforms, such as Veza, go beyond simply mapping access; they translate complex permissions into actionable CRUD operations (Create, Read, Update, Delete). This is critical because, while a system like AWS S3 may have over a hundred permissions, what truly matters is who can delete or modify data. By distilling permissions down to what actually impacts security, Veza helps prevent unintended privilege escalation and enables security teams to proactively manage risk rather than react to breaches.
Manual Access Reviews Are No Longer Sufficient
In this incident, unauthorized access wasn’t discovered through an internal review but rather through external scrutiny. This highlights the fundamental flaw of periodic, manual access reviews—they’re outdated before they even begin. Threats evolve in real time, and relying on quarterly or annual reviews creates a dangerous blind spot.
Automating Access Intelligence
Organizations must shift to continuous monitoring and automated anomaly detection to keep up with modern threats. Platforms like Veza enable real-time access intelligence by detecting suspicious changes in permissions, excessive privileges, and unusual access patterns—before they become a breach. Instead of waiting for an audit to catch issues, organizations should deploy risk-based micro-certifications that trigger automated reviews when access patterns deviate from the norm.
Complex Multi-System Environments Require Unified Visibility
The Treasury’s financial systems operate across multiple platforms, databases, and applications, making it difficult to maintain consistent and enforceable access controls. In today’s hybrid environments, where on-prem, cloud, and SaaS solutions intersect, a lack of centralized visibility creates security gaps.
Breaking Down Silos in Identity Security
A unified view of identity and access across all systems is now a requirement, not a luxury. Organizations must consolidate access data into a single, actionable graph to effectively govern permissions. Identity platforms like Veza provide this by mapping every user, permission, and entitlement across cloud, on-prem systems, SaaS, and custom applications in near real-time. This eliminates fragmented oversight, enhances compliance, streamlines audits, and enables security teams to respond to threats with greater precision.
Traditional IAM solutions often focus only on roles and groups within siloed systems, missing hidden access risks across SaaS and custom applications. Veza’s full-stack permission visibility ensures security teams can proactively manage risk, enforce least privilege, and maintain compliance across the entire identity landscape.
Temporary Access Requires Special Attention
In the Treasury incident, a temporary employee was granted elevated privileges for a specific task—but those privileges remained longer than necessary. This is a classic example of how temporary access, if not tightly managed, can become a security risk.
Enforcing Just-in-Time and Expiring Access
Organizations need to enforce just-in-time (JIT) access—ensuring that permissions are granted only when needed and automatically revoked once the task is complete. Additionally, all temporary credentials should have automated expiration policies and be subject to enhanced monitoring and audit logging. With modern identity platforms, these controls can be built-in, reducing human error and the risk of lingering excessive privileges.
Security Controls Must Balance Access and Protection
Even with multiple security layers, the Treasury breach demonstrated how difficult it is to strike the right balance between enabling necessary access and preventing misuse. CISOs often struggle to avoid over-restricting users, which can lead to workarounds—while also ensuring that sensitive data remains tightly controlled.
Implementing Context-Aware Access Policies
The answer lies in context-aware access control, where real-time risk assessment determines access permissions dynamically. Organizations should implement:
- Risk-based authentication, requiring additional verification when high-risk access is detected
- Least-privilege enforcement, automatically limiting access to only what’s necessary
- Real-time access analytics, continuously evaluating user behavior and permissions for anomalies
Platforms like Veza support these capabilities by integrating risk intelligence with dynamic access governance, ensuring that security teams maintain control without disrupting productivity.
Moving Forward: How CISOs Can Take Action Now
The Treasury incident is a cautionary tale for security leaders across industries. To prevent similar breaches, CISOs must move beyond traditional identity governance models and implement modern, automated security controls. Organizations should prioritize:
- Real-time visibility into all identity and access relationships
- Automated anomaly detection to catch risks before they escalate
- Granular permission analysis to prevent misconfigurations
- Dynamic, context-aware access enforcement for enhanced security
- Seamless governance workflows that reduce manual review burdens
Identity security is no longer just a compliance requirement—it is a foundational pillar of operational resilience. With modern identity platforms, organizations can turn identity risk management into a proactive, automated process, reduce attack surfaces, and strengthen security at scale.
Conclusion
The Treasury breach is a clear warning: identity security remains a primary attack vector, and legacy governance methods aren’t keeping up. To stay ahead, CISOs need solutions that provide:
- Continuous visibility into all user entitlements
- Automated governance with proactive risk detection
- Granular permission controls beyond traditional RBAC
Modern identity security is about intelligence, automation, and adaptability. Organizations that embrace this approach will not only reduce risk but also gain agility and resilience in an evolving threat landscape.
Take the Next Step:
Explore how Veza’s Access Platform addresses key identity security challenges, from Privileged Access Monitoring to SaaS Access Security. Learn how leading organizations are securing their environments with a modern, intelligent approach.